If you’re working in IT at a Fortune 500 firm, Cisco Systems has some unwelcome news: you have a malware problem.
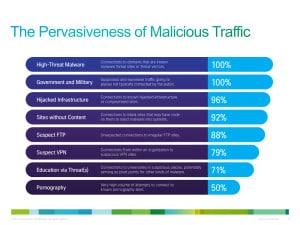
According to the 2013 Annual Security Report from the networking giant, 100 percent of 30 Fortune 500 firms it surveyed sent traffic to Web sites that host malware. Ninety-six percent of those networks communicated with hijacked servers operated by cyber criminals or other malicious actors and 92 percent transmitted traffic to Web pages without content, which typically host malicious activity.
“It was surprising that it was 100 percent, but we know that it’s not if you’re going to be compromised, but when,” said Levi Gundert, a technical lead in Cisco’s Threat Research, Analysis and Communications (TRAC) group in an interview with The Security Ledger.
Among the high points (or low points) in Cisco’s Report:
- Cisco observed the highest number of vulnerabilities and threats on its Intellishield alert service in the 13 years since it launched.
- Measures of other kinds of attacks, including distributed denial of service (DDoS) attacks also went up in 2013
- Organizations wishing to address security issues will have to contend with a dire shortage of trained cyber security experts. Cisco estimates that there is a global shortage of up to one million more cyber security experts in 2014.
Cisco’s report taps data from its Intellishield database, which tracks both vulnerabilities and threats. That database recorded a big jump both in the number of new vulnerabilities and new threats compared with 2012 and prior years, Cisco said.

Cisco said that malicious attackers changed the rules of the game in the last year – harnessing core technology platforms and Internet infrastructure to carry out attacks that were pervasive, difficult to track and highly effective.
“The trust model has been shaken in 2013,” said Gundert. “We trust web browsers, our email clients…or that we can open Adobe PDFs or that a web server is trustworthy.” That was turned on its head in 2013, as malicious actors shifted from pushing threats to victims, to compromising infrastructure and platforms that Internet users interact with on a daily basis, he said.
Nothing was more illustrative of that than the shift to Java based attacks in 2013. Compromises of Oracle’s Java accounted for 91 percent of all compromises detected by Cisco in 2013, dwarfing exploits of other platforms like Adobe Reader (3%) and Microsoft’s Excel (3%).
“When you’re talking about the application layer and what is being compromised it’s Java,” said Gundert. That’s a big change from two or three years ago, when attackers were focusing their attention on Adobe Reader.
During 2013, new malware like DarkLeach showed malicious actors taking advantage of cloud resources to launch attacks, while also introducing sophisticated features to make it difficult for security researchers to locate the source of attacks or even reproduce attacks.
The harnessing of core Internet infrastructure and the cloud greatly increased the availability of malicious resources while also complicating attribution within a diversified and disaggregated cloud hosting marketplace, Gundert said.
Even sophisticated firms had difficulty keeping malicious actors at bay. Cisco’s TRAC team surveyed activity 30 of the larger Fortune 500 firms and found evidence of malicious activity emanating from each of them, including outbound traffic to known malicious infrastructure, traffic to government and military-operated sites not typically accessed from the public Internet, traffic to infrastructure that is known to have been compromised, and connections to suspicious FTP and VPN servers.
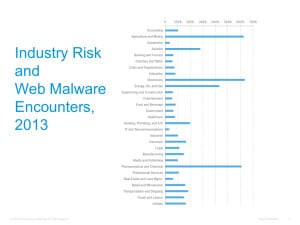
Attacks were spread across a number of verticals, with big year-over-year jumps in verticals like the Chemicals industry, Pharmaceuticals as well as Agriculture and Mining.
Some of that jump is linked to targeted attacks against industry verticals that may be linked to larger geo-political conflicts, Gundert said. At least some of those are believed to be nation-state sponsored attacks that use “watering hole” techniques to compromise the intended victims on sites they are known to frequent.
Fighting off future threats won’t be easy. Cisco foresees dire shortage of expertise in areas like security architecture, incident response and threat intelligence.
“Those are three areas in security that have niche skill sets. And those are the areas where all organizations are going to feel the pinch of the skills shortage,” he said. Without staff who can think like an attacker and use that knowledge to implement policies, procedures and architecture to thwart attacks, enterprises are likely to be caught unprepared for novel and even routine attacks.

Pingback: Cisco Survey: 100% of Fortune 500 Hosting Malware? | Beat the rich