Kaspersky Lab has a fascinating write-up of malware it is calling “DarkHotel.” The information-stealing software is believed to target traveling executives. Curiously, Kaspersky says the malware may be almost a decade old and is found only on the wireless networks and business centers of select, high-end hotels.
Reports about targeted attacks on traveling executives are nothing new. However, the Kaspersky report (PDF version here) may be the most detailed yet on a specific malicious software family that is devoted to hacking senior corporate executives.
According to Kaspersky, the DarkHotel malicious software maintained a presence on hotel networks for years, with evidence of its operation going back as far as 2007. The malware used that persistent access to target select hotel guests, leveraging check-in/check-out and identity information on guests to limit attacks to high value targets.
Targeted guests were presented with iFrame based attacks that were launched from the hotel’s website, where executives would go to connect to the hotel’s wi-fi network. The iFrames, which were tailored to the specific visitor, asked them to update a common software component, such as Adobe Flash. By clicking on the update link, executives had the DarkHotel malware installed on their system.
| Read more Security Ledger coverage of Advanced Persistent Threat (APT) attacks here. |
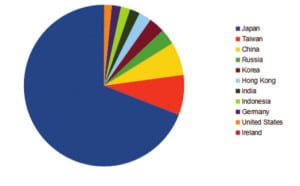
Targets include individuals with ties to defense industrial base (DIB) firms as well as government- and non-governmental organizations. The majority of attacks were recorded in Japan.
Kaspersky believes that attacks were targeted at specific guests and only lasted as long as the executive’s stay. Malicious iFrames and associated executables were removed after the guest targeted in the attack had left the hotel, making it more difficult for the malware to turn up in any scans or audits of the hotel network.
Kaspersky said the DarkHotel is interesting in that it combines elements of both indiscriminate ‘watering hole’ attacks, and more targeted spear phishing campaigns. Like watering hole attacks, the DarkHotel operation relied on victims coming willingly to a compromised asset (the hotel’s web page), rather than pushing attacks out to the victim. However, the use of specific information on the guest culled from compromised registration systems were used to create very focused spear-phishing like attacks on those guests who visited the watering hole site.
Paradoxically, Kaspersky also found evidence of the same malware being spread indiscriminately on peer-to-peer (P2P) sharing sites in Japan and over bittorrent.
According to Kaspersky, the Darkhotel malware is associated with a number of known malware families and keyloggers including Tapaoux, Pioneer, Karba and Nemim. The group responsible for it has used zero day exploits for popular platforms like Internet Explorer and Adobe Flash – a signal that the group is both sophisticated and/or well-financed.
Read more of Kaspersky’s analysis of DarkHotel here.
