Ralph Langner is one of the foremost experts on the security of critical infrastructure that we have. So, generally, when Ralph says something – whether its about Stuxnet, or cyberwar or the security of nuclear power plants – folks listen.
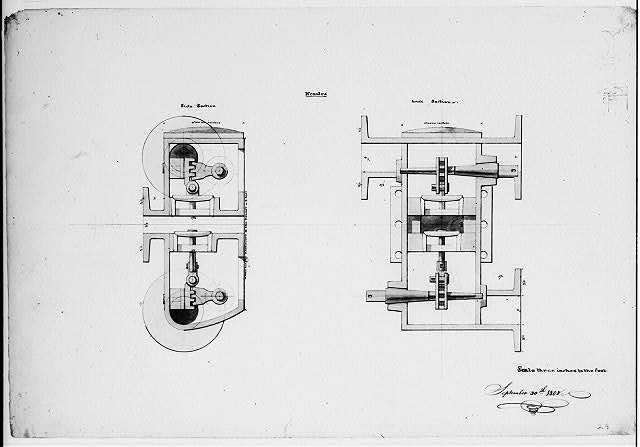
And these days, Ralph is wondering, out loud, whether our reliance on digital systems to manage critical infrastructure has gone too far. The answer, he suggests, may be to go “back to the future,” as it were: reintroducing analog systems into the control process chain as a backstop for cyber attacks.
Case in point: the Department of Homeland Security’s ICS-CERT warned on Friday that firmware for Siemens SIMATIC S7-1500 CPUs (Central Processing Units) contain nine vulnerabilities that could enable attacks such as cross site request forgery, cross site scripting and URL redirection. (Siemens has issued a firmware update that patches the holes.)
Langner is among the world’s foremost experts on control systems security. He was among the first to suggest (publicly) that the Stuxnet worm was a targeted, nation-backed attack on Iran’s nuclear enrichment program.
Writing on Saturday, he said that the critical infrastructure sector is in a headlong rush to replace aging, analog control system infrastructure with modern, digital systems. Software based control infrastructure, he notes, offers many advantages – flexibility, the possibility of remote operation and management and access to a much larger pool of talent and expertise. Engineers who understand and can manage analog systems are, after all, a dying breed – literally.
But Langner cautions against the wholesale embrace of digital systems by stating the obvious: that “every digital system has a vulnerability,” and that it’s nearly impossible to rule out the possibility that potentially harmful vulnerabilities won’t be discovered during the design and testing phase of a digital ICS product.

Even casual review of recent headlines about the security of industrial control system software makes it clear that the vast majority of dangerous, remotely exploitable vulnerabilities in ICS product are not found until those systems are already deployed in the field. At the recent S4 Conference, cyber security experts warned that energy and transportation networks remain vulnerable to attacks leveled at security holes in critical systems that can linger for months or years without being patched. The Federal Energy Regulatory Commission has also warned that, under the right circumstances, small scale cyber or physical attacks on a handful of electric transmission substations could cause a nation-wide blackout.
Langner’s proposal isn’t to abandon the move to digital, but to continue to rely on analog control systems as a hedge against crippling cyber attacks that are almost certain to occur.
“It would seem to follow that if …the hacking of digital safety systems at nuclear power plants was unacceptable, then analog control of safety systems ought to be a viable option on the table,” he writes.
Official sanction of analog systems as a way to segment- or backstop critical digital systems would provide the market an incentive to make, market and sell such systems – creating a market for the types of technologies that critical infrastructure owners need.
Food for thought!

There seems to be something missing in the first sentence of the fourth paragraph.
Yes – sentence fragment. A good catch. I’ve removed the fragment. Thanks for reading!
Pingback: Is Analog The Answer To Cyber Terrorism? | Sputnik7
Or you could just keep the digital systems offline, so you only have to worry about on site security.
Easier said than done – the interconnections between traditional IT assets and ICS/SCADA are often hard to get your arms around. Most critical infrastructure operators would tell you that their ICS systems are air-gapped and aren’t reachable via their network or the Internet. Recent history shows they are often mistaken in that belief.
It looks that we have to go back to stone age? We can make the systems stand alone and keep them in simplex communication mode! Control systems can send data out and no way they can receive data from any outside sources!
Pingback: Is Analog The Answer To Cyber Terrorism? | Beat the rich
Pingback: Is Analog The Answer To Cyber Terrorism? « Truth Is Rising