
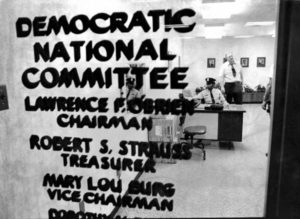
If you haven’t already had a chance to read the New York Times’ outstanding post-mortem on the hacking of the Democratic National Committee (DNC), I strongly urge you to do so. The story, coauthored by Eric Lipton, David Sanger and Scott Shane dissects the months long effort by hackers believed to be affiliated with the government of Russia to infiltrate the DNC, and that organization’s slow and lackluster response to the threat.
We all know how this story ends: with the leak of tens (hundreds?) of thousands of email messages that revealed the thinking and inner workings of the DNC and other Democratic party organizations and influencers. The content of those messages provided invaluable intelligence to opposition Republican party and were used to erode public confidence and trust in Hillary Clinton, the Democrats’ candidate for President.
The details of the unraveling of the DNC’s security make for required reading for any information technology professional. Among other things, the report notes the lack of proper detection tools at the DNC (which relied on “donations” to fund IT security, and everything else), a lack of training and awareness by front line IT support staff and opaque lines of communications. The tools of compromise – most phishing emails designed to look like Google password reset requests – were simple, but highly effective.
Most critical: the DNC lacked any kind of incident response function: a team charged with investigating and halting cyber intrusions and attacks on its networks, IT assets and employees. That’s surprising – given the high stakes involved – but not unusual.
Even today, incident response (or IR) is often perceived as the province of large and wealth firms in financial services or critical infrastructure. Smaller firms who struggle to staff even an IT security team may feel they don’t have the resources – or need – for a group devoted to incident response and threat hunting.
But incident response doesn’t have to be expensive or hard. That’s the message that I took away from my recent conversation with Tim Bandos of Digital Guardian.* Tim should know: he spent more than a decade doing incident response for chemical manufacturing giant DuPont, a top target of sophisticated hackers. There, he worked in the internal audit department before transitioning to DuPont’s cyber security group, where he had the chance to be a part of the team that stood up DuPont’s IR team. Now at Digital Guardian as the head of research, Tim has written an e-book on “Stopping Cyber Threats” that wraps up some of the lessons from his time at DuPont.
Among other things, Tim distinguishes between incident response – a set of formal procedures to classify and respond to security events – and threat hunting: identifying an incident early on, perhaps before it has spread or caused damage. As the story about the DNC tells us, this critical first step is needed if you expect to stay ahead of the attackers. The months long window that Russian hackers had to snoop around the DNC’s network allowed the attackers to spread out and focus on other targets as well, including the Democratic Congressional Campaign Committee (DCCC) and other groups. By the time the “threat hunting” and incident response happened, the horse (or data) had left the barn, so to speak.
I had a great opportunity to sit down with Tim about building a threat hunting and incident response capability. We talk about a range of topics, from how to “sell” IR and threat hunting to top executives and deciders, to building a team, using low-cost and open source tools and using outsourcing and managed services to complement internal staff and resources.
One of the many good points here is Tim’s argument that companies need relationships in place prior to incidents occurring, whether those are with third-party partners or law enforcement. Having lines of communication open allows information to move freely and investigations to move ahead quickly. The time taken to establish trust can slow down incident response badly – something that appears to be a factor in the DNC’s interactions with the FBI.
Check out our conversation below, or go to YouTube. You can also download Tim’s e-book (for free) from Digital Guardian’s web site. Happy hunting!
