
In-brief: researchers working in Canada and Israel have created a proof of concept Internet worm that spreads between connected devices, including connected lightbulbs, according to a paper published online.
Researchers working in Canada and Israel have created a proof of concept Internet worm that spreads between connected devices, including connected lightbulbs, according to a paper published online.
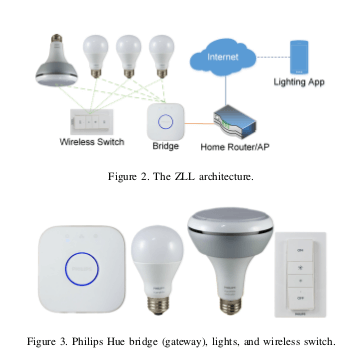
The researchers, from the Weizmann Institute of Science in Rehovot, Israel and Dalhousie University in Halifax, Canada, developed a worm that spreads between Philips brand Hue lightbulbs, jumping from one lamp to surrounding lamps using built-in ZigBee wireless connectivity. They describe an attack launched on bulbs deployed outside using a small drone device equipped with a low-cost sensor.
According to researchers, an outbreak can start with a single bulb, which will begin spreading rapidly to nearby bulbs when it is plugged in. With a critical density of around 15,000 smart lights, the worm could quickly spread to cover a city the size of Paris, though fewer bulbs might cause the infection to fizzle, the researchers said.
To create the worm, the researchers developed a method for disconnecting the bulbs from their network and then flashing (or re-installing) the firmware on them using an over-the-air firmware update mechanism built into the bulbs.
They were helped along by a previously unknown vulnerability in Touchlink, a part of
the ZigBee Light Link protocol. That protocol is supposed to block firmware updates from adjacent devices using a proximity test, but the researchers discovered a means of bypassing that.
Using an inexpensive ZigBee transmitter mounted to a flying drone, the researchers were able to launch attacks against the bulbs in a campus environment from a range of up to 400 meters. The researchers were able to force all the affected bulbs in range to disconnect from their network and respond to malicious commands (specifically: blinking S-O-S in Morse code).
To push the malicious firmware onto the device, the researchers developed a so-called “side channel attack.” Side channel attacks are a way of defeating an encryption algorithm using information from the actual implementation of the crypto system, rather than trying to “break” the cryptography itself.
In this case, the researchers said they were able to extract the global encryption key that Philips uses to encrypt and authenticate new firmware. The researches said they were able to do this using readily available equipment costing only a few hundred dollars and without the benefit of observing any updates to the devices first.
“This demonstrates once again how difficult it is to get security right even for a large company that uses standard cryptographic techniques to protect a major product,” the researchers said.
The demonstration is the first to poke holes in the security of the HUE bulbs. In 2013, for example, researcher Nitesh Dhanjani published information about a flaw that allowed any mobile phone users to send commands to a HUE bulb, making use of common tokens to authenticate wireless commands to the device.
In 2014, researchers at Context discovered that, by gaining access to a “master bulb” in LIFX deployments, they could control all connected lightbulbs and expose user network configurations.
