Despite increased media attention to the security of industrial control systems and critical infrastructure, progress in securing those devices has been slow, experts say.
Despite progress in some areas, critical infrastructure – including energy and transportation networks- remains vulnerable to attacks leveled at known security holes for months or years because of a lack of vendor response or customers who lack the incentive or know-how to patch vulnerable systems. That according to some of the world’s top experts in cyber security and industrial systems, who are gathering this week at an industry conference in Miami.
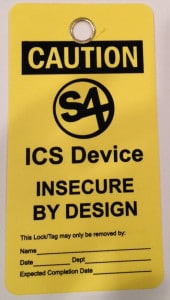
The S4 Conference, sponsored by the firm DigitalBond, is one of the premiere conferences for cyber security as it pertains to industrial control systems and often coincides with disclosures from industrial system vendors about serious security holes in their products.
The security of industrial control systems has been a top concern of IT security experts and government regulators ever since independent security researchers and hackers began migrating across the land bridge (so to speak) from PC systems to embedded devices and industrial control systems in the last decade. Media attention to the work of researchers like Dylan Beresford was often met with confusion, hostility or indifference by firms that make industrial hardware and software – Honeywell, Siemens, GE and others.
But interest in the vulnerability of industrial systems took on new dimensions with the identification of the Stuxnet worm in 2010. Stuxnet proved not only that ICS and SCADA systems were vulnerable to attack, but that attacks against such systems were practical and could be exploited to devastating effect by nation-backed hacking crews or, more worryingly, by terrorist groups.
Over the years, S4 has expanded to accommodate the increased attention to the security of critical infrastructure. This year’s show is four days long and includes sessions devoted to ICS practitioners and a day devoted exclusively to the topic of cyber weapons.
Despite the increased scrutiny of industrial systems by both bad guys and good guys, progress towards more secure technologies has been spotty. Eireann Leverett, a security researcher at IOActive who discovered the vulnerabilities in Siemens’ SCALANCE X-200 switches said that Siemens has made great strides in working with security researchers in the last five years.
Among other steps, Siemens has launched a dedicated security emergency response (or CERT) team to work with independent researchers and respond to reports of vulnerabilities in its products. In the case of the SCALANCE vulnerabilities, Siemens issued a patch within three months of Leverett’s initial report – a rapid turn around.
“What I’d like to see is all the other vendors be able to do that,” he said. “I’d like to see them respond to a vulnerability report from an external researcher courteously and get a patch out in three months.”
Many do not. Speaking on Thursday, independent researcher Chris Sistrunk and Adam Crain of the firm Automatak told the audience at S4 that they have also seen uneven response from vendors to reports of widespread and exploitable security holes in a common protocol, DNP3, that is used by industrial control systems. Despite notification by the researchers, public warnings from the Department of Homeland Security (DHS) Industrial Control Systems CERT, and even a New York Times article on their research, many ICS vendors have been slow to address the security issues in DNP3 within their products.
Despite prompt response from some prominent vendors, many were slow to respond or, when they did address the DNP3 issue, failed to acknowledge the vulnerability in the documentation accompanying the patch, or failed to inform the Department of Homeland Security or the researchers when the fix was available. At least one vendor appeared unable or unwilling to fix the problem in its products and “gave up.”
“What we’re finding is that some vendors are proactive and we can work with them. In other cases, vendors may have made progress (on security) with new products, but haven’t gone back and reviewed old code bases,” Leverett said. That’s a problem for products whose lifespan is commonly measured in decades, not years.
Even vendors who fixed the DNP3 vulnerability may not have taken the initiative to do further assessments of their products to look for similar holes, Sistrunk and Crain said.
Customers, also, bear responsibility for security problems, Leverett said. “You see some organizations where they have redundancy – multiple versions of devices that were put in the network so you don’t have a single point of failure. But that’s the top five or 10 percent of ICS deployments,” he said. “There are many that wait a year or two to patch something like (the SCALANCE switch vulnerability).”
Leverett said the need to maintain “availability” of critical services often hampers patching and other critical security operations – despite widespread recognition of the danger. He will be presenting his research on the Siemens SCALANCE Switch at S4 this year and releasing proof of concept code that can help Siemens customers determine if they have deployed hardware that is vulnerable.
I am attending the S4 Conference this week for the first time in two years and will be leading a discussion with noted cyber security researcher and recognized Stuxnet authority Ralph Langner on Friday. Stay tuned!







Pingback: S4x14 Press Roundup
Pingback: Is Analog The Answer To Our Digital Insecurity Dilemma? | The Security Ledger