Podcast: Play in new window | Download (Duration: 25:21 — 29.0MB) | Embed
In this spotlight edition of the podcast, sponsored by Trusted Computing Group* Steve Hanna joins us to talk about TCG’s 20th anniversary and how the group is tooling up to confront the challenge of securing billions of Internet of Things devices.
Twenty years ago, the Trusted Computing Group formed as a consortium of technology vendors concerned about the scourges of viruses and worms, which were then ravaging the still-young Internet.
That’s not unusual. The last two decades has witnessed the formation and then slow, silent deaths of hundreds of similar industry groups. But TCG’s story turned out quite differently. Today, the group counts more than 100 members across industries.

Critical Flaws in VxWorks affect 200 Million Connected Things
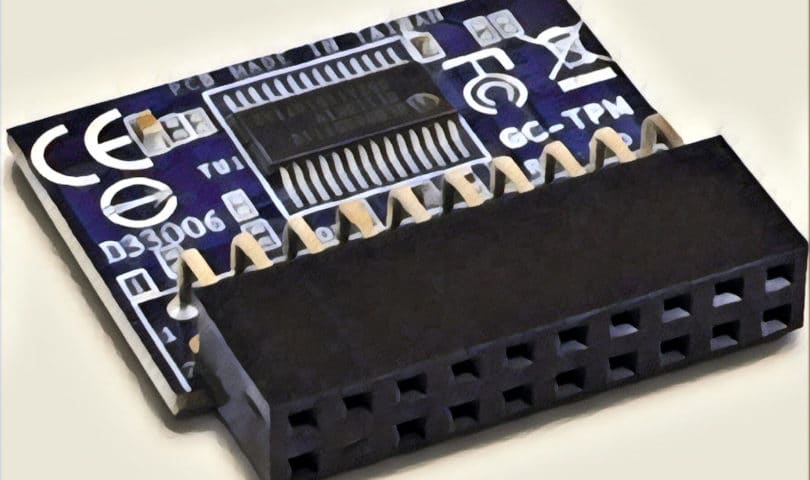
Even more important: the technology it has developed and promoted, including its trusted platform module (or TPM) chips, today power more than a billion devices including virtually all enterprise personal computer, many servers, networking equipment, storage drives and a growing number of embedded systems.
Securing Billions of Devices
But as the second decade of the 21st century draws to a close, TCG faces a monumental challenge: as computing shifts from PCs, laptops and servers to a vast universe of other devices – the Internet of Things.
Spotlight Podcast: Fixing Supply Chain Hacks with Strong Device Identities
As our guest this week, Steve Hanna of Infineon, points out: many of those devices are not suited to run traditional TPM type technologies – because they are too small, too power constrained or both.
In this spotlight podcast, Steve and I talk about how Trusted Computing Group is making the transition to the IoT and bring hardware based roots of trust to a much larger and more diverse population of devices. We also talk about why TCG succeeded when so many other industry consortiums have failed, and how the early backing from the likes of Microsoft and IBM gave Trusted Computing Group technologies a critical boost in the marketplace.
(*) Disclosure: This podcast and blog post were sponsored by Trusted Computing Group. For more information on how Security Ledger works with its sponsors and sponsored content on Security Ledger, check out our About Security Ledger page on sponsorships and sponsor relations.
As always, you can check our full conversation in our latest Security Ledger podcast at Blubrry. You can also listen to it on iTunes and check us out on SoundCloud, Stitcher, Radio Public and more. Also: if you enjoy this podcast, consider signing up to receive it in your email. Just point your web browser to securityledger.com/subscribe to get notified whenever a new podcast is posted.


Pingback: Spotlight Podcast: Building Resilience into the IoT with Rob Spiger | Raymond Tec