Podcast: Play in new window | Download (Duration: 24:17 — 44.5MB) | Embed
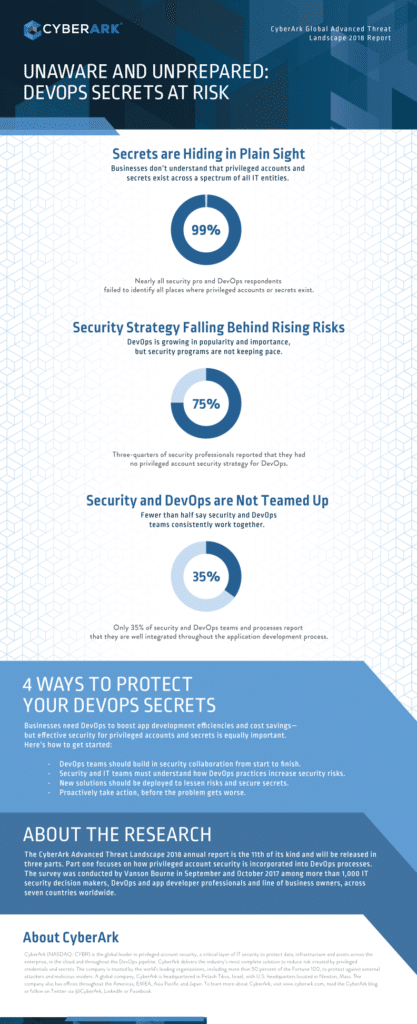
The hack of Uber and the loss of information on 57 million customers is just the latest security incident stemming from what our guest Elizabeth Lawler calls “DevOps secrets” – valuable credentials, APIs and other sensitive information that often end up exposed to the public as a result of lax continuous development operations. In this Spotlight Edition* of The Security Ledger Podcast, sponsored by CyberArk, we talk with Elizabeth about how to contain DevOps secrets and secure the secret super user lurking in modern organizations: highly privileged application code.
When the ride hailing service Uber revealed that information on 57 million customers and 600,000 drivers had been stolen by hackers, media attention focused on the company’s apparent decision to cover up the breach for months. That decision now seems likely to deliver a wealth of lawsuits to Uber’s doorstep.

Just as important, however, are the still-emerging details about how hackers were able to penetrate the systems of the nimble and tech-savvy firm. Though details of the incident are still sketchy, attention has focused on developer credentials accidentally published to the software repository Github. According to reporting by Bloomberg, those credentials gave the hackers immediate access to the developers’ privileged accounts on Uber’s network, and with it, access to sensitive Uber servers hosted on Amazon’s servers, including the rider and driver data they stole.
Just the latest incident linked to DevOps Secrets
The incident is just the latest to highlight a now-common culprit: exposed administrative credentials tucked into computer code that was checked into GitHub, a popular cloud based code repository. In this Spotlight edition of The Security Ledger podcast, we speak with Elizabeth Lawler of the firm CyberArk. She notes that Uber isn’t the only company to fall afoul of what are often described as “DevOps secrets” – small, but critical pieces of privileged information or data that are accidentally exposed as part of agile “continuous” development practices that heavily rely on cloud based assets like the GitHub code repository or Amazon Web Services for hosting and storage. In 2016, she notes, a security researcher found the entire source code of Twitter’s Vine video service stored in an unprotected Docker container.
Understanding the DevOps Secrets Risk
But what are “DevOps secrets”? What risk do they pose to your organization? While companies scramble to secure privileged user accounts from threats like “credential stuffing,” Lawler contends that they often overlook the most powerful privileged user on their networks: the application code churned out by agile development teams and then circulated to customers and – often -the public.
Saying ‘code is the new privileged user’ is a way of asking ‘did you realize that your code doesn’t have an identity and that nobody gave it any permissions, particularly?’ – Elizabeth Lawler, CyberArk
API keys, database passwords and the like pushed to GitHub at a “midnight moment” when developers just want to get home and into bed are the classic example, but hardly the only one, Lawler said. “There’s a lot of awareness that this is a common mistake,” and that means attackers are increasingly looking for them. But dev ops secrets might also reside on local resources like developer laptops or build systems like Jenkins.
To start our conversation, I asked Elizabeth to explain what is meant by saying “code is the new privileged user” and to talk about how and why organizations need to think about assigning identities to both application code and coded workflows.
Check our full conversation in our latest Security Ledger podcast at Blubrry. As always, you can also listen to it on iTunes and check us out on SoundCloud. And, if you like our intro music, give some love to the group JoeLess Shoe, who recorded “Baxton,” the song we use in just about every podcast.
(*) Spotlight Edition podcasts are commissioned works created by Security Ledger for the sponsoring company or organization.