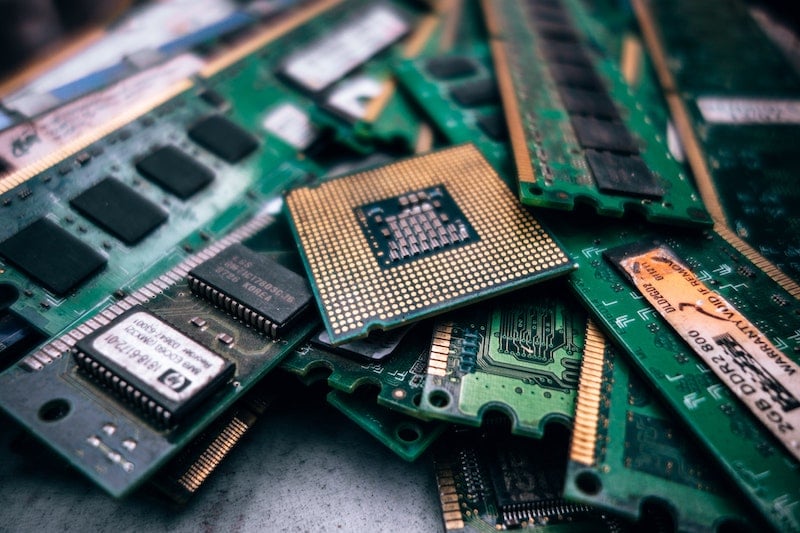
Efforts to wall off sensitive corporate and government data from foreign adversaries have a gaping hole: IT asset disposition (ITAD), where vendors – many owned by Chinese firms – process discarded hardware and data with little oversight.
Tag: hardware
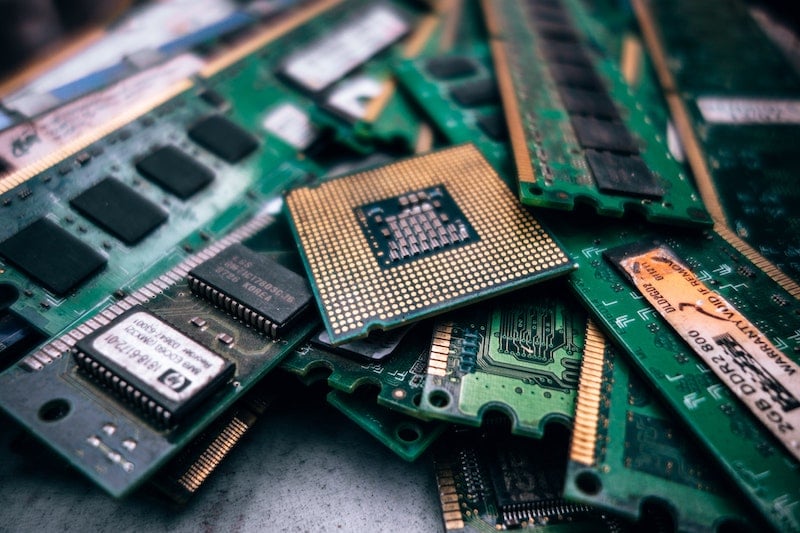
Study finds Chinese Hardware Powers U.S. Voting Machine
A new study by the firm Interos found that many hardware components in a popular touchscreen voting machine used in the U.S. originate in China or Russia.
