China is no stranger to scrutiny for its sophisticated cyber espionage campaigns against the U.S. and its western allies. In fact, many of the earliest identified “APTs” or “Advanced Persistent Threats” are hacking groups associated with China’s People’s Liberation Army or other branches of the Chinese government with a decades-long history of targeting both government and private sector firms.
Over the years, the actions of these groups against U.S. government agencies and firms like Google and Microsoft have garnered lots of attention from Western governments, cybersecurity firms and the Western media outlets alike. That has earned the Chinese threat groups recognition, brands – even swag.
China Green Lights Hacking News
But what about the activity going the other way? What campaigns are the U.S. and its allies carrying out against Chinese state, military and private sector interests? Despite ample evidence that the U.S. and its “Five Eyes” allies have prodigious cyber offensive capabilities, China’s tightly controlled and state run media means that few- if any details of offensive cyber actions targeting the state are matters of public record.
Until now, that is. Increasingly, China’s government is raising public alarms about U.S. hacking campaigns against the Chinese state. However, a report by SentinelOne, China’s Cyber Revenge, finds that the allegations by the Chinese government are just that – with few if any details of the alleged campaigns disclosed to give them credence.
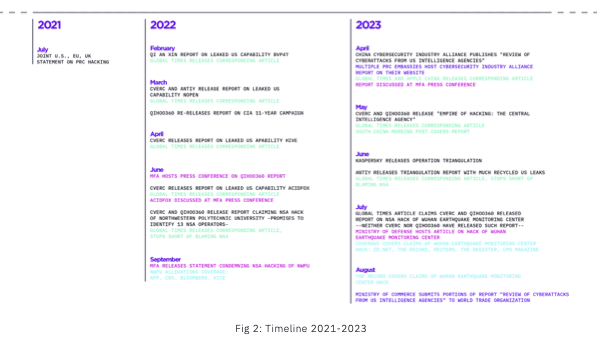
In a report filed Monday, SentinelOne documented the Chinese government’s more aggressive approach to countering stories of Chinese APT campaigns and malicious cyber activity. The company traced the origins of that change in policy to a July, 2021 joint statement condemning China’s cyber offensive activities by the EU, U.S. and UK governments. That statement came in the wake of a PRC cyber campaign targeting widespread flaws in Microsoft’s Exchange messaging platform.
The joint statement, which called out the PRC’s “pattern of irresponsible behavior in cyberspace” as “inconsistent with its stated objective of being seen as a responsible leader in the world.”
The response of China’s government was quick and robust, SentinelOne found. Almost immediately, the Chinese government began downplaying its own hacking activities and capabilities. The Tianfu Cup cybersecurity competition in 2023, for example, saw an iPhone hacking contest eliminate references to the iPhone as a target, referring to “another country’s phone” instead.
Then, starting in early 2022, the government allowed reports by domestic cybersecurity firms to get widespread coverage both domestically and internationally. A February 2022 report by the cybersecurity firm Qi An Xin, for example, analyzed what was declared to be a leaked hacking used by US operators and disclosed by an intelligence leak. That report received robust state media coverage. A corresponding, English-language article on the report appeared in Global Times, which SentinelOne describes as a “nationalist state media outlet.”
The Qi An Xin release became a template for state-media support of reports and stories highlighting foreign cyber offensive campaigns. That includes a March, 2022 statement by the Ministry of Foreign Affairs calling attention to a two year-old report about NSA spying the Chinese firm Qihoo360, SentinelOne said.
China’s National Computer Virus Emergency Response Center (CVERC) kept up the narrative, issuing a report detailing previously leaked US backdoors and tools, like NOPEN, HIVE and ACIDFOX.
China’s Hacking Disclosures: Sunlight, or Shade?
More transparency from governments about hacking incidents is a good thing, generally, and helps raise the level of awareness about cyber risks. The problem? China’s reports about U.S. and western government cyber offensive campaigns are lacking in any details that could affirm their veracity.
For example, a June 2022 report by CVERC and Qihoo360 claimed the NSA’s Office of Tailored Access Operations (aka Equation Group) had penetrated the networks of Northwestern Polytechnical University in China. The authors even claimed to have identified 13 US operators tasked with the mission and promised to reveal their identities, generating interest from western media outlets. However, the report was lacking critical details about the specifics of the attack – including IP addresses associated with the campaign or even dates on which the documented activity occurred.
Likewise, an April 2023 report by the China Cybersecurity Industry Alliance, dubbed a Review of Cyberattacks from US Intelligence Agencies, merely summarized past publications and intelligence leaks, with no new evidence or allegations and most citations from non-PRC vendors.
We’ve been hacked! Details: tbd.
Still, the new approach appears to be working. SentinelOne notes a July, 2023 report cited CVERC and Qihoo360 as claiming the U.S. hacked into seismic censors of the Wuhan Earthquake Monitoring Center, but neither CVERC nor Qihoo360 published the report on their respective websites. Despite the lack of a report or any technical details about the incident, the story was picked up by western news outlets (including Reuters) after the Global Times published a report covering the allegations.
Asymmetric Transparency
The lesson? China is exploiting a kind of transparency asymmetry: floating narratives to offset western claims of Chinese state sponsored hacking with accounts of U.S. state sponsored hacks, but refusing to provide the kinds of supporting evidence and proof that characterizes reports by western firms and governments. By accepting that asymmetry allows the Chinese government to “lie with impunity,” SentinelOne’s report concludes.
The consequences, politically, are serious. “Repeating China’s allegations helps the PRC shape global public opinion of the U.S. China wants to see the world recognize the U.S. as the ’empire of hacking’.” Of course, the U.S. may indeed be the empire of hacking, but to make that case requires proof that China’s government has yet to provide.


Pingback: February 16 | cybersecurity update