
In-brief: Software security holes in widely used industrial equipment known as “power quality analysers” (sp) could enable remote attackers to disrupt or corrupt operations at firms across industries, according to a report released by the firm Applied Risk.
Software security holes in widely used industrial equipment known as “power quality analysers” (sp) could enable remote attackers to disrupt or corrupt operations at energy and manufacturing firms, among others, according to a report released by the firm Applied Risk.
The firm found that software and hardware from the German firm Janitza Electronics GmbH contained a wide range of security weaknesses that make the products easy prey for malicious hackers. A remote attacker with knowledge of the holes could take “full control of” a vulnerable device, adjusting system parameters, manipulating measurement values or changing the function of the device and other systems dependent on it, Applied Risk warned.
Janitza UMB models 508, 509, 511, 604, and 605 Power Analysers were tested and found to be vulnerable. The Department of Homeland Security issued a security advisory about the issues on October 22. Janitza has produced new firmware to mitigate the holes, DHS said.
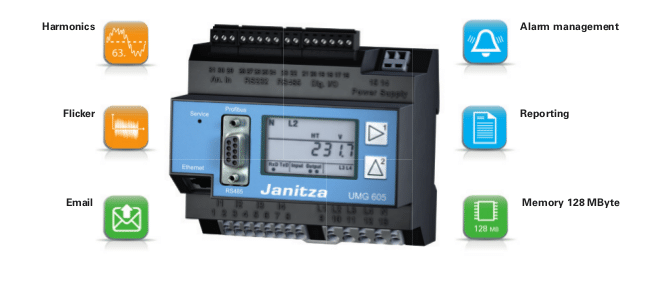
Janitza’s UMG line of power analyzers are used across many industries for power quality monitoring and to spot and analyze electrical disturbances that can interfere with the operation of industrial equipment. The devices are also capable of acting as Ethernet and Modbus gateways for subordinate measurement devices and can send alerts and warnings via e-mail or through a graphical management interface.
But the products also suffer from a variety of security woes that have been found to be common within the industrial control space. Among them: weak authentication controls including the ability to bypass authentication entirely, as well as cross site scripting and other common web application flaws.
Most critically, Applied Risk found that the UMG device’s web interface is unprotected. “A password can be configured, but is limited to a 4-digit value PIN. No controls are in place to prevent PIN guessing, which makes it trivial to guess a valid PIN by trying all possible combinations,” the company wrote.
[Read more Security Ledger coverage of critical infrastructure security here.]
Additionally, Janitza UMG devices studied by Applied Risk were found to expose an FTP (file transfer protocol) interface used by the product’s management suite. The FTP interface is protected with a default password that cannot be changed – a serious and trivially exploitable hole. “Once logged an attacker is able to upload and download arbitrary files, including JASIC program logic to modify the device’s behavior (e.g. controlling switch outputs).
Session tokens generated by the Janitza software were easily predictable – a unique value created by combining the 4 digit PIN with a server generated challenge. Intercepting an even small sample set of session tokens could result in recovery of the PIN due to the limited key space of both the session token and the PIN, Applied Innovation warned. (Assuming brute forcing the 4 digit PIN wasn’t possible.)
There were other issues as well, including persistent cross site scripting vulnerabilities in the UMB’s web interface, which is used to view output and reports.
In its alert, DHS’s Industrial Control System CERT (ICS-CERT) recommended upgrading affected devices to the latest version of the Janitza firmware to address some of the issues identified by Applied Risk, while also reviewing company documentation for how to secure TCP/IP connections to UMG devices.
Other mitigations include blocking remote access to TCP port 1239 and UDP ports 1234 and 1235, using network segregation to isolate the UMG device from other, sensitive assets and deploying firewalls and IDS/IPS technologies to secure networks on which the power analyzers are deployed.
Security issues affecting critical infrastructure are well known and run-of-the mill equipment used across industries is often a target of attack. Experts warn that nation-state actors are taking advantage of the technology weaknesses to compromise critical assets in areas like energy and power distribution.
In March, for example, DHS’s Industrial Control System Cyber Emergency Response Team (ICS-CERT) reported on incident response and vulnerability coordination in 2014. Among the 245 incidents reported were malware infections on “air-gapped control system networks,” strategic compromises of so-called “watering hole” web sites and the use of previously unknown or “zero day” vulnerabilities in industrial control system software.
DHS found 55% involved APT or sophisticated actors. Hactivists, malicious insiders and cyber criminals were behind other incidents. In many other cases, asset owners were unable to determine who or what was attacking them, the report said.

Pingback: Password Shaming: SCADA Password Dump Intended to Improve Security | The Security Ledger