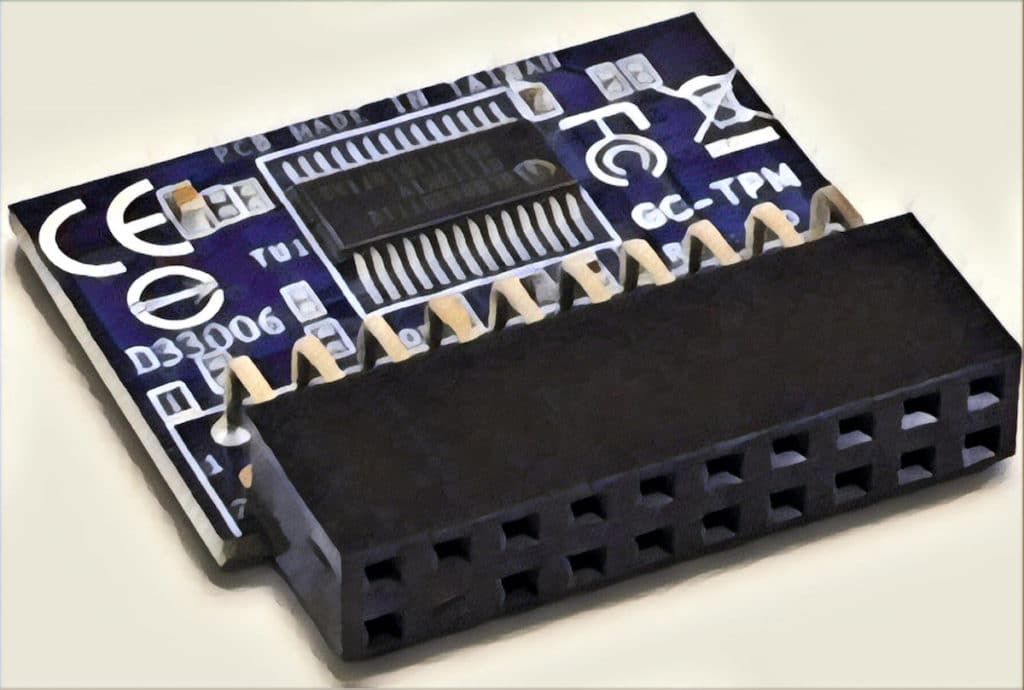
Spotlight Podcast: Two Decades On, Trusted Computing Group tackles IoT Insecurity
In this spotlight edition of the podcast, sponsored by Trusted Computing Group* Steve Hanna joins us to talk about TCG’s 20th anniversary and how the group is tooling up to confront the challenge of securing billions of Internet of Things devices.
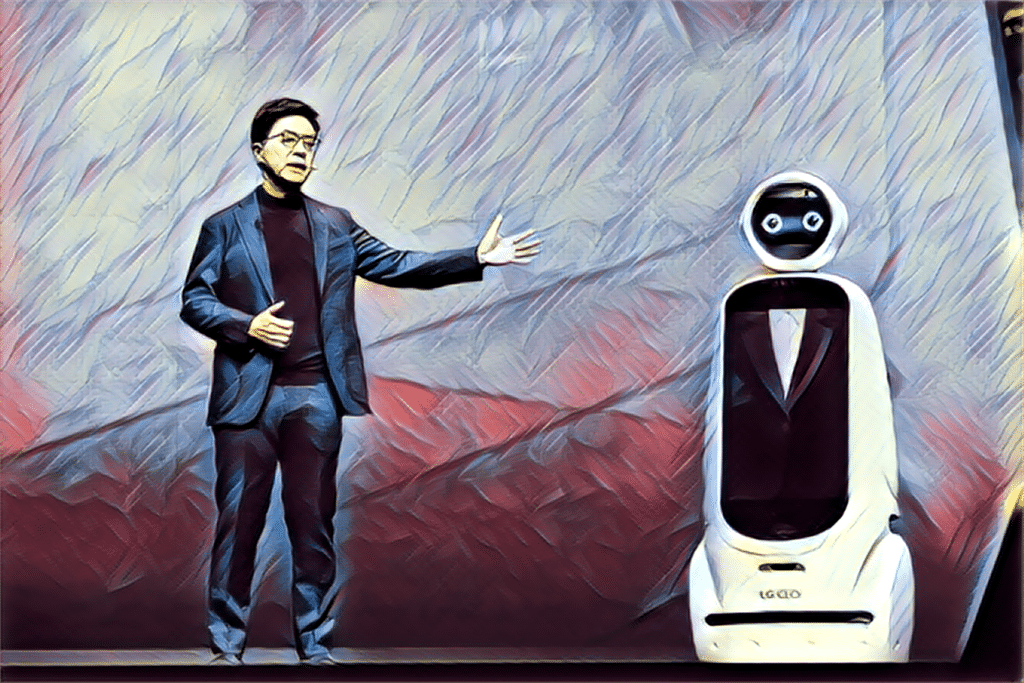
Podcast Episode 129: Repair Eye on the CES Guy and Sensor Insecurity
In this week’s podcast: For all the great new gadgets unveiled in Las Vegas, how many can be repaired? Kyle Wiens of iFixit joins us to report from the CES show. Also: more and more our physical surroundings are populated by small, wireless sensors. How secure are they from hacking and manipulation? Not very says our second guest, Roi Mit of the firm Regulus Cyber.
More Questions as Expert Recreates Chinese Super Micro Hardware Hack
Though the companies named in a blockbuster Bloomberg story have denied that China hacked into Supermicro hardware that shipped to Amazon, Apple and nearly 30 other firms, a recent demonstration at hacking conference in Germany proves the plausibility of the alleged hack.