In-brief: Two days after the site Wikileaks dumped thousands of pages of information about covert CIA hacking tool, the security and technology communities have weighed in. Their verdict? Meh.
Amid all the hoopla about the Wikileaks dump of hacking tools used by the U.S. Central Intelligence Agency, one salient point has been lost: many of the leaked tools weren’t that new or that powerful.
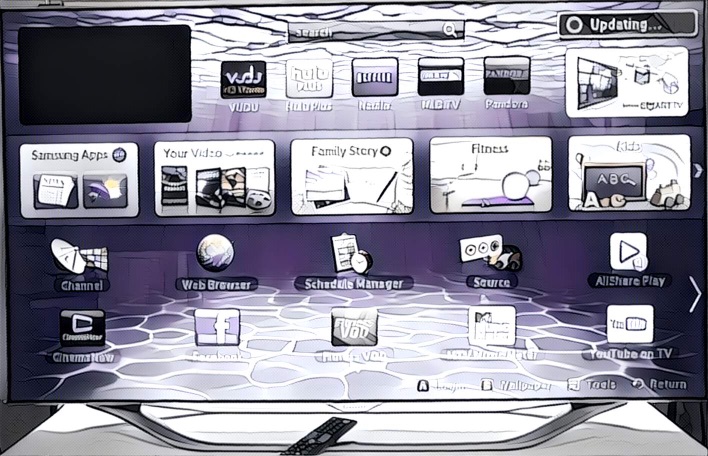
The data dump known as Vault7 included tools for hacking Samsung Television sets and software from Google, Apple and Microsoft often targeted known vulnerabilities in those products. In many cases, the holes had already been patched by the vendor. In other cases, attacks were only possible with direct physical access to the targeted device, greatly reducing the usefulness of the hacking tool, security researchers say.
Take “Weeping Angel” – one of the CIA tools that attracted the most press, because it targeted Samsung model smart television sets. As Security Ledger noted, Weeping Angel enabled CIA operatives to make the sets look as if they were powered down, even while the embedded microphone continued to record and send captured, ambient audio clips to a cloud-based server controlled by the Agency.
That’s pretty crafty stuff. (CIA agents devised a way to trick Samsung’s update feature and disable the LED lights indicating the set was “on”.) But security researchers at the firm Pen Test Partners noted that they had warned that the Samsung smart TVs appeared to be snooping on owners via a voice recognition feature, and sending captured voice data off to the cloud unencrypted. In fact, the group created a listening application, similar in concept to Weeping Angel, which they demonstrated for the BBC. (Interesting, especially because the Weeping Angel tool seems to have been adapted from one created by the UK’s MI5 spy agency.)
Even more important: Weeping Angel had no proper software “dropper.” In other words, CIA operatives would have to install it by hand using a USB drive or other means, Jamison Utter of the firm Senrio told The Security Ledger. That requirement greatly reduces the potency of the tool. Another limitation, Pen Test Partners notes, is that Weeping Angel relies on Wi-Fi to send audio out, meaning the CIA would need to set up their own, local wi-fi network to receive the transmitted audio. Again: another obstacle to deployment.
OK. Well, what about all the other tools for use against Apple’s iOS, Google’s Android and Microsoft’s Windows? In many cases, the so-called “zero day” vulnerabilities exploited by the tools have already been fixed. Apple said in a statement that it has addressed many of the vulnerabilities targeted by the CIA tools. In a statement to the web site TechCrunch, an Apple spokesperson said that the company’s “initial analysis indicates that many of the issues leaked today were already patched in the latest iOS.” But the company said that it is working to “rapidly address any identified vulnerabilities.”
Google said the same was true of its Android and Chrome operating systems. “As we’ve reviewed the documents, we’re confident that security updates and protections in both Chrome and Android already shield users from many of these alleged vulnerabilities,” Heather Adkins, Google’s Director of Information Security and Privacy, told the web site ReCode. “Our analysis is ongoing and we will implement any further necessary protections. We’ve always made security a top priority and we continue to invest in our defenses.”
So what to make of the tools? Security experts tell The Security Ledger that the notes leaked by Wikileaks (the group has not released the actual hacking tools so far) look like run of the mill offensive cyber weapons that any intelligence agency might use to gain a foothold on a target network or endpoint.
The CIA seemed to back up that conclusion itself. “It is CIA’s job to be innovative, cutting edge, and the first line of defense in protecting this country from enemies abroad,” Jonathan Liu, a CIA spokesman said in a statement. “America deserves nothing less.”
The Vault 7 releases seems destined to amount too much less than the 2013 leaks by NSA contractor Edward Snowden, which revealed a system of global, online surveillance that was breathtaking in scope and comprised operations ranging from global electronic surveillance of communications to bugging the mobile phones of world leaders, including some of the U.S.’s closest allies, to a program of interdiction that placed spy agency tools on networking equipment sold by U.S. firms.
“We find the documents mostly confirm existing knowledge about how common hacking is and how many potential targets there are in the world,” wrote researchers Richard Forno and Anupam Joshi of The University of Maryland. If anything, the two said, the Vault7 documents “reinforces perhaps the most troubling piece of information we already knew: Individuals (sp) and the government itself must step up cyberdefense (sp) efforts to protect sensitive information.”

Pingback: The Security Ledger
Pingback: Podcast: CIA Hacking Tools, Our Orwellian Internet of Things & G-Men can subpoena Memories? | The Security Ledger