[This story was updated to include response from Belkin describing its response to the vulnerabilities identified by IOActive, including firmware updates. – PFR Feb 19, 2014]
A researcher with the respected security firm IOActive says that he has found a number of serious security holes in home automation products from the firm Belkin that could allow remote attackers to use Belkin’s WeMo devices to virtually vandalize connected homes or as a stepping stone to other computers connected on a home network.
In a statement released on Tuesday, IOActive researcher Mike Davis said that his research into Belkin’s WeMo technology found the “devices expose users to several potentially costly threats, from home fires with possible tragic consequences down to the simple waste of electricity.” IOActive provided information on Davis’s research to the US Computer Emergency Readiness Team (CERT), which issued an advisory on the WeMo issues on Tuesday.
Belkin did not reply to requests for comment by e-mail and phone on Tuesday. IOActive said that efforts to contact Belkin regarding the software vulnerabilities were unsuccessful. However, Belkin contested that account of events and said that it released software fixes for the issues in question prior to publication of IOActive’s bulletin and the CERT advisory.
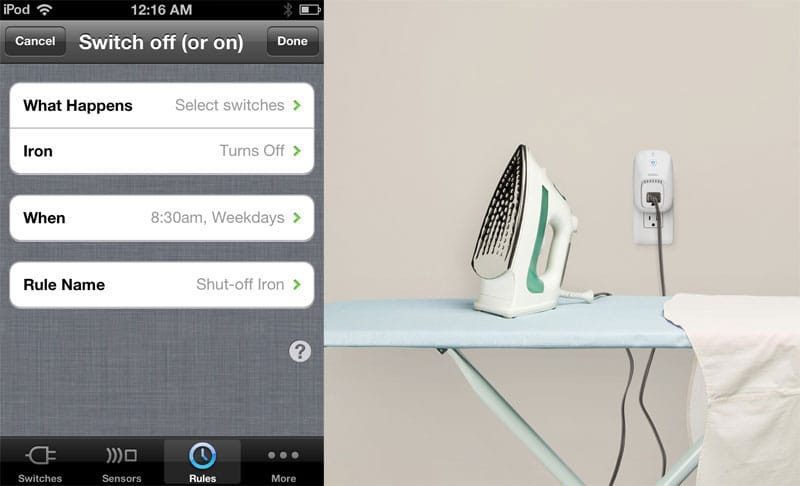
Belkin WeMo is a line of home automation products including wi-fi enabled light switches and plugs that allow home owners to control a wide range of “dumb” devices like lamps and kitchen appliances from the Internet using their computer or mobile device. Belkin partners with home goods makers like Sunbeam and Mr. Coffee to Internet-enable commonly used home appliances.
The problem? Older versions of Belkin’s firmware for the WeMo are signed with public key encryption to protect against unauthorised modifications. Unfortunately, the signing key and password are leaked on the firmware that is already installed on devices, Davis writes. An attacker with physical or logical access to a WeMo device could copy the signing key and password and then use it to sign a malicious software update to run on the device. The valid signature would allow the firmware to bypass security checks during the firmware update process, Davis alleges.
The firmware update problem is just one of a handful of problems Davis discovered. IOActive reports that WeMo devices don’t validate Secure Socket Layer (SSL) certificates used with inbound communications from Belkin’s cloud service. That could allow an attacker to impersonate Belkin’s legitimate cloud service using any valid SSL certificate, potentially pushing a bogus firmware update or malicious RSS feed to deployed WeMo devices.
WeMo customers who are counting on their wireless router and NAT (network address translation) or a firewall to provide cover: beware. Davis found that Belkin has implemented its own, hidden network of WeMo devices by ‘abusing’ a protocol originally designed for use with Voice over Internet Protocol (VoIP) services. With knowledge of the protocol and a ‘secret number’ uniquely identifying the device, an attacker could connect to- and control any WeMo device over the proprietary network. Belkin, Davis says, has “compromised all WeMo devices security by creating a virtual WeMo darknet where all WeMo devices can be connected to directly.”
Finally, Belkin’s WeMo server application programming interface (API) was found to be vulnerable to an XML inclusion vulnerability, which would allow attackers to compromise all WeMo devices.
Belkin says that those holes have been closed. Fixes released by the company include an update to the WeMo API server on November 5, 2013 to close an XML injection vulnerability identified by IOActive and an update to the WeMo firmware, published on January 24, 2014, that ended the practice of storing SSL keys on the device and added SSL encryption and validation to the WeMo firmware distribution feed
“Users with the most recent firmware release (version 3949) are not at risk from these malicious firmware attacks or remote control or monitoring of WeMo devices from unauthorized devices,” the company said in a blog post. Belkin said customers should download the latest version of its mobile application from the iTunes App Store (version 1.4.1) or Google Play Store (version 1.1.2) and then use the updated mobile application to update the device firmware.
The security of Internet connected ‘stuff’ has become a sticking point in the adoption of the so-called “Internet of Things.” Just last week, the US Federal Trade Commission (FTC) approved a settlement with TRENDnet, Inc. over lax security features in its line of SecurView home surveillance cameras, which were found to expose customers to remote snooping.
At an FTC-sponsored forum in November, Commissioner Maureen Ohlhausen said that The Internet of Things has “the potential to transform many fields, including home automation, medicine, and transportation.” However, “the ability to collect large amounts of information and, in some cases, to act on that information also raises important consumer privacy and data security issues.”
Writing on IOActive’s blog yesterday, Davis’s colleague, Cesar Cerrudo said that Internet of Things products such as the WeMo commonly suffer from the exact same kind of software vulnerabilities that have plagued laptop and desktop computers for the last decade. They include sending ssensitive data sent over insecure channels, poor implementation of encryption technology, reliance on hardcoded administrator credentials (or ‘back doors’) and storage of sensitive data in clear text.
Cerrudo blamed the problem on what he termed “data ambition.”
“It seems that many hardware companies are following really poor security practices when adding software to their products and connecting them to the Internet,” he wrote.


The number of vulnerabilities would seem to indicate that security for these devices was a distant thought to Belkin when it was developing them. Are these devices more trustworthy now that Belkin has been ‘caught’? Doubtful since this maker of low margin tech gadgets has no doubt stuffed ‘security’ back in the trunk; at least until the next embarrassing press release.
Pingback: The Geek’s Reading List – Week of February 21th 2014 | thegeeksreadinglist
Pingback: HED: Application Security at RSA: The Coming Storm | Application Security News, Research, Trends – Veracode Blog