In-brief: security experts are warning about the threat posed by third-party applications that tap into prominent social media platforms like Twitter after accounts belonging to media organizations and prominent personalities were hacked and hijacked to display messages accusing Dutch and German officials of Nazi sympathies.
This week’s hack of thousands of prominent Twitter accounts has underscored the limits that users face in protecting social media platforms and the risk posed by third-party applications that run on top of those platforms, security experts warn.
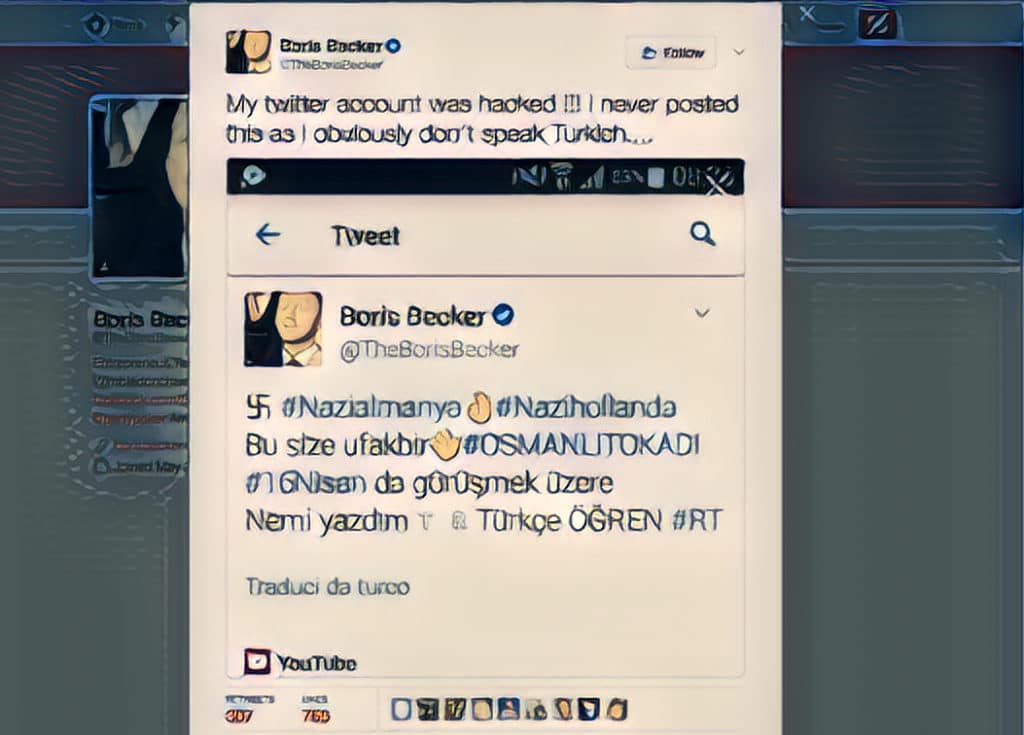
The hack took place Wednesday and affected an eclectic group of Twitter accounts used by media outlets such as Forbes and the BBC as well as prominent government and human rights groups like Amnesty International and Unicef and celebrities like Tennis great Boris Becker. Twitter accounts caught up in the hack were hijacked and posted messages in the Turkish language accusing both Germany and The Netherlands of racist and Nazi sympathies. The barrage of messages, depicting the Nazi Swastika and messages in Turkish was widely seen as blowback for a diplomatic row between the Governments in Ankara and the Netherlands in which Turkey’s ambassador was barred from speaking at rallies of Turkish nationals living in The Netherlands.
Despite the varied list of targets, however, behind the scenes was a single culprit: a social media tracking application known as Twitter Counter that is used by more than 2 million Twitter account holders. In a statement Wednesday, Twitter Counter, which is based in Amsterdam, said the breach lasted for around two hours and began in the early morning hours, US-time.
“It appears that the attack affected a number of accounts using this service as well as other Twitter accounts through additional third-party applications and direct hacking of Twitter accounts,” Twitter Counter said in a statement.
The company’s CEO, Omer Ginor, said the hacks – occurring on the same day that Dutch voters took to the polls in a closely watched election – was not a coincidence but “part of a bigger political offensive at Dutch online targets.” The company is investigating the incident, he said.
Twitter Counter is among the most popular social media tracking applications, along with platforms like HootSuite and Brand Watch, Evan Blair, the co-founder of the firm Zero Fox, told The Security Ledger.
But security experts warn that the means hackers used to compromise the accounts is part of a growing problem, as social media and mobile device users grant permissions to third-party applications that can be compromised or – in some cases – be malicious themselves. By agreeing to the application’s terms of use, Twitter, Facebook or mobile device users are often giving it access to their account and the ability modify content.
“The more connected and integrated services become, the more every app has a supply chain to protect. In this case, it wasn’t Twitter that was compromised directly, but a third-party app that integrates with the messaging platform,” said Tim Erlin, senior director of IT security and risk strategist at Tripwire in an email statement.
“Most of these are from reputable companies,” said Blair, “but you’re assuming that the company has done its due diligence in areas like application development and security monitoring.”
That’s a big assumption that often proves false, he said. “These aren’t considered critical path technologies,” he noted. That means the bar for secure design and deployment is set low.
The stakes for affected firms can be high. As the Wednesday incident shows, firms risk reputation damage as the result of compromised social media accounts. But Twitter is also used for customer support by countless brands and 64% of those engagements contain some form of personally identifying information (PII) or payment card information (PCI), Blair notes.
Compromising third-party applications or fooling victims into downloading and installing a malicious application for a social media platform can pay long-term benefits. Such applications are often granted liberal access to account data in addition to control over critical functions. Moreover: their access typically persists, even after users have changed their password. Applications are often exempt from two factor authentication schemes, providing an easy way to sidestep such security features, Blair said.
In its recent M-Trends report, FireEye’s Mandiant division warned about the risk posed by malicious and compromised applications designed for cloud-based productivity tools like Google’s G Suite. Hackers have gone so far as to create malicious Google applications that pose as Google security tools. When installed, the applications obtain a OAuth token that gives the attacker access to the user’s data – including Google Drive and Gmail – even after they have changed their password, Mandiant warned.
“Users should think about connected apps as part of their personal attack surface. The more apps that have access to your Twitter, Facebook and other social media accounts, the more doors there are for attackers to try,” said Erlin.
Still, overseeing such third-party applications can be difficult. Platforms like Twitter, Slack are often treated as “shadow IT” – user driven applications that are beyond the reach of corporate IT groups. Beyond that, those platforms have few features that make it easy for corporations or other organizations to monitor or limit which third party applications users can grant account access to. With modern, consumer-oriented corporations managing hundreds of social media accounts and users, the risk quickly grows.
“The fact that more security groups are not doing management and governance of social accounts is baffling,” Blair said. “These are corporate assets. I hope something like this is wakeup call.”






