In-brief: Barnes & Noble said its Nook tablets have not been used to steal data and that it is taking steps to stop using software by the Chinese firm Shanghai Adups Technology Co. Ltd. (ADUPS).
Barnes & Noble said its Nook tablets have not been used to steal data and that it is taking steps to stop using software by the Chinese firm Shanghai Adups Technology Co. Ltd. (ADUPS) that was observed transmitting reams of personal data from mobile phones to company servers in China.
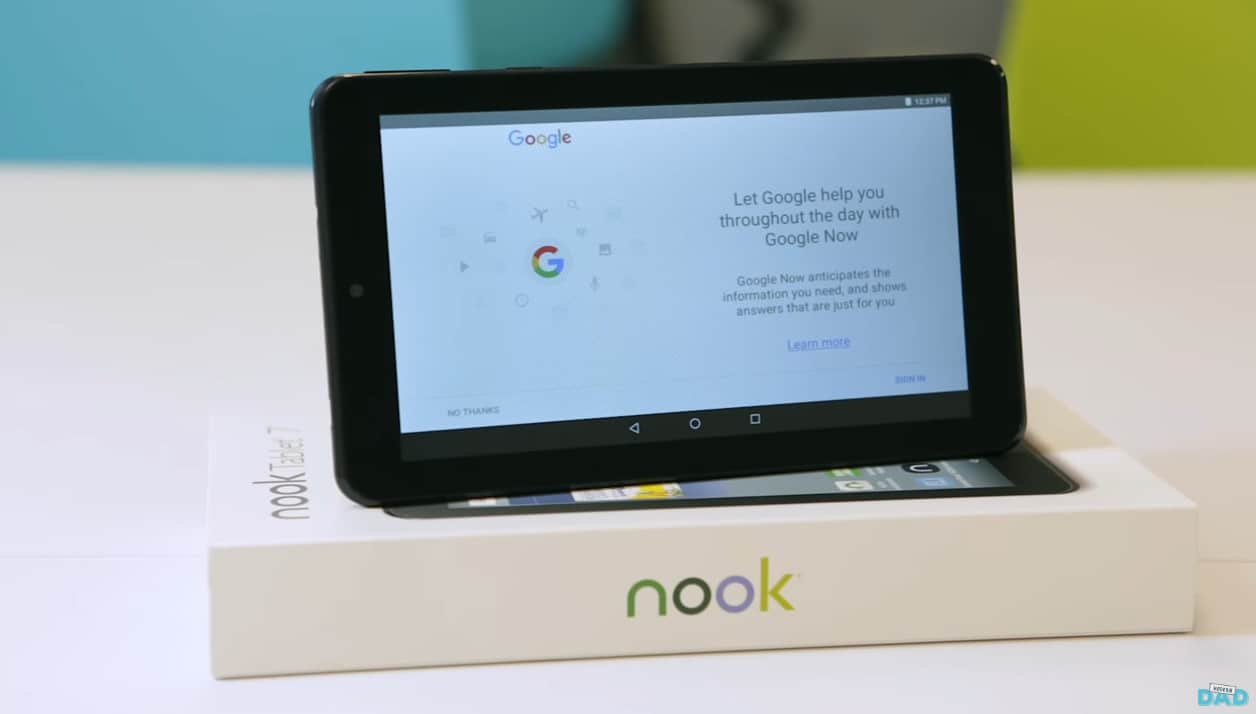
The company acknowledged that its low-cost NOOK Tablet 7 ran software update tools by ADUPS that was the subject of a warning from the firm Kryptowire in November, after that firm observed the software copying and transmitting the contents of mobile phones, including contacts and text messages, to company servers in China. The activity was not disclosed to users.
In a statement to The Security Ledger, Fred Argir, Barnes & Noble’s Chief Digital Officer said that the NOOK Tablet 7, which went on sale on November 26, ran software by ADUPS but that the software had been updated to a more recent version of the ADUPS software by the time it shipped that “has been certified as complying with Google’s security requirements, when first connected to Wi-Fi.”
ADUPS confirmed to Barnes & Noble that it “never collected any personally identifiable information or location data from NOOK Tablet 7 devices, nor will it do so in the future,” Argir said.
[Read more Security Ledger coverage of firmware security issues here.]
ADUPS software is used to update and manage mobile devices including smart phones and tablets. As reported by The Security Ledger, an earlier version of ADUPS software running on low-cost Android phones sold under the Miami-based BLU brand were observed sending user and device information to servers in China at regular, 72 hour intervals, according to Azzedine Benameur, a researcher at Kryptowire.
Further analysis by researchers at Kryptowire determined that the data included the full-body of text messages, contact lists, call history with full telephone numbers, unique device identifiers including the International Mobile Subscriber Identity (IMSI) and the International Mobile Equipment Identity (IMEI) of the phone. Using that data, a third-party or government could easily monitor the doings and conversations of a phone’s owner, Benameur said. That activity became the basis for a class action lawsuit against BLU on behalf of consumers whose data was transmitted.
ADUPS apologized for the mishap and explained that the data collection features were developed for one customer who was seeking to “screen out junk texts and calls from advertisers.” It has subsequently issued statements assuring customers that Version 5.5 of its firmware only collects “basic device information and product model information, such as device type, platform, model, version, IP address, International Mobile Equipment Identity (IMEI).” “None of this information can be used to identify the users even in combination with other data stored by ADUPS,” the company said in a statement on December 5.
Still, Barnes & Noble is at work to remove ADUPS from the Nook Tablet 7 entirely, Argir said. “That update will be made available to download within the next few weeks, but in the meantime customers can rest assured that the device is safe to use,” he said in a statement.
The issue first came to light with an article in the publication LinuxJournal, which noted that the BNTV 450, a low-cost Nook that sells for around $50 came loaded with Version 5.2 of the ADUPS software, which was observed siphoning off user data.
The problem highlights a growing concern that the software (or “firmware”) used in low cost electronic devices sourced outside the U.S. may harbor back doors or other features that compromise the security and integrity of the device and the privacy of its owner.
In November, for example, the firm Anubis Networks said that it discovered hidden features in Ragentek Android software that contained a mysterious over-the-air update mechanism that communicates over an unencrypted channel. That could allow a remote attacker to execute arbitrary code on the device with administrator (or “root”) privileges, Anubis said.






