
In-brief:The tactics of cyber criminal hacking crews are indistinguishable from those of sophisticated, state sponsored “advanced persistent threat” groups, the firm FireEye said in its most recent M-Trends report.
The gap between the bad guys and firms who are their victims yawned even wider in 2016, according to a new report out by the firm FireEye, which warned that nation backed hackers and sophisticated cyber criminals advanced by leaps and bounds in 2016, far outstripping the ability of even sophisticated firms to detect and thwart their efforts.
Hacking groups refined their tools and methods for bypassing security, becoming increasingly intimate with victims in order to circumvent protections. Among other things, Mandiant witnessed sophisticated hacking groups that phoned victims to elicit email addresses and other information useful to sidestepping security controls. Techniques have advanced to such a degree that there is no longer a meaningful distinction between the behavior of so-called “advanced persistent threat” (APT) hackers and financially motivated hacking groups, Mandiant found.
“While nation-states continue to set a high bar for sophisticated cyber attacks, some financial threat actors have caught up to the point where we no longer see the line separating the two. Financial attackers have improved their tactics, techniques and procedures (TTPs) to the point where they have become difficult to detect and, challenging to investigate and remediate,” Mandiant said in its annual M-Trends 2017 report, which distills the findings of the company’s consulting engagements for the past year.
Mandiant’s report traces a steady evolution of attacker tools and techniques dating back at least to 2014. During that time, hackers targeting banks and financial services firms have progressed from simple attack tools and relatively limited compromises of similarly-configured systems to extensive and diverse attacks that rely on custom malicious software tailored to the victim’s environment and sophisticated “counter forensic” techniques designed to cover attackers’ tracks and allow them to remain on victim networks undetected.
Alas, the detection and incident response capabilities of organizations has not advanced at the same pace. Indeed, as companies have added detection tools and capabilities to respond to new attacks, companies may have become “victims of their own successes,” Mandiant suggests. “With increased investments in security tools and technologies, teams have become overwhelmed with alerts and data and are struggling to prioritize and find the signal in the noise,” the company said.
The increasing sophistication of attackers is manifest in a number of ways. Mandiant notes that attackers have stashed backdoors and other tools on legitimate web sites for “staging,” avoiding the IP reputation filters built into web proxy and intrusion detection tools. Sites like Github and Microsoft’s TechNet were used for command and control of compromised endpoints within victim organizations, Mandiant said.
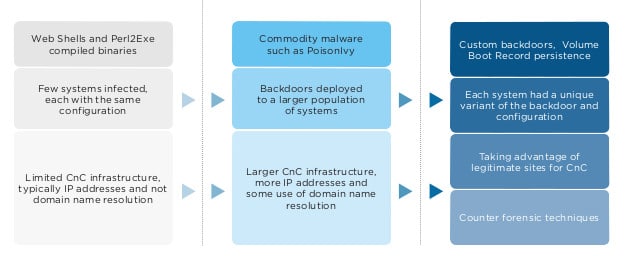
Hacking groups have also embraced the use of tools like Volume Boot Record (VBR) modification to load malicious tools on infected systems before the host operating system is loaded, thus avoiding a wide range of detection tools that rely on the Microsoft Windows API.
For organizations that rely on cloud-based productivity tools like Google’s G Suite, hackers have gone so far as to create malicious Google applications that pose as Google security tools. When installed, the applications obtain an OAuth token that gives the attacker access to the user’s data – including Google Drive and Gmail – even after they have changed their password. Attackers also used standard administrative tools, such as Powershell, to disguise their activities from security monitoring tools.
In their broad outlines, attacks in 2016 resembled those from previous years, Mandiant found. Attackers were quick to identify exposed or weakly protected systems and gain control over them, before pivoting to other, higher value assets. However, in other ways, attacks in the last year pushed into new territory. Mandiant related accounts of attacks on banking and financial services customers that betrayed a deep understanding of the target business. In one investigation, an attacker modified a compromised banking network user account to no longer require “four-eyes” approval on transfers – an industry requirement that two sets of eyes are needed for every transaction – by compromising both an account used to initiate transactions and an account used to approve transactions. “Mandiant investigators surmise that the attacker had significant knowledge of banking network transactions, in part evidenced by knowledge of the four-eyes process and how to circumvent that requirement by escalating the privileges of a targeted banking network account,” the company concluded.
In another incident described in the report, attackers got wind of the presence of incident response professionals from FireEye’s Mandiant unit on the compromised network and began masquerading as the Mandiant consultant to send additional phishing emails to accounts within the victim organization.
The report recommends a number of steps for companies to take to try to level the playing field. Mandiant said firms need to do a better job identifying critical data and assets and segmenting that on their network to hamper lateral movement by attackers. Companies need to invest in threat intelligence to make themselves aware of nascent attacks against their environment. Investments in security automation and orchestration to help overcome the “alert fatigue” that results from so many, noisy security tools. Organizations also need to develop dedicated “threat hunting” capabilities that attempt to identify threat actors and respond to current and future attacks.
Check out the full M-Trends 2017 report here.

Pingback: Twitter Hack is latest to underscore Third Party App Risk | The Security Ledger