The White House’s cyber security czar, Michael Daniel, said the Obama Administration is deeply concerned about the reported hack of systems belonging to banking giant JP Morgan Chase & Co. but sees the incident as part of a larger trend of attacks against U.S. critical infrastructure.

Asked about the targeted attack against JP Morgan and other banks and financial institutions, Daniel said that the White House was concerned, but not surprised by the incident.
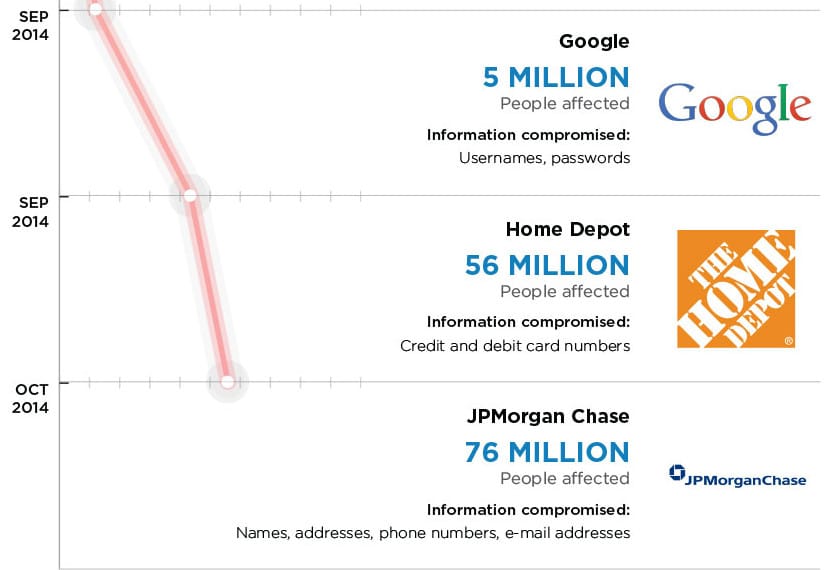
“We have watched for several years the trend of malicious actors in cyber try to figure out how to target critical infrastructure,” he said. “Financial services is critical infrastructure.” The White House was concerned that a major U.S. bank would fall victim to hackers, but sees it in the context of a “broad trend,” rather than an isolated incident, he said.
Speaking with Michael Farrell, the Cybersecurity Editor at Christian Science Monitor, Daniel hit on many of the now-common talking points of the Obama Administration. He trumpeted the need for public-private partnerships to improve the security of software as part of the development process. And he said security needs to become more transparent and less labor intensive – envisioning a kind of autonomic security system.
“We need networks with the equivalent of T and B cells that hunt intruders in your body,” he said.
Daniel promoted government efforts like the NIST Cybersecurity Framework, but balked when asked if the government should push beyond cooperation with industry and mandate better software security.
“We believe that it can remain voluntary and be effective,” he said. “We have a long history of voluntary frameworks being effective.”
Daniel has been a subject of controversy in recent months following an interview in August in which he appeared to trumpet his lack of a technical background.
“Being too down int he weeds at a technical level could actually be a little bit of a distraction,” Daniel said in an interview with the Information Security Media Group. That opinion drew the ire of technology and security professionals who saw it as dismissive of the information security profession.
Speaking on Thursday, Daniel was contrite – grouping his ill-advised opining with a long tradition of self inflicted political wounds in the doldrums of August. The bigger point, he said, was that cyber security was a multi-disciplinary problem requiring both human and technical skills. That’s especially true in the halls of power in Washington D.C., where getting bills passed has little correlation with one’s authority as an expert.

That said, Daniel was decidedly pessimistic about the Obama Administration’s chances of seeing substantive cyber security legislation passed in this term.
“We’re heavily involved with the committees with jurisdiction in both the House and the Senate,” he said. “We’re hoping to make improvements and get to a place where we have something that can pass both houses and be signed by the President.” However, passing legislation of any kind in the current political environment is a Herculean challenge, he admitted. “We remain committed to doing that. But getting anything past Capitol Hill these days is a challenge. We remain engaged.”
lassBroad trends: Internet of Things that has already arrived. Thermostat, coffee maker, refrigerator threat vector in cyber terms. We thought cyber in world of wired desktops was hard. Now going to do it in world of Big Data mobile cloud. We’ve also watched malicious actors willing to move up the threat spectrum. Now not just do digita
the attack on JP Morgan is the White House Cybersecurity Coordinator and Special Assistant to the President. was speaking in Washington D.C. at an event hosted by The Christian Science Monitor and The Center for National Policy