Host Paul Roberts speaks with Marc Blackmer of ShardSecure about that company’s new approach to protecting data at rest, which relies on fragmenting and scattering data to make it impossible to steal.
Tag: encryption
How NIST Is Securing The Quantum Era
Quantum computers powerful enough to break the strongest classical encryption are at least a decade away, but the time to develop quantum safe encryption is now. In this opinion piece, Thomas Pöppelmann, a Senior Staff Engineer, Security Architecture and Cryptography Research at Infineon Technologies talks about the steps NIST and companies like Infineon are taking to make that happen.
IT Preps for Post Quantum Crypto (Whatever That Means)
Practical quantum computing isn’t here yet. But a new survey by Digicert suggests that isn’t stopping IT pros from prepping for a post-quantum reality…even if they aren’t exactly sure what that means.
Spotlight Podcast: Unpacking Black Hat Hacks with Digicert CTO Dan Timpson
In this Spotlight Podcast, we broadcast from the Black Hat Briefings in Las Vegas Nevada. Dan Timpson, the Chief Technology Officer at DigiCert joins us to talk about some of the high profile hacks at this week’s “hacker summer camp” and the common weaknesses and security lapses that are common to all of them.
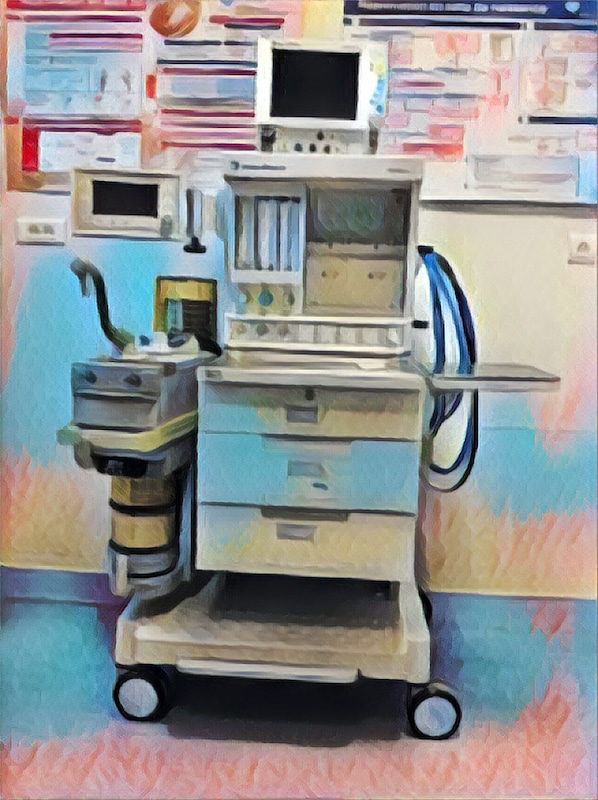
Breathe Deeply: DHS warns of Flaw in Hospital Anesthesia Machines
GE learned of a serious vulnerability affecting two brands of anesthesia machines in October. The company on Tuesday advised customers to take steps to protect them from being remotely tampered with.