Researchers at DUO Security claim to have found a way of bypassing a two factor authentication feature that secures logins to Paypal.com, eBay’s online payment service.
The vulnerability could allow an attacker who has stolen a Paypal customer’s user name and password to gain access to the account, even though the customer had enabled the more secure two-factor authentication option.
DUO described the problem in a blog post early Wednesday. According to researcher Zach Lanier, Paypal has published an API (application program interface) for its Security Key two-factor authentication technology that contains a vulnerability that would allow even a non-technical hacker to bypass the second factor when accessing a Paypal customer’s account.
An attacker only needs a victim’s PayPal username and password in order to access a two-factor protected account and send money. “The protection offered by the two-factor Security Key mechanism can be bypassed and essentially nullified,” the company wrote in a blog post.
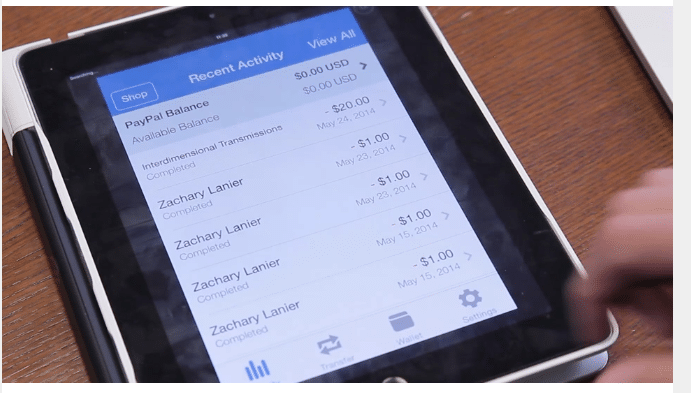
The problem comes up when trying to access a Paypal account protected using two-factor authentication using a PayPal mobile application – for example: on a tablet or smart phone.
PayPal’s mobile apps do not currently support two-factor-enabled accounts and display a message to users who have enabled it for their accounts when those users attempt to log in from a PayPal mobile application. However, Lanier and his colleagues discovered that it is possible to trick the PayPal mobile applications into ignoring that flag on the account and allow an attacker to log in without requiring secondary authentication.
According to DUO, the vulnerability is in the “authentication flow” for PayPal’s API web services. The company’s Web API uses the OAuth technology for user authentication and authorization, but PayPal only enforces the two-factor requirement on the accessing client – not on the server. Researchers at DUO discovered that implementation flaw when they noticed that the PayPal iOS application would briefly display a user’s account information and transaction history prior to displaying an error message saying that the mobile application did not support two factor authentication and logging them out.
The behavior suggested that mobile users were, in fact, being signed in to their account prior to being logged off. The DUO researchers investigated: intercepting and analyzing the Web transaction between the PayPal mobile application and PayPal’s back end servers and scrutinizing how sessions for two-factor-enabled accounts versus non-two-factor-enabled accounts were handled.
The flaw does not affect Paypal sessions that are conducted via a traditional web browser. However, anyone with access to the PayPal mobile API could take advantage of the vulnerability, regardless of the platform they were accessing PayPal from.
DUO says that PayPal has implemented a “workaround” that limits the impact of the vulnerability and is working on a permanent fix. The company did not immediately respond to requests for comment from The Security Ledger.
With a rash of major data breaches that have spilled user name and password info, companies of all stripes have turned to two factor authentication as a backstop to account hijacking and identity theft. The technology asks users attempting to access an online service to enter a username, a password and a unique, one time value- often a numeric code that is transmitted to the user’s mobile phone via text message.
PayPal was one of the first firms to offer a two-factor authentication options to its customers. Other firms have since followed suit, including most banks as well as Google, Twitter, Facebook and others. Use of two factor authentication has grown in recent years, especially after stories like that of Mat Honan gained notice. Honan had his digital life wiped out after attackers compromised his Google Gmail account, Apple ID and Twitter account. Honan noted that using two factor authentication may have kept him from being a victim.
More recently, Reuters web page was defaced by the Syrian Electronic Army after attackers compromised an account at Taboola, an online ad network used by Reuters. Taboola also has claimed that its employee accounts were hacked despite being protected by two-factor authentication.

Pingback: Paypal Disables Two Factor From Mobile | The Security Ledger
Pingback: Trivial Bypass of PayPal Two-Factor Authentication On Mobile Devices | Slash Dot Blog
Pingback: This Week In Security: Poking Holes In Two Factor Authentication | The Security Ledger