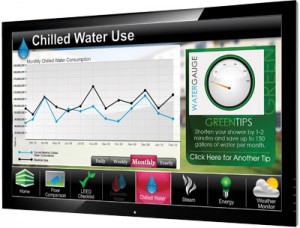
The FBI issued an alert to businesses in July after unknown attackers breached a computer used to control the heating, ventilation and air conditioning (HVAC) system of a New Jersey company, accessing a graphical user interface for the system, including a floor play layout of the company’s office.
The attacks came after an Anonymous affiliated hacker, using the handle @ntisec, published links to vulnerable ICS systems running software from the firm Tridium online. The links included the address of an administrative system that controlled the HVAC system used by US Business 1, a New Jersey company that installs air conditioning systems for other companies, according to a copy of the July, 2012 Situational Information Report (PDF), issued by the Newark Division of the FBI.
The alert concerning the February and March, 2012 attack was released by the web site Public Intelligence on Saturday. The FBI did not respond to a request for comment from Security Ledger.
US Business 1 installed the Tridium system on customer networks, and used it for its own offices. According to the FBI report, the Niagra AX Framework software used to manage the company’s HVAC system was not deployed behind a firewall and was accessible from the public Internet. The attacker was able to locate the device using a search for Tridium Niagra systems on the Shodan search engine, then use a publicly disclosed backdoor administrative account to log into the control system. A link to the administrative control panel was published online by @ntisec and was then accessed “multiple, unauthorized international and US-based IP addresses,” said the FBI report, citing information from a classified document.
The Tridium Niagra systems are installed on around 300,000 systems worldwide, including those used for building automation, lighting control, energy management and telecommunications, in addition to heating and cooling, according to the Tridium web site. The product was the subject of an alert from the Department of Homeland Security (DHS)’s Industrial Control System CERT (ICS-CERT) in July. The alert described vulnerabilities (PDF) discovered by ICS researchers Billy Rios and Terry McCorkle. One of those vulnerabilities allowed an attacker to download a file containing user credentials from a publicly accessible Tridium product, and decrypt the file’s contents to reveal the administrative user name and password. Other holes included a directory traversal vulnerability, weaknesses in the way session cookies and session IDs were generated by the Tridium products.
The FBI Issued an alert to companies in July regarding attacks on ICS software used to control HVAC and other critical systems.Tridium issued an advisory (PDF) about the security holes in July and a subsequent security patch for the vulnerable Niagra AX Framework systems.
Though less-discussed, vulnerabilities in SCADA and ICS systems are common and have become a thorny issue for a wide range of firms, as previously isolated systems are exposed to threats from the Internet, or from infected systems used by contractors and support staff. In October, ICS-CERT updated its warning about vulnerable, Internet accessible ICS systems, saying that a team of researchers had identified over 500,000 control systems-related devices using the Shodan search engine, warning that attackers could use the search engine as a shortcut find vulnerable systems.

Pingback: SCADA Security Friday News & Notes for 14 Dec 2012