A few months ago we wrote about a new Internet worm notable because it spread between devices running the Linux operating systems, and because it had the ability to infect a range of non-PC devices including set top boxes.
Symantec was quick to suggest that the worm, Linux.Darlloz, was the first “Internet of Things” malware. Now, three months later, Symantec is updating the story: noting that Darlloz is still out there, and seems to have been put to use mining for virtual currencies.
Writing on Symantec’s blog on Thursday, analyst Karou Hayashi said that researchers there discovered a new variant of Darlloz in January that included code changes and improvements from the version discovered at the end of 2013.
Darlloz is versatile: it can run on devices using a variety of architectures, including the common Intel x86, but also hardware running the ARM, MIPS and PowerPC architectures. Those are more common on non-PC systems such as home routers and set-top boxes.
[Read more Security Ledger coverage of Darlloz and IoT threats. ]
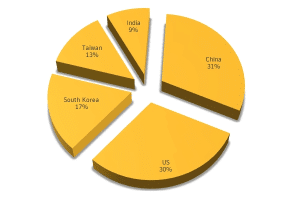
To date, Symantec has discovered around 31,000 devices worldwide infected with Darlloz – not a huge population of infected systems, by any measure. But not insignificant, either.

Recent updates to Darlloz appear to have focused the worm on mining crypto-currencies including Dogecoins and Mincoins. Intel-based systems infected with the new Darlloz variant are outfitted with cpuminer, an open source coin mining software.
By the end of February 2014, the attacker using mined 42,438 Dogecoins for a take of around…$31 USD and 282 Mincoins (approximately USD $150).
Symantec said that Intel based PCs, home routers, set top boxes and IP cameras are still the targets of choice for the malware, which is programmed with 13 default login credential combinations for common hardware, which is used to gain administrative access to the systems.
As we’ve noted, many Internet of Things devices are poorly secured by design or in deployment. Increasingly, cyber criminals are taking notice. The firm Team Cymru reported this month that it discovered evidence of a botnet consisting of 300,000 compromised home broadband routers, of the type that Darlloz affects.
