The top news this week is about Wall Street giant JP Morgan Chase, which disclosed on Thursday that a previously disclosed breach was much larger than initially believed, affecting more than 75 million account holders. And once again, reports suggest that a compromised employee account may be at the root of the incident. Bloomberg, which first broke the news of the cyber attack on JPMorgan Chase in August, said on Friday that hackers exploited an employee’s access to a development server as part of an attack on a JPMorgan Chase & Co. server that led to one of the largest cyber-attacks ever and the theft of data on 76 million households and 7 million small businesses. According to the Bloomberg report, which cited “people familiar with the bank’s review,” the breach started in June when an employee’s user name and password for what’s described as “a web-development server” were compromised. From that […]
Tag: phishing
Report: Apple IDs Targeted by Kelihos Botnet
There’s an interesting post over on Symantec’s blog about a shift noted in the behavior of the Kelihos botnet in recent days. According to Symantec, Kelihos operators have turned their attention to Apple customers, launching a phishing email campaign aimed at Apple iCloud users and Apple ID’s and passwords. According to the post, Symantec has observed Kelihos (also known as Waledac) being used to send spam emails purporting to be from Apple, informing the victim that a purchase has been made using their account on the iTunes Store. Samples of the emails discovered by Symantec bear the subject line “Pending Authorisation Notification.” The body of the phishing email says that the victim’s account has been used to purchase the film “Lane Splitter” on a computer or device that hadn’t previously been linked to their Apple ID. The email gives an IP address that was used to make the alleged purchase and […]
What Hollywood Can Teach Us: Passwords Matter More Than Ever
Andrey Belenko had what you might call a ‘brush with infamy’ earlier this week after a presentation he took part in on the security of Apple’s iCloud became a set piece in the news media scramble to identify the source of a huge trove of leaked celebrity photos – many depicting Hollywood A-List stars in various states of undress. “It’s not the kind of attention you want to receive,” said Belenko, a security researcher with the firm ViaForensics. “It’s all really creepy stuff.” Belenko’s link to the celebrity hacking scandal was a matter of happenstance. He was scheduled to give a presentation at a small, St. Petersburg multi-media conference, Chaos Constructions, over the weekend. Belenko was presenting research he had conducted a year earlier on the security of Apple’s KeyChain technology and iCloud – a talk he had given twice before in the last year. Prior to his talk, Belenko […]
Update: Cyber Spies Digging For Clues On Iraq?
The folks over at CrowdStrike have dug deep into a campaign of targeted cyber attacks targeting Washington D.C. think tanks and say they have evidence that whomever is behind the attacks has taken a sudden interest in U.S. policy towards Iraq. Editor’s Note: This story was updated to include comments from Adam Meyers, Vice President of Security Intelligence at CrowdStrike. – PFR July 8, 2014 14:30 Writing on Tuesday, CrowdStrike CTO Dmitri Alperovitch described a new campaign by a group they dubbed “DEEP PANDA” that was targeting think tanks specializing on U.S. foreign policy and national security. Alperovitch said CrowdStrike observed a pronounced shift in targets from think tank experts on Asia to experts on Iraq and the Middle East in recent weeks. The shift corresponded with the rapid escalation of violence in Iraq as the Islamic extremist group ISIS took control of large parts of the country. “This actor, who was engaged in […]
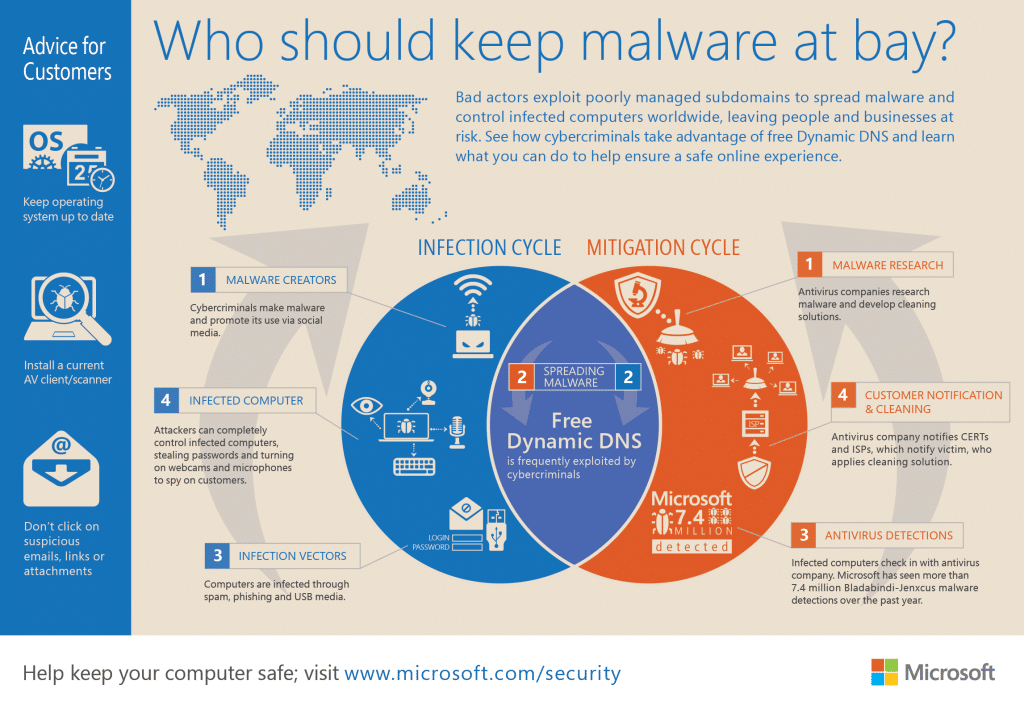
Microsoft Uses Courts To Take Down Malicious, Managed DNS Services
Microsoft Corp. has taken action against yet another cyber crime network, taking control of- and shutting down a managed DNS (domain name system) operated by the firm No-IP that were being abused by cyber criminals, the company said on Monday. The domains were associated with malware families named Jenxcus and Bladabindi that are believed to have infected on some 7.5 million systems, globally. The malicious programs – which are used to spy on the operators of infected systems – use Dynamic DNS services like NO-IP to communicate with command and control systems used to manage infected systems. Dynamic DNS makes the malicious systems more difficult to trace. In a post on Microsoft’s Digital Crimes Unit blog, Richard Domingues Boscovich, the company’s Assistant General Counsel said that the company had filed a civil case on June 19 naming two foreign nationals: Mohamed Benabdellah and Naser Al Mutairi along with a U.S. company, Vitalwerks Internet Solutions, LLC (doing […]