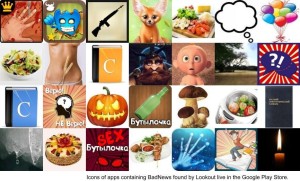
The identification over the weekend of a large-scale outbreak of mobile malware dubbed “BadNews” is bad news, indeed for millions of Android device users, who downloaded applications from the official Google Play application store that connected their devices to a malicious advertising network, dubbed “BadNews.”

The discovery of the malware-infected apps, which were downloaded between two- and nine million times, suggests a new wrinkle in the mobile malware space, with attackers turning to honest-seeming mobile ad networks to push out malicious links and collect information on compromised devices.
“This is one of the first times that we’ve seen a malicious distribution network clearly posing as an ad network,” wrote Lookout’s Marc Rogers on the company blog. He speculated that the new tactic may reflect improved security on the Google Play app store following the introduction of the Bouncer malware scanner.
Lookout said that the company notified Google, which removed the offending applications and suspended the associated developer accounts pending further investigation. Google did not immediately respond to a request for comment.
The BadNews malware was distributed mostly in mobile applications targeted at users in Russia and the former Soviet Republics of Eastern Europe. Among the popular mobile applications found infected were those with names like “Bottle Shoot,” “Savage Knife” and “Stupid Birds” (not angry ones, mind you), as well as pornography applications.
Lookout researchers found that BadNews masquerades as an innocent advertising network for a time, before it begins acting maliciously: sending fake news messages, prompting users to install applications and transmitting sensitive device information to a Command and Control (C&C) server controlled by the cyber criminals. The application also displays fake news messages with links to other malware and applications tied to bogus affiliate marketing schemes.
Lookout researchers observed BadNews pushing copies of AlphaSMS, an SMS Trojan, to users. That malware is intended to leverage premium SMS services, mostly in Russia and the former Soviet republics. The company said BadNews marks “a significant development in the evolution of mobile malware by delaying infection in order to fool gatekeeper functions like Google’s Bouncer.
But a source with knowledge of the BadNews malware, but who asked to speak anonymously, said that warnings about “millions” of infected phones were overblown. “Just having the application installed does not mean any harm has happened to the user,” the source said. Rather, users must be targeted with an attack via the BadNews ad network (say a malicious link) and then take the bait – downloading and installing a malicious application and granting it permissions on the phone, for example. The number of successful second-stage attacks, the source said, is small.
The report comes amid a report by the industry publication AdWeek that suggests that botnet traffic and bogus web sites may be costing advertisers more than $400 million a year. That report, following earlier investigations, identified a number of high traffic sites that revealed suspicious behavior – such as traffic sources that overlap with dozens or even hundreds of other, unrelated sites online.
Lookout recommends that developers pay close attention to “any third-party libraries they include in their applications.” Such re-used code could contain malicious components that risk the reputation of their application and their company.
Enterprise security managers should assume that malicious application behavior may take time to emerge, and may not be identifiable out of the box. Companies need to monitor the security of mobile applications in an ongoing fashion, Lookout advised.
The security of mobile devices is coming under increasing scrutiny – particularly those of Android devices. Last week, The American Civil Liberties Union filed a complaint with the U.S. Federal Trade Commission on Wednesday calling on the Federal Government to take action to stem an epidemic of unpatched and insecure Android mobile devices – a public scourge that the ACLU blames on recalcitrant wireless carriers. Android’s application ecosystem is decentralized and, as a result, easier to compromise than Apple’s AppStore model, which the Cupertino company tightly controls.
Android devices now account for close to 70 percent of new mobile devices sold. The porous security of many of those devices has become a topic of concern. The latest data from Google highlights the challenge facing the company, with just over 16% of Android users running Versions 4.1 or 4.2 – the latest versions of the OS, dubbed “Jelly Bean” more than six months after its release. Forty four percent of Android users are still running the “Gingerbread” release – Versions 2.3.3 through 2.3.7, a two year-old version of the operating system that has known security vulnerabilities. This according to data released by Google on the Android developer blog. In contrast, third party estimates put the market share for iOS 6.x, the latest version of that operating system, at close to 90%. Around 98% of all iOS users running either iOS 6.x or 5.x.

