In this week’s episode of the podcast (#168), sponsored by Signal Sciences, Chris Eng of Veracode joins us to talk about the 10th annual State of Software Security Report and the problem of application security debt. Also, Brendan Macaraeg of Signal Sciences talks about the expanding landscape of web application attacks and defenses.
Mobile
Episode 149: How Real is the Huawei Risk?
In this episode of the podcast we’re joined by Priscilla Moriuchi of the firm Recorded Future, which released a report this week analyzing the security risks posed by Huawei, the Chinese telecommunications and technology giant.
Spotlight Podcast: Flashpoint’s Allison Nixon on SIM Swapping and the Looming Online Identity Crisis
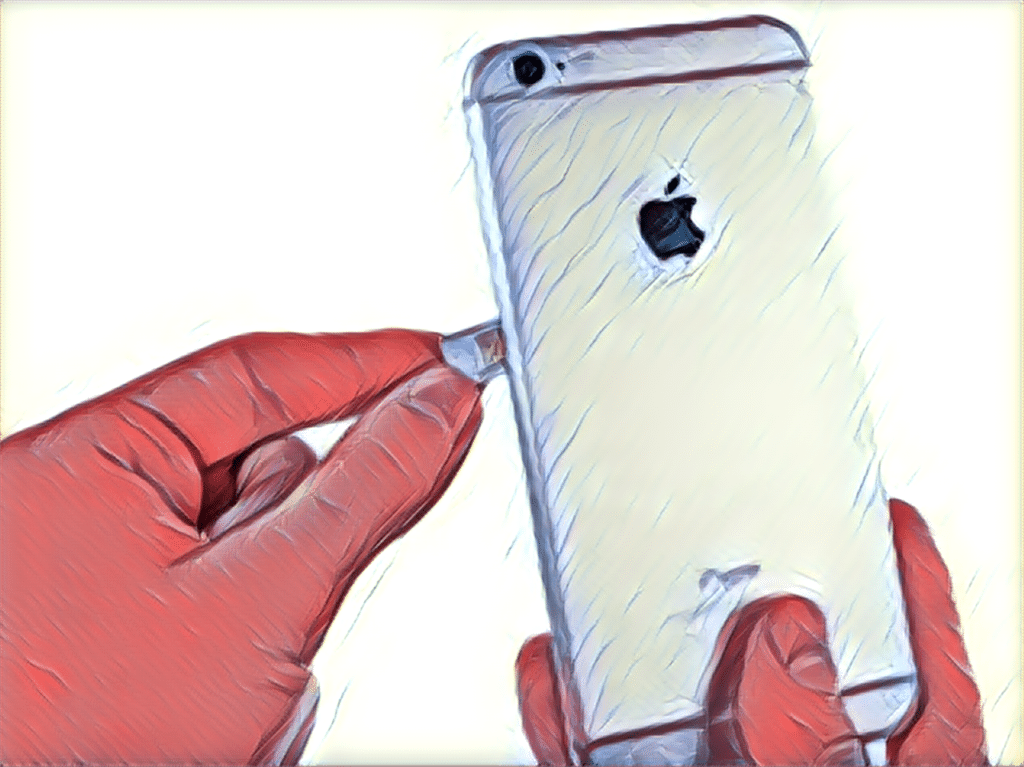
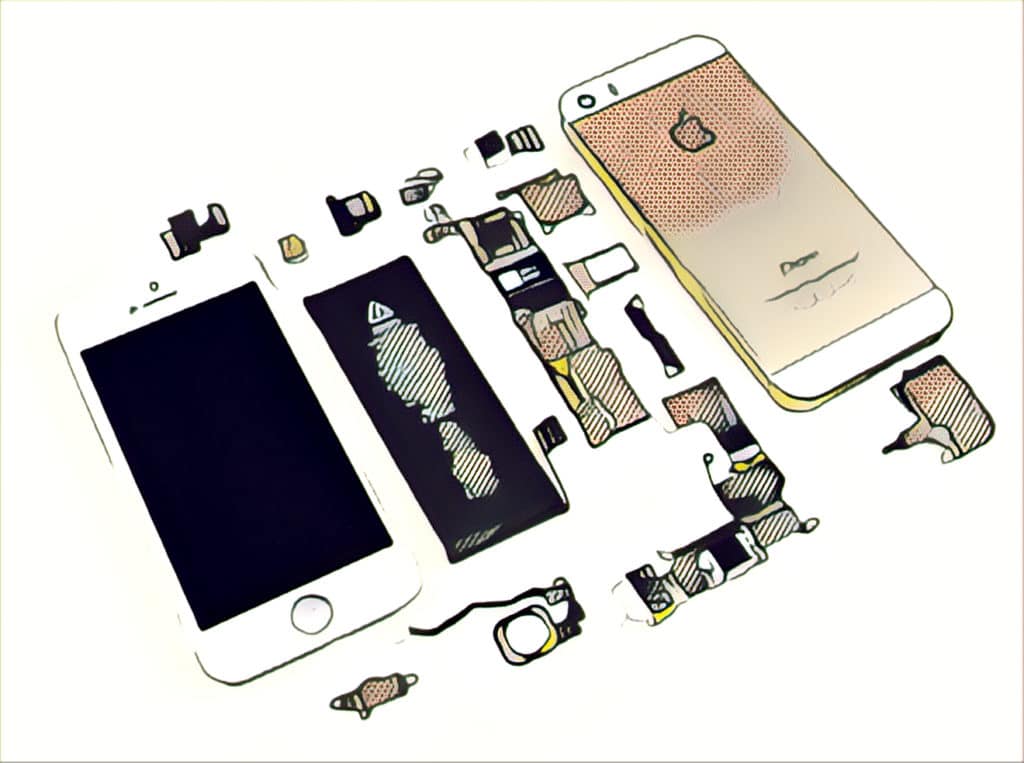
Your smart phone does double and triple duty: letting you do banking, buy a cup of coffee, board a plane or access a sensitive online account. But that doesn’t mean that your phone number is equally as trustworthy. In this Spotlight Podcast, we speak with Flashpoint* head of research Allison Nixon about how a recent rash of SIM swapping attacks highlights a looming crisis in online identity.
FBI exaggerated inability to access encrypted devices in promotion of ‘Going Dark’ problem
The FBI has mislead Congress and the public about the extent to which encrypted cellphones are hampering federal investigations by preventing authorities from accessing the devices–presumably to support the agency’s own agenda to gain backdoor access to them.
BLU settles with FTC over unauthorized transmission of personal customer data to China
Florida-based mobile device maker BLU has settled with the Federal Trade Commission (FTC) over charges it allowed a Chinese partner to collect detailed personal customer information from some of its devices without authorization or consent.