In-brief: The security firm Anubis Networks said in a blog post that it has discovered a mystery code by the firm Ragentek that is used in a number of low-cost Android smart phones, used across 55 different device models.
Another week, another warning about fishy mobile phone firmware from a little-known vendor.
Last week, the news was about software in Android phones that was sending contact information and text messages to servers in China. This week, the warning is about the discovery of a hidden software application lurking in more than 2.8 million devices that performs secret, over the air updates.
The security firm Anubis Networks said in a blog post that it has discovered a mystery code by the firm Ragentek that is used in a number of low-cost Android smart phones, used across 55 different device models.
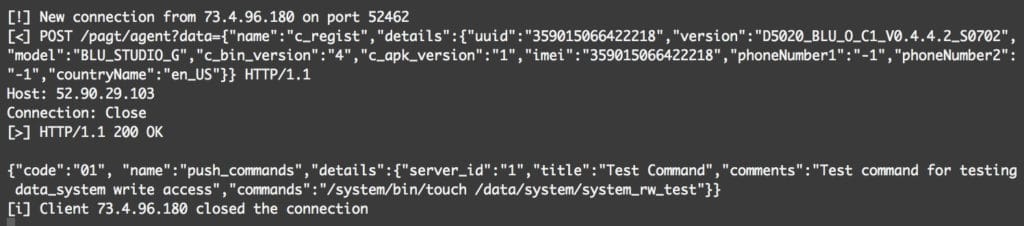
Ragentek Android software contains a mysterious over-the-air update mechanism that communicates over an unencrypted channel. That could allow a remote attacker to execute arbitrary code on the device with administrator (or “root”) privileges.
More troubling: the researchers uncovered various parts of the Rangentek software that appear designed to hide the execution of the application. A warning from Carnegie Mellon University’s CERT noted “this behavior could be described as a rootkit.”
Analysis by Anubis identified three domains that the application communicates with and determined that those servers respond to requests sent by mystery application, including commands for executing arbitrary commands, installing applications and updating mobile configurations.
Only one of the three domains was registered at the time of the discovery. An adversary who registered one of the other domains would have been able to “perform arbitrary attacks on almost 3,000,000 devices without the need to perform a Man-in-the-Middle attack,” Anubis said. The company has since taken control of the two unused domain names to prevent such an attack from occurring.
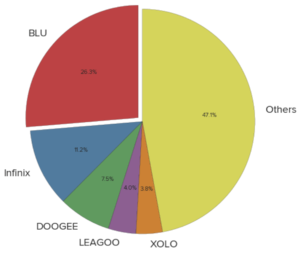
Among the phones affected are the BLU phone that was the subject of an analysis by the firm Kryptowire after the low-cost smart phones were observed sending text messages, phone contacts and other data back to servers in China.
But the impact of the RagenTek software goes well beyond BLU, affecting device manufactured by low-cost phone makers like Infinix, Doogee, Leagoo and Xolo.
Anubis said that, after registering domain names hard-coded into the RagenTek firmware, it observed more than 2.8 million devices across 55 device makers trying to reach them. The company was not able to fingerprint all those devices, meaning many other devices could be affected.
Source: Ragentek Android OTA update mechanism vulnerable to MITM attack

