In-brief: A hidden, backdoor account affects a line of VoIP gateways made by DblTek, researchers from TrustWave found. The manufacturers fix, however, may not solve the problem.
Customers using Voice over IP (VoIP) products sold by the firm DblTek beware: researchers at the firm Trustwave discovered what appears to be a backdoor administrative account that could affect a wide range of products, giving unauthorized users or hackers total control over the devices.
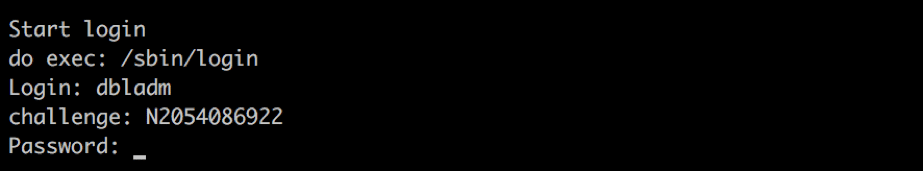
Writing on the Trustwave blog on Thursday, researcher Neil Kettle said that his team discovered the existence of a hidden administrator-level Telnet account, “dbladm” that provides root level Telnet access (super administrator) access to the device. The hidden account is protected by what Kettle describes as a “proprietary challenge-response authentication scheme” that can be reverse engineered, leaving the devices vulnerable to skilled attackers.
Trustwave researchers said that the account was found in firmware used by DblTek’s GoIP GSM Gateway, which allows organizations to bridge GSM (cellular) and IP networks, allowing individuals to use GSM based cellphones with a VoIP switch.
Hidden (or “back door”) accounts are a common problem among device makers and are often slipped into the software (or “firmware”) that operates networking equipment and machinery to allow technicians to remotely support the equipment. Back doors have also been surreptitiously placed in networking gear as part of sophisticated APT campaigns, likely orchestrated by state actors.
In the case of DblTek, the problem appears to be a failure of imagination. Rather than set a static password for the dbladm account, however, DblTek fashioned a more complex challenge-response scheme that presents a unique numeric value to the user which is needed to generate a valid password – in the form of an MD5 hash- to access the device whenever the dbladm user name is entered.
[Read more Security Ledger coverage of supply chain security issues]
Alas, analysis of the firmware by Trustwave engineers revealed that DblTek firmware used a relatively simple, linear equation to generate the unique value needed to log in. That means that anyone with knowledge of the challenge, the equation used to compute a response and the protocol used can create a valid password for the device, Trustwave warned.
It isn’t clear how many DblTek devices are affected by the hidden account issue. TrustWave said its researchers first discovered the issue in an 8 port DblTek VoIP GSM Gateway. Subsequently, it discovered the flaw was also present in GoIP 1, 4, 16 and 32 models, as well. (These are identical hardware, just sporting support for fewer or more SIM cards and lines.)
However, TrustWave notes that most of the devices DblTek manufacture use the same login binary in their firmware as the GoIP devices. “We’re reasonably confident it will be a consistent feature across their product ranges,” Kettle of TrustWave wrote.
TrustWave researchers reported the issue to DblTek on October 13 and a patch was issued on December 21, 2016. However, engineers at DblTek merely replaced the challenge response mechanism with a more complex – but still reverse-able and reproducible equation.
“It seems DblTek engineers did not understand that the issue is the presence of a flawed challenge response mechanism and not the difficulty of reverse engineering it,” Kettle wrote. “The main differences between the latest challenge response mechanism and the older variant is the level of complexity it employs: a simplistic MD5 with a linear equation changed to several ‘round’ functions mixed with a modified version of the MD5 hash algorithm.”
Flaws in hardware and software supply chains can be felt far and wide. In just the most recent example, weak, default credentials associated with software made by XiongMai Technologies was abused by cyber criminals to install the Mirai “bot” software on hundreds of thousands of DVR, NVR (network video recorder) and IP cameras globally.

The problem with everything that has been done over the past 30 – 40 years, is the skills base has moved to the far east due to cost. These may not be the only devices that have backdoors. At around the turn of the millennium when all the methods for computing and communicating was reliable, and all the vulnerabilities weren’t discovered you never heard of this level of exploitation. Then the dot bomb crash happened with the market. The skills base scattered, and to cheapen labor a lot of the work was out sourced to China. What’s the matter with the workers and skills base here in the west? Is it because none of you want to pay for a quality product built under ethical guide lines. The worst part is everyone is whining about national security, when purchasing from a foreign entity that runs under an authoritarian government is preferred because of cost. Democratically it has been a choice to sell national security, and jobs. Which in turn creates national security on a democratic level. Look inward and point the fingers at yourselves before you buy a piece of junk that has been dumped on our shores. You’re better off not buying anything at all for the grief it causes you.