It was only a couple weeks back that we wrote about new research from the folks at WhiteHat Security that posited a way for mobile ad networks to be gamed and used to distribute malicious code. Now it looks as if the bad guys were one step ahead, as researchers at Palo Alto Networks reveal new type of malicious Android malware that uses mobile ad networks to infect vulnerable devices.
Palo Alto described the new, malicious mobile software, dubbed “Dplug,” in a blog post on Monday. The company said the malware authors appear to be leveraging second tier mobile ad networks, mostly in Russia and the former Soviet Republics), to distribute their wares. The Dplug malware takes advantage of the deep integration between mobile applications and mobile advertising networks to gain a foothold on infected devices, then send out messages to premium SMS services to generate money for the fraudsters, according to Wade Williamson, a senior security researcher at Palo Alto.
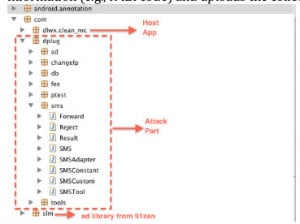
The malware is still rare, relatively. Palo Alto said it collected seven samples of it, mostly from infected systems in Asia. The malware is similar to BadNews, a malicious mobile ad network discovered in April, 2013, Williamson said. However, the architecture and delivery mechanism for the malware is “as interesting as the malware itself,” he said. Mobile ad networks are a key part of the mobile application ecosystem, allowing application developers to give away their creation and recover money from in-app advertisements. Developers typically bundle the mobile ad network code with their own application, then distribute it via mobile ad marketplaces like Google Play.
However, there are many second- and third tier mobile ad networks that perform little vetting of their customers’ ads, or that may be compromised. If those networks can be exploited, malware can be delivered directly to the mobile device by way of the application that the mobile ad network is bundled with.
“The mobile ad network is a kind of ‘dropper’ built into the application,” Williamson told The Security Ledger, using a term that describes a kind of helper program that is used to deposit malicious applications on infected systems. “If the malware isn’t known, the mobile device user won’t know that anything is happening.”
The malware observed by Palo Alto worked by first installing itself in memory. That allowed it to run without requiring user permission to install the malicious code. The malware was programmed to wait for the user to install another application before throwing up a prompt asking for permission to be installed. The authors were clearly hoping that the anonymous pop-up, coming after similar pop-ups from the legitimate application, would quickly be approved by the phone’s owner.
Once resident on the phone, the malicious application sends SMS messages to premium services, and receives SMS format messages from command and control (C&C) servers controlled by the attacker, Williamson said.
At the Black Hat security conference earlier this month, researchers at WhiteHat Security presented research that showed how would-be attackers can parlay a small mobile ad network buy into a sizable browser-based botnet that could be used to send out spam, spread malicious code or launch denial of service attacks on other web sites. One problem is that ad networks do a poor job vetting the javascript that accompanies many online ads that are submitted for circulation. “The folks we dealt with (at the ad networks) didn’t really have the javascript reading skills to know the difference” between legitimate and sketchy code, Johansen told me.
Palo Alto said their research picks up the thread, looking at how mobile ad networks could be leveraged to distribute malware by way of the mobile application ecosystem, rather than by pushing out malicious javascript in the form of mobile ads.
Williamson said there is no easy fix for the problem Palo Alto identified without better industry coordination. “At an industry level, you will need to have reputable, verified mobile application stores,” Williamson said. “Applications need to have a seal of approval,” he said. However, the market dynamics driving mobile phone adoption seem to preclude that. “Android is absolutely dominating the worldwide market for mobile operating systems right now,” he said. “And that’s because its an operating system that is easy to integrate with different platforms and app stores,” Williamson said.
The new mobile malware also marks a progression in the mobile space from simple click fraud to more permanent, mobile botnets capable of launching distributed denial of service (DDoS) attacks and other targeted hacks, he said.
Read more about Palo Alto’s discovery here.

