Factory-installed and even aftermarket identity management applications may soon be standard components on automobiles, as the federal government looks for ways to leverage automation and collision avoidance technology to make the country’s highways and roadways safer.
That’s the conclusion of a new report from the Government Accountability Office (GAO), which finds that vehicle to vehicle communications are poised to take off, but that significant security and privacy challenges must first be met, identity management top among them.
The report, GAO 14-13 (PDF available here) takes the measure of what the GAO calls “Intelligent Transportation Systems,” including vehicle-to-vehicle (or V2V) technology. The GAO found that V2V technology that allows automobiles to communicate with each other in ways that can prevent accidents has advanced considerably in recent years.
Automakers, working with the Department of Transportation, are testing the technology in real-world scenarios. However, the deployment of V2V technologies faces a number of challenges, with security chief among them, GAO found. The Government’s watchdog agency reviewed documentation on V2V technology-including related efforts by DOT and automobile manufacturers. GAO staff also visited a pilot study of V2V technology that is being conducted in Michigan. Automobile executives were interviewed, as were subject experts on V2V technology as part of the review.
You might also like “When Autonomous Vehicles Crash, Is the Software Liable?”
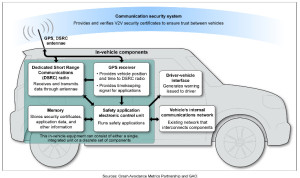
GAO said the auto industry and regulators still need to agree on a technical framework and management framework that will constitute a V2V communication security system. Among other things, the DOT needs to make sure that V2V radio-frequency communications will not be interrupted by other radio devices operating in adjacent parts of the radio frequency (RF) spectrum. Automobiles will also need what GAO called an “external communication security system” that will “ensure that data being transmitted among vehicles are secure and trusted and have not been altered in the transmission process.”
The GAO said research by the DOT is looking at public-key infrastructure (PKI) deployments that would allow automobiles to authenticate to each other and ensure that the data being transmitted has not been tampered with. Vehicles would receive certificates from a security certificate management authority.
GAO quotes officials at one auto industry consortium known as “CAMP VSC 3,” which includes Ford Motor Company, GM, Honda and Mercedes, saying that the security system will need to be able to detect “misbehaving devices—such as devices that are malfunctioning, used maliciously, or hacked,” then “automatically revoke certificates from vehicles with such devices.”
That sounds an awful lot like the enterprise technology known as “Network Access Control,” or “NAC,” in which endpoints are assessed against a variety of criteria (patch level, presence of malware, location, etc.) before being granted permission to communicate with other nodes on a LAN or WAN. So, NAC for cars? Maybe. And maybe not. GAO said the specifics of any kind of in-automobile NAC or Identity and Access Management (IAM) technology are still on the drawing board.
The “technical specifications of how certificates will be provided, how often they will be validated, and who will manage this system have not yet been fully defined, “ GAO found. Beyond that, a trial of a prototype security system revealed the need for “additional enhancements” before it could be deployed on roadways. The DOT has invested heavily in “connected vehicle” and “intelligent roadway” technologies in the last decade. From 2003 through 2012, the DOT funded 12 research programs as part of its Intelligent Transportation Systems (ITS) program totaling around $445 million, GAO said. The government has also expressed concerns about the potential misuse or misapplication of connected vehicle technology by automakers.
In May, David Strickland, the chief Administrator for the National Highway Traffic Safety Administration (NHTSA) told Congress that more research into “vehicle cyber security” is needed to address the threats to a coming generation of networked automobiles that connect to the public Internet and to each other. The agency requested $2 million in the 2014 budget to research “vehicle electronics and emerging technologies” with an eye to developing requirements for the safety and reliability of vehicle controls. But the identity problem may be even more critical.
In August, hackers at the DEFCON hacking conference demonstrated methods for attacking remote sensors used in collision avoidance systems, inducing erratic or even dangerous behaviors in late-model automobiles.
In an article on Forbes.com this week, Patrick Moorhead, an independent analyst pegged identity and privacy as key issues for what he called the “Human Internet of Things” (or HIoT), an “emerging set of ‘greenfield’ services and technologies” that include applications like “quantifiable self” and “automated home” systems, where the infrastructure to support the services must be built as they service grows.” John Fontana, writing on Ping Identity’s blog, argues that the Internet of Things will demand standardized technologies and protocols for managing identity and security – something akin to what standards like OAuth and OpenID do for web services and web-based applications.

Pingback: Verizon: New Cloud Encryption Service Will Secure IoT Devices | The Security Ledger