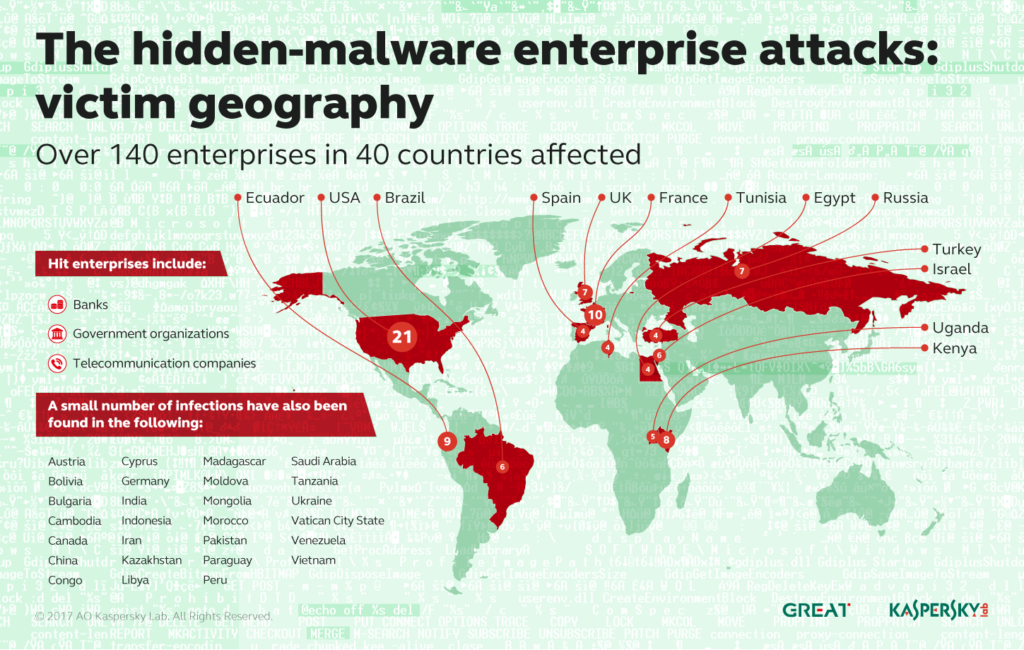
In-brief: Security experts are warning that so-called “file-less” attacks on commercial networks operated by banks and other firms are spreading and harvesting sensitive information, like administrator user names and passwords.
command and control
Clues in language often tip hacker’s hand | CSMonitor.com
In-brief: forensic investigators are using language clues to help identify the source of sophisticated and targeted attacks, like those on Democratic Party committees and the campaign of Hillary Clinton.
Black Hat: Talent Scarce, Firms Look to Automation and Ai
In-brief: with security talent scarce, experts at the Black Hat Briefings say that security automation fueled by machine learning and data analytics is going to play an increasing role in security operations.
Report finds Hackers Delving Deep Into Compromised Networks
In brief: A report studying compromised networks from the firm Vectra finds a big jump in “lateral movement,” as hackers delve deeper into hacked organizations.
Everything Tastes Better with Bluetooth: Understanding IoT Risk
In-brief: Marc Blackmer of Cisco says that, with so much promise, it can be hard to anticipate how individual or company-wide decisions to embrace the IoT might bear on cyber risk.