Editor’s Note: Updated to add comments from Lookout Mobile Security. – PFR 6/10/2013
When reports surfaced about “BadNews,” a new family of mobile malware that affected Google Android devices the news sounded…well…bad. BadNews was described as a new kind of mobile malware for the Android platform-one that harness mobile ad networks to push out malicious links, harvest information on compromised devices and more.
Now, six weeks later, a senior member of Google’s Android security team claims that BadNews wasn’t really all that bad, after all.
Speaking at an event in Washington D.C. sponsored by the Federal Trade Commission, Google employee and Android team member Adrian Ludwig threw cold water on reports linking BadNews to sites that installed malicious programs. The search giant, he said, had not found any evidence linking BadNews to so-called SMS “toll fraud” malware.
“We’ve observed the app(lication) and we’ve reviewed all the logs we have access to,” he said. “We haven’t seen a single instance of abusive SMS applications being downloaded as a result of BadNews,” Ludwig said.
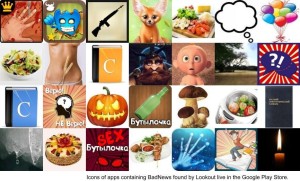
The statement was Google’s first on BadNews since the company pulled 32 applications from its Google Play store on April 20. The suspensions followed reports about the malicious ad network by the mobile security firm Lookout Security on April 19.
Lookout’s Marc Rogers, writing on April 19, said that his company first identified the 32 applications, linked back to four developer accounts on Google Play, the company’s official mobile application store. BadNews was among the first examples Lookout has seen of malicious ad networks in the mobile space. Lookout researchers postulated that the malicious ad network was the next logical step to pushing malware to Android users, after Google began scanning applications on Google Play using its Bouncer application testing technology.
See also: “Bad News: Mobile Attackers Pivot to Malicious Ads“
BadNews operates like a legitimate ad network for a period of time after it is installed, but eventually begins pushing malicious ads out to Android users who have downloaded and installed a mobile app that is bundled with the Badnews software, Lookout warned. The company said Badnews was observed “pushing AlphaSMS, well-known premium rate SMS fraud malware, to infected devices,” mostly in Russia. Many of the infected applications were also targeted at a Russian-speaking audience.

But Ludwig seemed to contradict that account last week. While he acknowledged that Badnews was bundled with 32 Play applications. He also admitted that the applications using the software had been downloaded by a “significant number of people – in the low millions,” he disputed the links to SMS Trojans or malicious web sites, specifically.
Google’s decision to remove the applications and suspend the accounts of four developers was,
Ludwig said, justified by their violation of Google’s Android Developer agreement, not because the applications in question were malicious. “If something is coming down from Google Play, that removal doesn’t necessarily mean that application is bad,” he told the audience at the FTC forum. “We rarely confirm the reasons.”
Asked about Ludwig’s comments, a Google spokeswoman affirmed his claim that Google had no evidence that BadNews was linked to malicious web sites or SMS Trojans.
Contacted by The Security Ledger, Lookout Mobile Security was unable to respond to Ludwig’s allegations specifically, but referred back to its posted research on BadNews.-founder and CTO Kevin Mahaffey said that his company was very confident in its assessment that BadNews was a malicious mobile ad network.
“We’re open to all possibilities. But, having observed the behavior of this ad network at length and analyzed its code, we don’t see any possibilities other than this being a malicious ad network,” Mahaffey told Security Ledger.
In addition to observing the behavior of BadNews, Lookout analyzed the underlying code used to serve ads to mobile device. That analysis revealed that BadNews was substantially similar to another malicious ad network, which Lookout calls “RUPaidmarket.” “There is substantial code re-use,” Mahaffey said. “That indicates that the same person that wrote the RUPaidmarket malware is working on BadNews, as well.”
Asked to explain Google’s assessment that BadNews may not be malicious, Mahaffey said that the organization behind BadNews only pushes malicious ads for short periods of time – as little as five minutes a day. Intermittent scanning of the ad network might easily miss such activity, but any company that observed the network over time would catch it, Mahaffey said.
Ludwig’s reasons for revisiting the BadNews malware aren’t entirely clear. The researcher was participating in a panel discussion entitled “Building Security Into Modern Mobile Platforms,” along with representatives from Blackberry, Apple, Microsoft. His comments were part of a larger argument that Google was adequately managing the security of its Google Play application store, even without the kind of pre-screening of developers and applications that its chief rival Apple conducts. Instead, Google relies on a team of 300 dedicated security engineers and close monitoring of developer activities to spot suspicious or malicious activity – which Ludwig said is rare.
“Every single day we’re learning something new,” he said “It’s like looking for quarter needles in a haystack.”






