In this week’s episode (#112): top bug hunters can earn more than $1 million a year from “bounties” paid for information on exploitable software holes in common platforms and applications. What does it take to be among the best? We talk with Jason Haddix of the firm Bug Crowd to find out. Also: The Internet Society’s Jeff Wilbur talks about the new #GetIoTSmart campaign to educate device makers and the public about Internet of Things security.
Tag: hardware
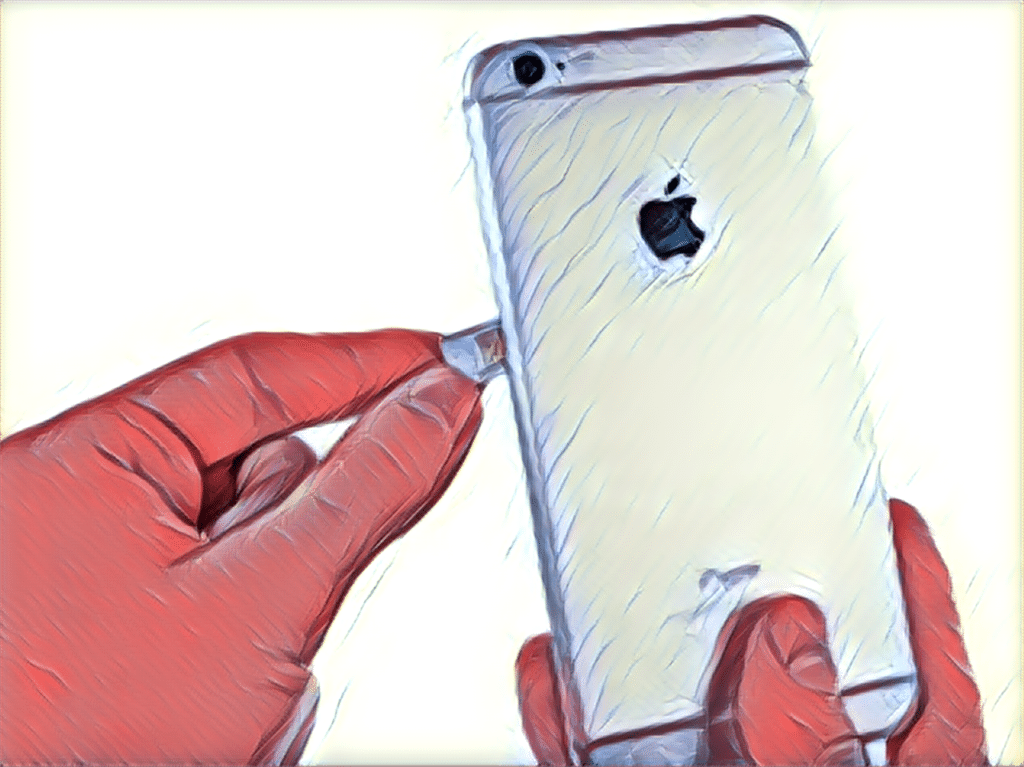
Spotlight Podcast: Flashpoint’s Allison Nixon on SIM Swapping and the Looming Online Identity Crisis
Your smart phone does double and triple duty: letting you do banking, buy a cup of coffee, board a plane or access a sensitive online account. But that doesn’t mean that your phone number is equally as trustworthy. In this Spotlight Podcast, we speak with Flashpoint* head of research Allison Nixon about how a recent rash of SIM swapping attacks highlights a looming crisis in online identity.
Podcast Episode 110: Why Patching Struts isn’t Enough and Hacking Electricity Demand with IoT?
In this week’s episode (#110): the second major flaw in Apache Struts 2 in as many years and has put the information security community on alert. But is this vulnerability as serious as the last, which resulted in the hack of the firm Equifax? We talk with an expert from the firm Synopsys. And: we’ve heard a lot about the risk of cyber attacks on the critical infrastructure used to generate and distribute electricity. But what would happen if someone figured out to how to hack electricity demand? The Internet of Things just might make that possible. We talk to a Princeton University researcher behind a paper that discusses how even small changes in demand can have big consequences for the grid.
McAfee Researchers Exploit Smart Plug to attack Smart TV!
Researchers from McAfee have demonstrated how a flaw in a Belkin smart switch can be used to access other connected devices on the same network as the switch.
From Mainframes to Connected Cars: How Software drives the Automotive Industry
Automakers must pay as much attention to the integrity and security of the software running modern vehicles as they pay to areas such as metallurgy, impact protection, seat belts, and materials science argues Gary Mcgraw, the Vice President of Security Technology at the firm Synopsis.