
In brief: A report studying compromised networks from the firm Vectra finds a big jump in “lateral movement,” as hackers delve deeper into hacked organizations.
Hackers are delving deeper into compromised corporate networks by moving “laterally,” hopping from one system to another, a report from the firm Vectra contents.
The 2015 Vectra “post intrusion report” surveyed networks of 42 customer organizations, comprising close to 250,000 hosts and found big jumps in certain kinds of malicious behavior. Among them: instances of “lateral movement” by malicious actors within organizations, which jumped more than 500% over the previous year.
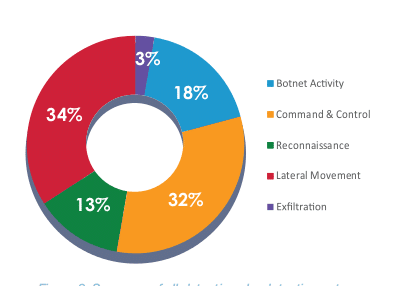
Vectra collected data over a six-month period. The company deploys network monitoring hardware on customer networks to gather the data, which customers agreed to share anonymously. It documented more than 46,000 threat detection within the 40 customers it surveyed. The company grouped them into one or more categories of persistent attacks: botnet monetization, command and control, internal reconnaissance (port scanning), lateral movement and data theft.
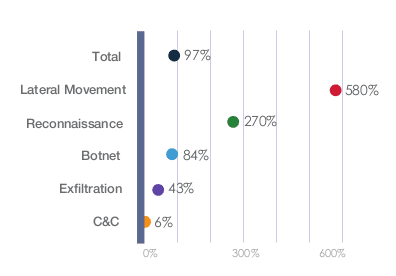
The company found the biggest jump in lateral-movement detection, which track the internal spread of malware and authentication-based attacks such as the use of stolen passwords. That kind of activity jumped 580% over the previous year. (It is worth noting that Vectra’s sample size also increased some 122% over the previous year.)
Lateral movement characterized 34% of all threat identifications the company made, followed closely by so-called command and control detection, which characterized 32% of all threat identifications.
Brute-force attacks accounted for 56 percent of all lateral movement activities followed by automated replication (as with malware), at 22 percent. Interestingly: Kerberos-based attacks were used in 16 percent of lateral movement incidents, a big jump from last year. That may reflect recent, exploitable vulnerabilities discovered in Microsoft’s implementation of Kerberos (a network authentication protocol), as well as published research about methods for compromising Kerberos deployments.
Among the findings of the “post intrusion” report: detection of Tor and external remote access behavior grew significantly, while activity linked to command and control networks increased only slightly. Specifically: Tor detection jumped by more than 1000 percent compared to last year’s survey, accounting for 14 percent of all command-and-control traffic. Overall, external remote access shot up by 183 percent over last year, with encryption of data communications (mostly using HTTPS) also on the rise.
“The increase in lateral movement and reconnaissance detection shows that attempts at pulling off targeted attacks continue to be on the rise,” said Oliver Tavakoli, Vectra Networks CTO, in a statement. “The attackers’ batting average hasn’t changed much, but more at-bats invariably has translated into more hits.”
The report comes amid continuing revelations about long-running compromises at the Office of Personnel Management. Reports over the weekend shed further light on that incident, revealing that attackers with links to China operated undetected on the OPM network for nearly a year, using “administrator privileges” into the computer networks at the Office of Personnel Management to move with impunity and siphon out reams of personnel data on U.S. government employees, including those seeking access to classified information.

Pingback: Report: Hackers Delve Deep Into Compromised Networks – The Threat Vector
Compromised networks are usually shared or sold with many. Just a matter of taking credits or making money. Make no mistake. Its going to take many years before internet security is at a decent level.