The saga of the application-signing flaw affecting Google’s Android mobile phones took another turn Tuesday when a Silicon Valley startup teamed with graduate students from Northeastern University in Boston to offer their own fix-it tool for hundreds of millions of Android phones that have been left without access to Google’s official patch.
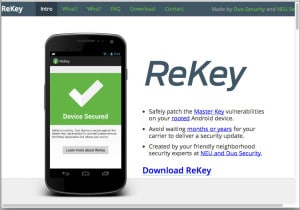
Duo Security announced the availability of an Android utility dubbed “ReKey” on Tuesday. The tool allows Droid users to patch the so-called “Master Key” vulnerability on Android devices, even in the absence of a security update from Android handset makers (OEMs) and carriers who distribute the phones, according to a post on the Duo Security blog. The tool can be downloaded from the site rekey.io.
“ReKey is the latest of our research projects designed to make the Internet a safer place,” said Collin Mulliner, a postdoctoral researcher at NEU SecLab in a joint press release issued by NEU and Duo. “We hope that ReKey will provide a practical tool for users to protect themselves and, at the same time, raise awareness of the challenges in the mobile security space.”
Google issued a patch for the application signing flaw in March, soon after being informed of its existence by Jeff Forristal, a researcher at Bluebox Security. The flaw is located in an Android component known as the Dalvik Debug Monitor Service (or DDMS), the virtual machine that runs software on Android devices. The vulnerability affects almost all Android devices in use, could allow a malicious actor to modify a legitimate, signed Android application without affecting the application’s cryptographic signature. That would prevent Android from noticing the changes when the application is installed. Forristal will present more details of the Android flaw at the Black Hat Briefings hacker conference at the end of this month.
In an e-mail exchange with The Security Ledger, Jon Oberheide, the CTO of Duo Security, said that ReKey provides an in-memory patch for the master key vulnerability, dynamically instrumenting the Dalvik bytecode routines where the vulnerability originates, patching it in-memory. Oberheide said that ReKey will also”hook” (or monitor) those routines to notify you if any malicious applications attempt to exploit the vulnerability.
Despite the availability of a patch, many Android users remain vulnerable to attacks that take advantage of the application signing flaw because Android handset makers have been slow to issue updates for their Droid handsets. Even for those handsets that do have patches available (Samsung and HTC have patched some of their Android devices), some carriers have not deployed them to their customers, further limiting the reach of the patch.
Those vulnerable devices are susceptible to attack, especially now that proof of concept exploit code has been released for the Android master key vulnerability.
“The security of Android devices worldwide is paralyzed by the slow patching practices of mobile carriers and other parties in the Android ecosystem,” said Oberheide. However, the fragmentation of the Android ecosystem is significant enough that it is no longer feasible for Google to take over responsibility for distributing patches, Oberheide said.
“It would be infeasible to expect Google to be responsible for all the various software, hardware, and configuration cross-products that OEMs and carriers produce,” he wrote in an e-mail. Similarly, carriers aren’t in the business of managing the security of mobile devices, he said. “They provide cell and data service to your phone, that’s what they’re good at.”
Third parties like Duo may, in time, have to take the lead on providing security for vulnerable devices- working with carriers and OEMs in an open ecosystem.
“Hey, third parties providing fixes sounds better than no parties providing fixes,” he wrote.

