
Some of the nation’s top experts on cyber security and the Internet of Things urged Congress to take a more forceful approach to securing a burgeoning population of Internet connected devices before security and quality issues undermine consumer confidence.
Members of the House Committee on Energy and Commerce were told in separate testimony that security problems such as the recent denial of service attacks linked to the Mirai botnet will become more common and could threaten the integrity of the Internet and of the nation’s broader economy if left unaddressed.
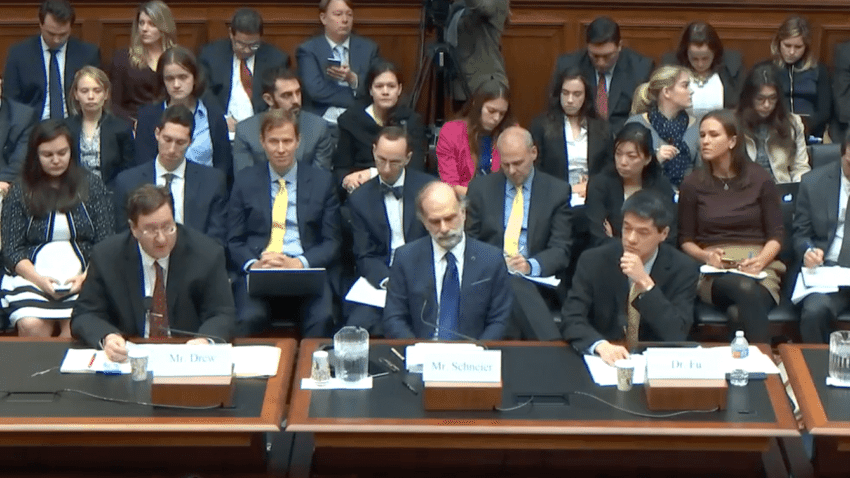
The Committee heard from Dr. Kevin Fu of the University of Michigan, Bruce Schneier of IBM and a fellow at Harvard’s Kennedy School of Government and Dale Drew, the Chief Security Officer of Level3 Communications. All three, to varying degrees, advised a bigger government role in setting standards for devices connected to the Internet. And all three warned that a failure to deal with an epidemic of insecure devices could result in the public rejecting new technology for fear of the implications to their security and personal privacy.
Security problems in software are nothing new, Dr. Fu told the Committee, but the expansion of software-based devices into the physical world has drastically raised the stakes of software insecurity. “One of the core problems with the increasing number of IoT devices is the increased complexity that is required to operate them safely and securely. This increased complexity creates new safety, security, privacy, and usability challenges far beyond the difficult challenges individuals face just securing a single device,” Fu told the Committee.
Bruce Schneier, the Chief Technology Officer at the firm Resilient (now part of IBM) and a Fellow at The Berkman-Klein Center at Harvard University and the Harvard Kennedy School of Government said that the complexity of the Internet itself made it very difficult to secure and tended to favor attackers more than defenders. The inability to secure connected devices represented a clear “market failure,” according to a copy of testimony provided to The Security Ledger. “Basically, the market has prioritized features and cost over security,” Schneier told the Committee. “The teams building these devices don’t have the security expertise we’ve come to expect from the major computer and smart phone manufacturers, simply because the market won’t stand for the additional costs that would require,” Schneier noted.
That point was echoed by Drew of Level 3, an Internet backbone provider with a front row seat for massive distributed denial of service attacks (DD0S). “The global nature of the IoT device marketplace means many products are manufactured in and shipped to foreign countries that have yet to embrace sound cybersecurity practices. IoT devices also are particularly attractive targets because users often have little way to know when they have been compromised,” Drew said.
Fu called on the government to support better security on the Internet of Things in a variety of ways: through support of agencies such as NIST and NSF (National Science Foundation) that can “advance our understanding of how to protect IoT devices and to establish a cybersecurity workforce that meets industry needs.” Fu said the U.S. government should study the feasibility of standing up an independent, national embedded cybersecurity testing facility modeled after the facilities overseen by the National Transportation Safety Board (NTSB) or the Nevada National Security Site.
Recent attacks on sites like Krebsonsecurity.com and the managed domain name system (DNS) provider Dyn in New Hampshire were brief and, essentially, victimless crimes, Fu noted. However, the targets of the massive Mirai botnet that launched those attacks could have been a hospital, disrupting care for patients. Such facilities are already vulnerable to disruptive attacks, he said, “and no one has been able to provide assurance that a future Dyn-like attack will not cause a massive, nation-wide healthcare outage.”
Likening the problem to environmental pollution, Schneier told the Committee, “the only solution is to regulate.”
“The government could impose minimum security standards on IoT manufacturers, forcing them to make their devices secure even though their customers don’t care. They could impose liabilities on manufacturers, allowing companies like Dyn to sue them if their devices are used in DDoS attacks. The details would need to be carefully scoped, but either of these options would raise the cost of insecurity and give companies incentives to spend money-making their devices secure,” according to comments submitted by Mr. Schneier.
Holding up his smart phone, Schneier noted that the nature of the Internet of Things makes simple fixes impossible given the current regulatory model. “For the first time the Internet affects the world in a direct physical manner. “Already the stuff on this device monitors my medical condition, controls my thermostat, talks to my car. Already I’ve crossed four regulatory agencies and it’s not even eleven o’clock,” he said. “This is going to be something that we need to do something new about,” he told the Committee on Wednesday, suggesting that a new agency may be needed to address the problem, as new agencies stood up to address technologies like telecommunications, aviation and automotive transportation.
Schneier also warned against efforts to “deliberately weaken the security of any computing devices at the request of the FBI. Devices like smart phones are becoming the de facto digital hub where we control many of our Internet-of-Things devices. Attempts to weaken encryption will make these attacks easier and more damaging, and will harm our society far more than their benefit to FBI investigations,” he wrote in comments.
The government needs to invest broadly in training cyber security experts and in populating agencies like the FBI with staff with cybersecurity expertise. “Regardless of what you think about regulation vs. market solutions, I believe there is no choice. Governments will get involved in the IoT, because the risks are too great and the stakes are too high. Computers are now able to affect our world in a direct and physical manner.”
As befits Congress and Washington D.C. in general, opinions on the Committee were mixed. Congressman Michael Burgess (R-TX) said he understood how cyber criminals could make a business out of ransomware, but didn’t understand the criminal business model behind compromising a connected doorbell.
Experts explained that even inexpensive connected devices can be powerful when joined with other devices in a botnet.
Fu said that the current status quo was a stalemate between consumer groups who see cyber security as a public good and manufacturers, who want assurances that investments in security will be paid for down the line. Resolving that stalemate was critical in order to get improvements in connected devices, he said.
The testimony came on the same day as The Department of Homeland Security released its own “suggested practices to fortify the security of the IoT.” The agency called for security to be a design-time priority, risk based assessments to prioritize security measures and patching and “transparency” as a means of fending off attacks on Internet of Things systems.

I will say, the number one strategy to grow your observe is by giving good service and the phrase of mouth that is generated from that.
Another would consist for “Paul” to actually check that the video embedded in his report does not present the viewer with 45min and 29s of “nothing” before reaching the first introductory remarks by the committee’s chairman. Editing out the first blank 45 minutes and 29 seconds is easy by any measure.