In-brief: The FBI seized equipment from noted security researcher Chris Roberts on Wednesday, alleging that Roberts may have tampered with the systems aboard a United flight to Chicago. Roberts denies the claim.
Tag: Legal
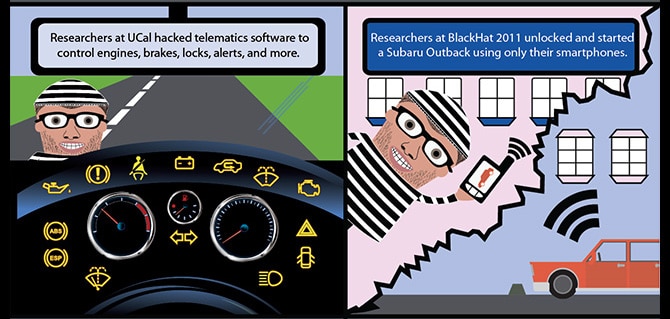
Cyber Lemons: Lawsuit alleges Hackable Cars Pose Risks to Consumers
In-brief: A lawsuit filed in California charges U.S. automakers with endangering their customers by failing to protect ‘connected vehicle’ features from cyber attack.
Supply Chain Risk Escapes Notice At Many Firms
Online attacks that come by way of suppliers and other third party business partners are one of the biggest threats that modern organizations face. But too few firms are giving supply chain security the attention it deserves, a panel of legal and information security experts told attendees at a cyber security forum in Boston on Wednesday. Companies need to protect their exposure through third parties better, according to the panel: beefing up auditing of internal- and partner assets and including contractual protections that will indemnify them in the event that a breach at a supplier or business partner exposes data that materially affects their firm. The panel, “Fortifying the Supply Chain,” was part of a day long event at The Federal Reserve in Boston and sponsored by the Advanced Cyber Security Center, a technology industry consortium. It brought together top legal and information security experts, including FireEye researcher Alex Lanstein and Jim Halpert, the […]
The Internet of Things: Legal Woes for CIOs | CIO
Stephanie Overby over at CIOs has an interesting piece today on the legal pitfalls that Internet of Things adoption may hold for chief information officers (CIOs). While the prospect of more, intelligent devices holds great promise for organizations across the economy, Overby notes that there are also risks – especially when it comes to the wholesale harvesting of customer data. “Many of the legal issues are not well understood even by sophisticated privacy practitioners,” the article quotes Christopher Wolf, a partner at the law firm Hogan Lovells saying. “In the world of sensors rather than computer screens, the legal issues are challenging.” CIOs are advised to consider “self-regulating” around issues like privacy, security and consent, to stay on the right side of the evolving law. CIOs should scrutinize every decision to collect user information and ask whether the benefits to collecting the data outweigh the potential costs, especially in the event of […]
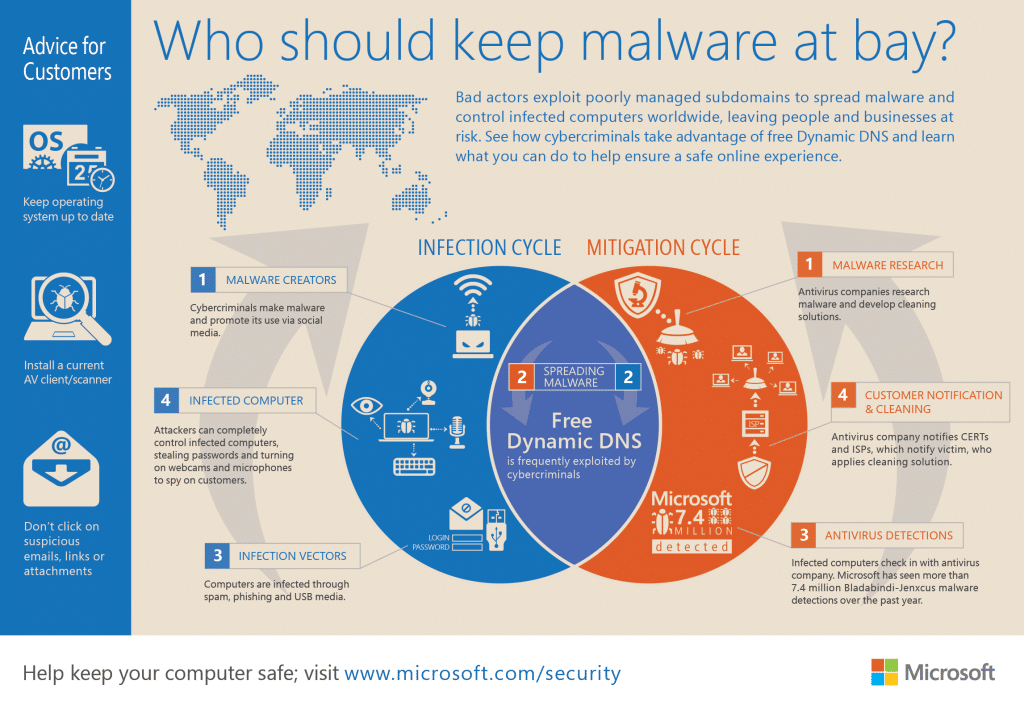
Microsoft Uses Courts To Take Down Malicious, Managed DNS Services
Microsoft Corp. has taken action against yet another cyber crime network, taking control of- and shutting down a managed DNS (domain name system) operated by the firm No-IP that were being abused by cyber criminals, the company said on Monday. The domains were associated with malware families named Jenxcus and Bladabindi that are believed to have infected on some 7.5 million systems, globally. The malicious programs – which are used to spy on the operators of infected systems – use Dynamic DNS services like NO-IP to communicate with command and control systems used to manage infected systems. Dynamic DNS makes the malicious systems more difficult to trace. In a post on Microsoft’s Digital Crimes Unit blog, Richard Domingues Boscovich, the company’s Assistant General Counsel said that the company had filed a civil case on June 19 naming two foreign nationals: Mohamed Benabdellah and Naser Al Mutairi along with a U.S. company, Vitalwerks Internet Solutions, LLC (doing […]