We’ve interviewed security researcher Nitesh Dhanjani before. In the last year, he’s done some eye-opening investigations into consumer products like the Philips HUE smart lightbulbs. We did a podcast with Nitesh in December where we talked more generally about security and the Internet of Things.
Now Dhanjani is in the news again with research on one of the most high-profile connected devices in the world: Tesla’s super-smart electric cars. In a presentation at Black Hat Asia on Friday, he released findings of some research on the Tesla Model S that suggests the cars have a weakness common to many Web based applications: a weak authentication scheme. (A PDF version of the report is here.)
Specifically: Tesla’s sophisticated cars rely on a decidedly unsophisticated security scheme: a six-character PIN.
Dhanjani’s research discovered a variety of potentially exploitable holes that would give even an unsophisticated attacker a good chance at breaking into a Tesla or modifying it remotely. (The cars require a separate key fob to drive, so its unlikely that these vulnerabilities would result in theft of the car itself.)
Of note: Tesla’s companion mobile application as well as its web site can be hacked using brute force attacks, because Tesla sets no limit on password retries.The web site is susceptible to cross site scripting, phishing attacks or any of a number of well-trod web based attacks.
Dhanjani also notes that Tesla’s support desk is a source of possible compromise: Tesla support engineers can remotely unlock cars and – like all humans – might be socially engineered to do so by a thief.
Finally: Tesla publishes a Web API that allows third party application developers (for example: developers for Google’s Glass platform) to connect to the vehicle’s on board systems directly. Those third party applications, which store the car’s credentials are likewise vulnerable to hacking.
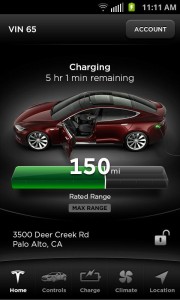
Why is this so bad? Well, with a valid email and password, a malicious hacker could track the location of a Tesla, lock or unlock its doors and configure a wide range of environmental settings, Dhanjani writes in his report.
Dhanjani recommends that Tesla “address the issue of using static passwords with low complexity requirements.” (That is: require longer passwords or switch to a multi-factor authentication scheme.) He also thinks Tesla owners should refrain from using any third party applications with their car – at least until Tesla announces an software development kit (SDK) and introduces a way to isolate (or sandbox) third party applications.
In a statement to the web site UberGizmo.com, company spokesman Patrick Jones said that Tesla “protects our products and systems against vulnerabilities with our dedicated team of top-notch information security professionals, and we continue to work with the community of security researchers and actively encourage them to communicate with us through our responsible reporting process.”
Indeed, Tesla recently hired security researcher Kristin Paget away from Apple to bolster its internal security team.
In his other research, Dhanjani has also found that even sophisticated connected devices often suffer from a “weak link” problem that undermines their security. He has noted that many devices assume that the local (wi-fi) network that the devices are deployed on is trustworthy. The result could be that malware authors may soon begin looking for connected consumer devices, not just PCs, Dhanjani warns. “The next generation malware authors will abuse this trust to invade our privacy or even cause physical harm.”
