In-brief: security experts say the 13 page report, released Thursday, falls well short of offering conclusive evidence of Russian involvement in the hacking, even as The Obama Administration acts to punish Russia for its involvement.
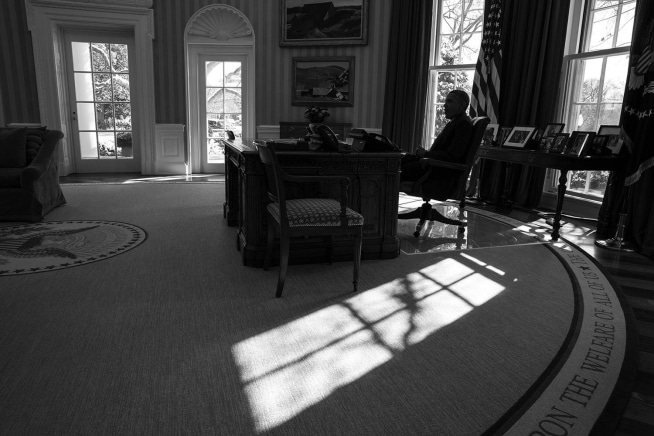
The Obama Administration came clean with the dirt on hacking efforts that coincided with the recent U.S. presidential election, pointing the finger of blame squarely at the Government of Russia.
But security experts say the 13 page report, released Thursday, falls well short of offering conclusive evidence of Russian involvement in the hacking, even as The Obama Administration expelled dozens of Russian diplomats from the country that it accused of spying.
The FBI and US Department of Homeland Security’s consensus report said that a campaign dubbed “Grizzly Steppe” was the work of “Russian civilian and military intelligence Services” and sought to “compromise and exploit networks and endpoints associated with the U.S. election,” and other U.S. government, political and private sector entities.
Though not mentioned in the report, the report represents the government’s analysis of hacking campaigns targeting the Democratic National Committee, the Democratic Congressional Campaign Committee (DCCC) and other political organizations during the 2016 presidential campaign.
The report largely echoes the findings of private sector analysis by firms like Crowdstrike, claiming that two different Russian hacking groups participated in the intrusion into the unnamed “U.S. political party.” The first actor group, known as Advanced Persistent Threat (APT) 29,
entered into the party’s systems in summer 2015, while the second, known as APT28, entered in
spring 2016, the report concludes.
As evidence, the report presents a range of “indicators of compromise” that are associated with each hacking crew. Among them: the use of certain types of attacks to gain a foothold on target networks, the use of specific malicious software programs and a reliance on certain online systems for command and control of infected systems and on specific “operational infrastructure” to cover their tracks and host data stolen from victims.
The report shares some threat signatures specific to the attack and lists dozens of groups that the U.S. government associates with Russian government cyber offensive operations, though it is unclear how many of the listed groups may have played a role in the specific hacking campaigns against Democratic party organizations and the U.S. election.
But security experts say the report, at least as presented, is far from conclusive, and may even muddy the waters on Russia’s culpability in the hacking of the U.S. election.
“The GRIZZLY STEPPE report reads like a poorly done vendor intelligence report stringing together various aspects of attribution without evidence,” wrote Robert Lee, the CEO and Founder of the critical infrastructure cyber security company Dragos and a National Cybersecurity Fellow at New America.
Among other things, Lee notes that the report’s list of Russian cyber ‘actors’ lumps in the names of malware associated with nation-state actors (like Black Energy) with specific cyber operations, creating confusion about what exactly the purpose of the list is. And, while the report may be more about educating the public how to look for Russian hacking campaigns in their own environments, the statements about attribution create an expectation that it will make solid line connections between evidence and actors, when none is offered, Lee said.
In addition, much of the evidence presented was already known. And, at this late date, is equally associated with cyber criminal activity as with nation-state sponsored hacking, said Ron Gula, the founder of security firm Tenable. That is causing many in the threat intelligence community to question the value of the data, he said in an email.
Lee notes that the full extent of what the government knows is still classified. That will likely be put into a report prepared by the Intelligence Community and presented to Congress. Parts of that report may later be declassified and released to the public. However, the most recent statements create the impression that the evidence presented on Thursday is the government’s proof against the Russians – and that’s a problem, Lee wrote.
The Obama Administration has cited the proof of hacking as one cause for taking action against a wide range of Russian interests in the U.S. Among other things, President Obama sanctioned nine entities and individuals operating within the country: two Russian intelligence services (the GRU and the FSB); four individual officers of the GRU; and three companies that provided material support to the GRU’s cyber operations.
Given the challenges facing the U.S. government and U.S. critical infrastructure, the focus on attribution may, itself, be an unnecessary distraction, said Joshua Corman, the Director of the Cyber Statecraft Initiative at The Atlantic Council.
“Everyone is focused on attribution, but we may be missing the bigger truth.” Namely: “that the level of sophistication required to do this hack was so low that nearly anyone could do it.” Rather than quibbling over indicators of compromise, Corman believes that political leaders in Washington D.C. should come together to focus on strengthening the nation’s cyber defenses and making critical infrastructure – including our elections – more resilient to attack.
Such a focus would make the country better able to defend itself in the future, while steering clear of politically charged debates about how to assign blame for past incidents. “We have to change,” Corman said. “We appear to have chosen the one topic to focus on that gets entangled with partisanship and politicization, instead of focusing on a renewed commitment to defending our nation’s critical institutions,” he said.

Whenever an individual is shopping for Chaturbate tokens, from Chaturbate’s
end, it’s a-4 stage process.
What’s up to every single one, it’s genuinely a good
for me to visit this website, iit coontains valuable Information.
As the author concludes, the level of sophistication required to perform these hacks is so low that potentially anyone over the age of fourteen with moderate computer hacking skills could have accomplished these acts. While it’s plausible Putin authorized these attacks, it’s also just as likely that my grandmother did as well.