Your search results are the next frontier for online scammers and fraud, including identity theft, warns Angel Grant of RSA’s Fraud & Risk Intelligence group.*
Tag: forensics
Massive Facebook Breach Affects 90 Million Accounts
Facebook forced a reset of more than 50 million user accounts on Thursday and would force another 40 million account resets in the coming days, citing a major breach of the site’s security that allowed unknown attackers to take over people’s accounts.
Episode 106: Election Trolls Are Afoot. We Talk To The Guy Who Watches Them
In this episode of The Security Ledger Podcast (#106): with the November midterm elections in the U.S. fast approaching, election related shenanigans have already cropped up in connection with contested races in swing states, as well as around “hot button” issues such as gun control and race. To find out what the trolls are trolling about, we speak with Jonathan Morgan, the CEO at the firm NewKnowledge, which provides disinformation defense services for organizations.
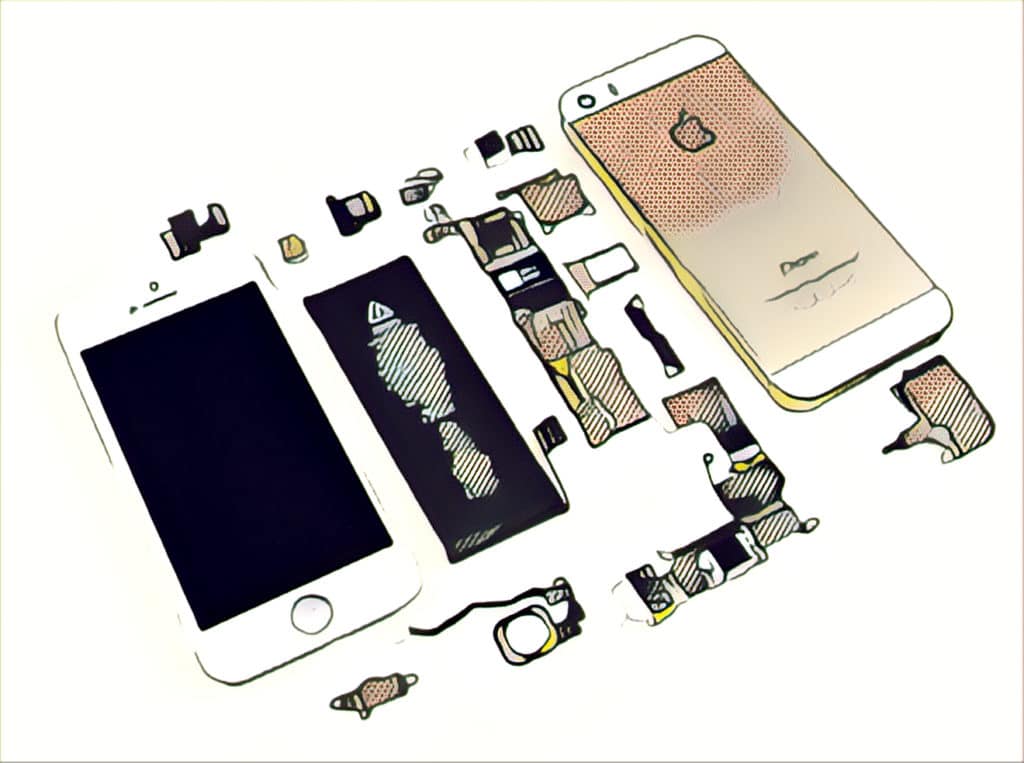
FBI exaggerated inability to access encrypted devices in promotion of ‘Going Dark’ problem
The FBI has mislead Congress and the public about the extent to which encrypted cellphones are hampering federal investigations by preventing authorities from accessing the devices–presumably to support the agency’s own agenda to gain backdoor access to them.
Opinion: Don’t Be Blinded by APTs
In this industry perspective, Thomas Hofmann of Flashpoint says that sensational coverage of advanced persistent threat (APT) actors does little to help small and mid sized firms defend their IT environments from more common threats like cyber criminals. The key to getting cyber defense right is understanding the risks to your firm and prioritizing investments to protect critical IT assets.