The German magazine Der Spiegel made headlines this week with its story detailing the US National Security Agency’s (NSAs) offensive hacking capabilities. The story is based on classified NSA documents absconded with by former contractor Edward Snowden and lays bare a Webster’s Dictionary full of classified hacking tools and programs.

Among the highlights of the story:
+ The NSA developed and deployed a wide range of hacking tools that could compromise hardware from leading IT and networking equipment makers including Cisco Systems, Juniper Networks and the Chinese vendor Huawei and Dell Inc.
+ The NSA tools were designed to provide persistent access that allowed the NSA to monitor activity on the compromised endpoint, avoid detection by third party security software and survive software and firmware updates. One such tool, DEITYBOUNCE, provided persistent access to Dell’s PowerEdge servers by “exploiting the system BIOS” and using “System Management Mode to gain periodic execution while the operating system loads.”
+ NSA concentrated hacking operations in units with names like “TAO” (for Tactical Access Operations”) and “ANT,” which developed tools to compromise and gain control over a wide range of technology products.
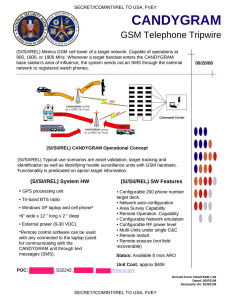
+ The tools were catalogued in a 50 page product manual with associated costs for each intelligence product ranging from $0 for “MONKEYCALENDAR,” a software implant for SIM cards for GSM phones that pulls geolocation data from the phone and sends it via SMS to an NSA -controlled phone, to $40,000 for “CANDYGRAM” a device that can mimic a GSM tower on a target network.
+ Many NSA tools could be deployed remotely, over the Internet, using “phishing” and social engineering techniques common to cyber criminal groups. Others, however, required “interdiction” by an NSA operative, using malware installed via USB or other means.
The revelations are just the latest to spill from the trove of documents and other classified information taken by Snowden, who now lives in Russia. The companies involved have all denied knowledge of the Spy Agency’s work with their technology. The revelations prompted at least one affected firm, Cisco Systems, to say that it was “deeply concerned” about the allegations that the NSA developed tools capable of compromising the security of Cisco products.
“We are committed to avoiding security issues in our products, and handling issues professionally when they arise,” Cisco Chief Security Officer John Chambers wrote in a blog post on Monday. “We do not work with any government to weaken our products for exploitation, nor to implement any so-called security ‘back doors’ in our products.”
