A string of reports in recent weeks has focused a spotlight on rising attacks against an often-overlooked piece of equipment that can be found in almost every home and business: the wireless router.

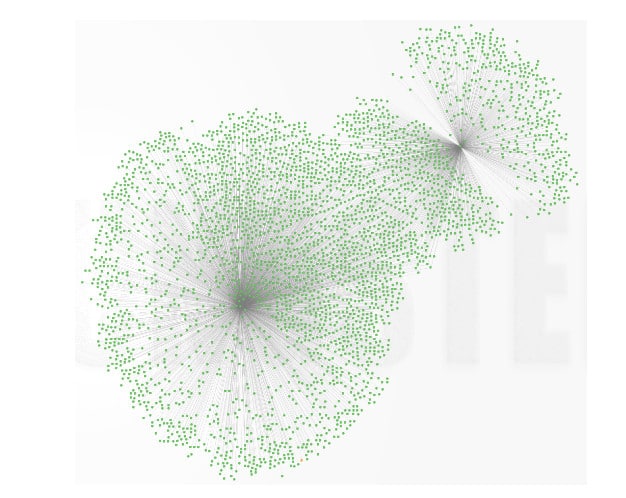
Just this week, the security firm Team Cymru published a report (PDF) describing what it claims is a widespread compromise of small office and home office (SOHO) wireless routers that was linked to cyber criminal campaigns targeting online banking customers. Cymru claims to have identified over 300,000 SOHO devices (mostly in Asia and Europe) that were compromised.
According to the report, the compromises first came to light in January, after Team Cymru analysts noticed a pattern of SOHO routers with overwritten DNS settings in central Europe. The affected devices are from a range of manufacturers, including well-known brands like D-Link, Micronet, Tenda and TP-Link. The devices were vulnerable to a number of attacks, including authentication bypass and cross-site request forgery hacks.
Once compromised, vulnerable devices had their DNS (Domain Name System) settings altered, so that requests to visit web sites were directed through servers controlled by the attackers.
(FUD alert: Team Cymru didn’t observe any actual malicious activity stemming from the DNS redirection attacks. Also, the vast majority of the compromised SOHO routers Cymru identified are located in Vietnam, India and Italy, with only a couple thousand devices identified in the US. So you probably don’t have to worry.)
Still, the report from Team Cymru adds one more data point to a string of recent reports and warnings about attacks that target home routers. In January, the Polish security website Niebezpiecznik.pl warned of a remotely exploitable hole in firmware run on home routers by TP-Link, a popular brand in Poland. The vulnerability in the firmware allowed a remote attacker to download the backup configuration data from the device without first authenticating (or logging in) to the router. The file could be used to harvest the actual administrative credentials needed to take control of the TP-Link router.
In February, the same site reported on apparent online banking fraud resulting from online banking credentials harvested after a home router compromise.
Low-cost SOHO routers are ubiquitous and provide wired- and wireless Internet connectivity in addition to local DNS and DHCP services. As we reported last year, the small, insecure devices are numerous and often loosely secured and managed. The sheer number of vulnerable home routers and gateways that are vulnerable to trivial attacks makes them attractive to cyber criminal groups, state-backed actors or hacktivists for malware distribution, spam or crippling denial of service attacks on the ISPs that manage the devices.
Security researchers Ehab Hussein (@_obzy_) and Sofiane Taimat (@_sud0) of the firm IOActive wrote in April, 2013, that ISPs often identify blocks of network addresses (or “netblocks”) assigned to home-based customer-premises equipment, making it easy for would-be attackers to focus their search for vulnerable equipment to known netblocks at a given ISP. Free tools like WhoIs or IPInfoDB can provide crucial information about the addresses that make up the netblock, including the type of connection (ADSL, DSL, Wi-Fi) and so on, then generate a list of target IP addresses, the two wrote.
Cymru said that tests on the DNS servers used by the compromised SOHO routers didn’t reveal any suspicious activity. Requests sent through the DNS servers were correctly forwarded to the authoritative server. However, researchers did experience delays when requesting banking websites and software downloads from sites like Adobe – a possible indication that such requests were being harvested or otherwise tampered with.
The security of so-called customer-premises equipment (or CPE) is taking on new importance as more ‘smart’ devices, from televisions to thermostats and surveillance cameras start to leverage residential local area and wireless networks in order to provide enhanced services. Compromised routers can easily be used to shut off critical services or even as a stepping stone to more invasive attacks.

Pingback: Linux IoT Worm Still Alive And Mining Virtual Coins | The Security Ledger
Pingback: Heartbleed: Technology Monoculture's Second Act | The Security Ledger
Pingback: Report: Hell is Unpatched Systems | The Security Ledger