In-brief: a security researcher demonstrated a broadcast-based attacks on smart televisions, almost three years after a similar demonstration by researchers at Columbia. More than 90 percent of smart TVs may be vulnerable – but carrying out an attack may be challenging.
A security researcher at the German firm Oneconsult has demonstrated a method for hacking smart televisions using attacks buried in rogue broadcasts, and warns that many brands of the devices may be vulnerable.
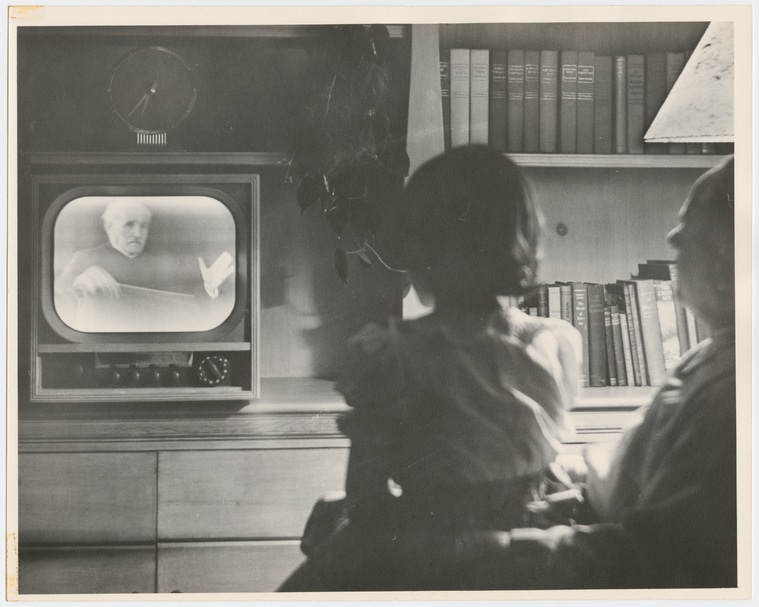
Rafael Scheel of OneConsult said that up to 90% of smart television sets sold today are vulnerable to exploits that use Hybrid Broadcast Broadband TV (HbbTV). An attacker equipped with an inexpensive DVB-T transmitter could remotely compromise smart TVs within its broadcast range, forcing TVs to load a malicious website in the background that could be used to install a malicious software program.
However, another researcher who has worked on smart television security cautions that broadcast based attacks using HbbTV are harder to make work than it would seem, while low hanging fruit in the form of network-based exploits of smart televisions are there for the taking.
HbbTV is an industry standard supported by most cable providers and smart TV makers that “harmonizes” classic broadcast, IPTV, and broadband delivery systems. An attacker who set up a rogue television transmitter. DVB-T, or Digital Video Broadcasting – Terrestrial, is a EU-based standard for broadcasting compressed audio, digital video and other data.
Scheel presented his research at the European Broadcasting Union (EBU) Media Cyber Security Seminar on March 22, demonstrating how a rogue DVB-T broadcast could be used to force the embedded web browser on a vulnerable smart set to load a malicious web page.
Poor design and security practices often make smart televisions easy targets. But getting access to the devices is a challenge. The malicious application route is one option – making smart televisions similar to mobile phones. However, users are much less apt to download and install smart TV apps than smart phone applications, making that attack vector even more challenging. Use of the web browser on TVs is even more rare. The CIA tool, dubbed “Weeping Angel,” relied on physical access to the target TV to plug-in a malicious USB stick that contained the malicious software.
He is not the first to point to security issues in the HbbTV standard. In 2014, Yossef Oren and Angelos Keromytis of the Network Security Lab at Columbia University, demonstrated a similar HbbTV attack against smart TV sets. However, the fact that HbbTV attacks are still a problem with even late-model sets suggests that calls for security improvements to the standard have gone unheeded by the HbbTV consortium, which manages the standard, said Craig Young, a principle researcher at the firm Tripwire.
Fixes like “whitelisting” features that would limit what stations could be received by smart television sets, or support for SSL and other authentication technologies are an option, but have not been embraced, he said. “It’s a real concern given that these televisions have much more computing power.”

Pingback: 10Fold- Security Never Sleeps- 150 - 10Fold Communications