Botnets are mostly linked with spam e-mail campaigns, denial of service attacks and data theft. But global networks of compromised hosts can be used for a variety of ends – not all of them malicious.
That was the idea behind “Internet Census 2012,” a stealth project by an unnamed and unknown researcher/hacker to map the entire IPV4 Internet address space using a massive network of compromised devices. The results, published in the form of a research paper, underscore the problem of unsecured embedded devices, including set top boxes, home routers and critical infrastructure, with the hacker able to locate and compromise these systems, creating a botnet of more than 420,000 nodes.
According to a copy of the report, the project grew out of an experiment to locate unprotected devices online using nmap, the open source scanning tool. By compromising each vulnerable host and then enlisting it to scan for other unprotected hosts, the hacker was able to continue doubling the size of his scanning apparatus until he had a network of 100,000 scanning devices able to map the entire IPV4 address space in less than an hour.
The hacker used a custom binary (aka ‘malware’) – adapted to a number of platforms -to manage scanning across the botnet and provide command and control capabilities. S/he also designated around 9,000 nodes to monitor the botnet and collect data from the scanning nodes for upload to the management server. The botnet used nmap, as well as ICMP ping and reverse DNS to scan and identify Internet connected hosts.
Most of the unprotected devices that were discovered were described as “consumer routers or set-top boxes.
“Whenever you think ‘that shouldn’t be on the Internet but will probably be found a few times’ it’s there a few hundred thousand times. Like half a million printers, or a Million Webcams, or devices that have root as a root password.”
In addition, IPSec routers, BGP routers, industrial control systems, physical door security systems and equipment by enterprise vendors like Cisco and Juniper were enlisted in the botnet.
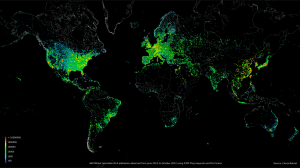
The botnet, dubbed “Carna” by its creator, operated between March and December, 2012 and collected 9 Terabytes of data, comprising billions of ICMP ping probes, reverse DNS records and service record probes.
The hacker said that the project was designed to be “nice” and that the binary was designed to “minimize interference with normal system operation.”
“We used the devices as a tool to work at the Internet scale. We did this in the least invasive way possible and with the maximum respect to the privacy of the regular device users.”
However, there’s little question that the activities engaged in to carry out the scan are illegal and little different from other malicious botnet operations, with the researcher/hacker remotely controlling compromised hosts and, in some instances, rebooting them to aid with scanning and data collection.
The Carna botnet’s creator said that the project was really for kicks but that – mapping aside -this is a cautionary tale. “A lot of devices and services we have seen during our research should never be connected to the public Internet at all,” the botnet author wrote. “As a rule of thumb, if you believe that ‘nobody would connect that to the Internet, really nobody’, there are at least 1000 people who did.”
