Let’s be clear: the natural gas explosions that rocked the Merrimack Valley north of Boston in September weren’t the result of a cyber attack. Unfortunately: well known vulnerabilities affecting the security of remote sensors and industrial control system software mean they easily could have been.
Tag: hardware
Spotlight: as Attacks Mount, how to secure the Industrial Internet
In this spotlight edition* of The Security Ledger Podcast, Steve Hanna of Infineon joins us to talk about the growing risk of cyber attacks on industrial systems and critical infrastructure. “Industry 4.0” is poised to transform the global economy, Hanna said, but not if the issue of cyber risk can’t be managed. We talk about how that might be done and the need for strong identity and hardware based roots of trust!
Podcast Episode 122: will 5G increase Internet of Things Risk?
Telecommunications firms like to talk up all the great things that so-called 5G cellular networks will bring to smart phones. But what new kinds of Internet of Things use cases may become possible? And, just as important, what are the security implications of massively distributed IoT endpoints connected to capacious 5G cellular infrastructure? Jason Ortiz of the cybersecurity services firm Pondurance joins us to talk about the impact of 5G on the IoT.
Podcast Episode 116: Cryptojacking and MikroTik’s Bad-Feeling Feel Good Patch Story
MikroTik is part of a bigger problem: the failure of infrastructure owners to take appropriate action to address serious security holes in products.
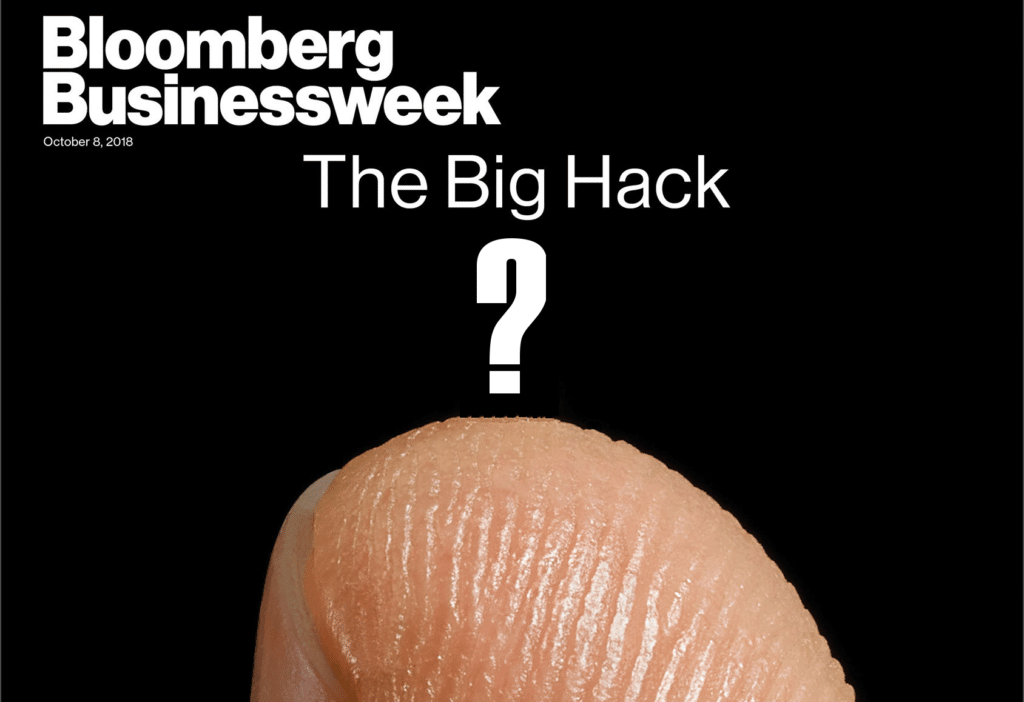
Podcast Episode 115: Joe Grand on Unicorn Spotting and Bloomberg’s Supply Chain Story
In this week’s episode (#115), noted hardware enthusiast and hacker Joe Grand (aka “Kingpin”) told reporters from Bloomberg that finding an in-the-wild supply chain hack implanting malicious hardware on motherboards was akin to witnessing “a unicorn jumping over a rainbow.” They went with their story about just such an attack anyway. Joe joins us in the Security Ledger studios to talk about whether Bloomberg got it right. Also, Adam Meyers of Crowdstrike comes into the studio to talk about the U.S. Department of Justice indictment of seven Russian nationals. Adam talks about the hacks behind the charges and what comes next.