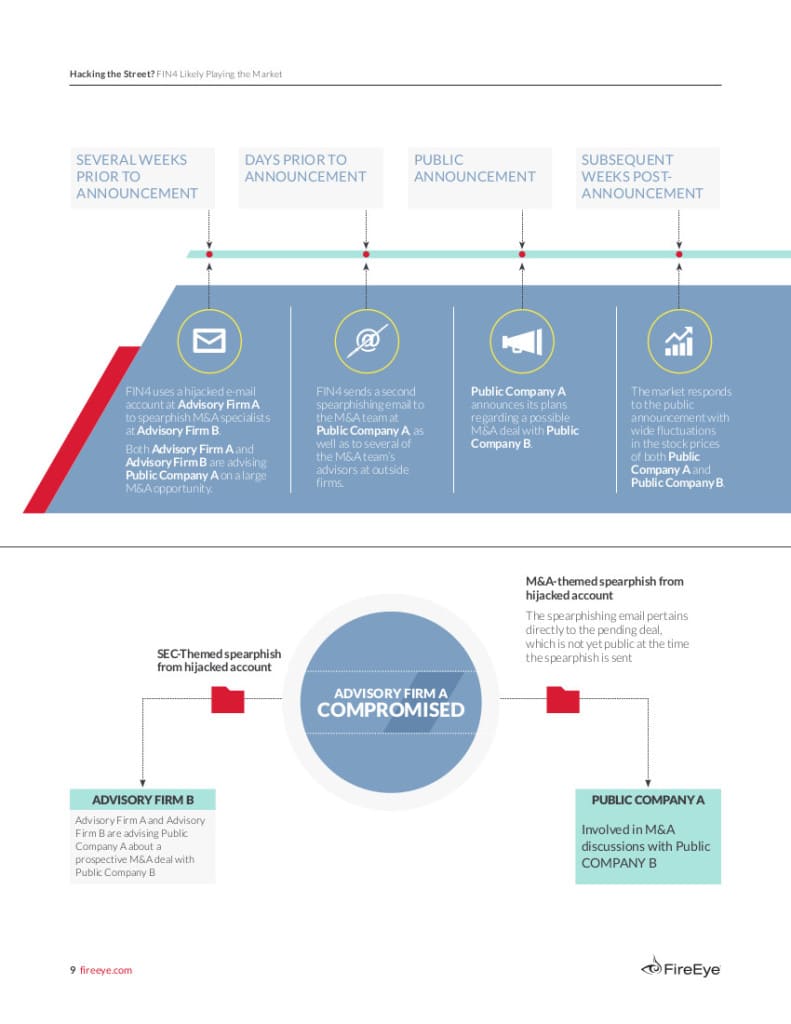
Reuters has the story this morning about a new report out from the folks at FireEye about a cyber espionage ring that targets financial services firms. The campaign, dubbed FIN4 by FireEye, stole corporate secrets for the purpose of gaming the stock market. FireEye believes that the extensive cyber operation compromised sensitive data about dozens of publicly held companies. According to FireEye the victims include financial services firms and those in related sectors, including investment bankers, attorneys and investor relations firms. Rather than attempting to break into networks overtly, the attackers targeted employees within each organization. Phishing e-mail messages led victims to bogus web sites controlled by the hackers, who harvested login credentials to e-mail and social media accounts. Those accounts were then used to expand the hackers reach within the target organization: sending phishing email messages to other employees. The criminals behind FIN4 sought data that could be useful to stock traders, including Securities and […]
Tag: phishing
Discrete Malware Lures Execs At High-End Hotels
Kaspersky Lab has a fascinating write-up of malware it is calling “DarkHotel.” The information-stealing software is believed to target traveling executives. Curiously, Kaspersky says the malware may be almost a decade old and is found only on the wireless networks and business centers of select, high-end hotels. Reports about targeted attacks on traveling executives are nothing new. However, the Kaspersky report (PDF version here) may be the most detailed yet on a specific malicious software family that is devoted to hacking senior corporate executives. According to Kaspersky, the DarkHotel malicious software maintained a presence on hotel networks for years, with evidence of its operation going back as far as 2007. The malware used that persistent access to target select hotel guests, leveraging check-in/check-out and identity information on guests to limit attacks to high value targets. Targeted guests were presented with iFrame based attacks that were launched from the hotel’s website, […]
Customer Support A Weak Link In Two Factor | Ars Technica
Ars Technica has an interesting write-up on an apparently successful compromise of Google’s two-factor authentication technology. Though in this case, the culprit wasn’t any system Google deployed or managed, but a gullible customer support representative working for the victim’s cell phone carrier. According to this post over at Facebook-for-hipsters site Ello.co, Grant Blakeman woke up on a recent Saturday morning to find that his Google account had been hijacked – despite the fact that he used Google’s two-factor authentication to protect access to the account. How? Blakeman enlisted the help of none-other than Mat Honan, whose own struggles with account hijacking became the subject of a much-cited Wired feature article. As with Honan, Blakeman’s valuable three-character Instagram account, @gb, appears to have been the lure for hackers. (Honan’s @mat Twitter account was what lured his attackers.) Read “Researchers sidestep Paypal Two-Factor Authentication.” After a conversation with Honan, Blakeman contacted his cell provider and […]
Dusting For Malware’s Bloody Prints
Malicious software is nothing new. Computer viruses and worms have been around for decades, as have most other families of malware like remote access tools (RATs) and key loggers. But all our experience with malware hasn’t made the job of knowing when our organization has been hit by it any easier. In fact, recent news stories about breaches at Home Depot, Target, Staples and other organizations makes it clear that even sophisticated and wealthy corporations can easily overlook both the initial compromise and endemic malware infections – and at great cost. That may be why phrases like “dwell time” or “time to discovery” seem to pop up again and again in discussions of breach response. There’s no longer any shame in getting “popped.” The shame is in not knowing that it happened. Greg Hoglund says he has a fix for that latter problem. His new company, Outlier Security, isn’t “next generation […]
Europol Warns of Internet of Things Risk
In a newly released report, Europol’s European Cybercrime Center (EC3) warns that the growth of the Internet of Things (IoT) threatens to strengthen the hand of organized cyber criminal groups and make life much more difficult for police and governments that wish to pursue them. EC3’s latest Internet Organized Crime Threat Assessment (iOCTA) says the “Internet of Everything” will greatly complicate the work of law enforcement creating “new opportunities for everything from cyber criminals to state actors to child abusers. The growing numbers of connected devices will greatly expand the “attack surface” available for cyber criminal activity, the EC3 warns. Cyber criminals may co-opt connected devices for use in common criminal activity (like denial of service attacks and spam campaigns). However, advancements like connected (“smart”) vehicles and infrastructure create openings for large scale and disruptive attacks. The report, which was published late last months, is a high level position paper and pulls data mostly […]