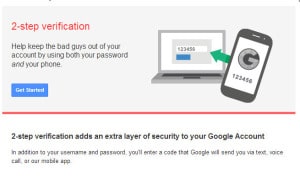
Ars Technica has an interesting write-up on an apparently successful compromise of Google’s two-factor authentication technology. Though in this case, the culprit wasn’t any system Google deployed or managed, but a gullible customer support representative working for the victim’s cell phone carrier.
According to this post over at Facebook-for-hipsters site Ello.co, Grant Blakeman woke up on a recent Saturday morning to find that his Google account had been hijacked – despite the fact that he used Google’s two-factor authentication to protect access to the account.
How? Blakeman enlisted the help of none-other than Mat Honan, whose own struggles with account hijacking became the subject of a much-cited Wired feature article. As with Honan, Blakeman’s valuable three-character Instagram account, @gb, appears to have been the lure for hackers. (Honan’s @mat Twitter account was what lured his attackers.)
| Read “Researchers sidestep Paypal Two-Factor Authentication.” |
After a conversation with Honan, Blakeman contacted his cell provider and found that someone enabled call-forwarding on his cell account without his knowledge. The call-forwarding resulted in Google authentication codes sent to Blakeman’s phone to be forwarded to the attackers. After gaining access to the Gmail address, hackers were able to compromise the Instagram account linked to it.
The story points out an interesting ‘weakest link’ problem with 2FA schemes: cell phone carriers. Many otherwise security-conscious users may apply a different standard to the web site we use to manage our mobile phone accounts. And, even if they don’t, mobile phone carriers are inundated with legitimate customer service calls every day. Account hijacking attempts are a vanishingly small sliver of those calls and a problem that front line customer support representatives aren’t likely to be on the lookout for.
One security ‘pro tip’ from all this (to add to your list): set up a voice authorization code with your mobile phone provider that must be given before a customer service representative can make changes to your account!
Read more via Cell carrier was weakest link in hack of Google, Instagram accounts | Ars Technica.