
In-brief: A new start-up, Senrio, unveiled its Sensor this week: a new security monitoring tool that can identify and monitor embedded devices connected to your network and spot anomalous or malicious behavior.
A couple of months back I was working on an intriguing story about a brand of network gear known as a remote power management (or “RPM”) device that was exhibiting some strange behavior. Specifically: there were reports that one specific type of RPM was sending spoofed and encrypted traffic to suspicious domains in China, Europe and elsewhere.
The reports were a concern. RPM devices basically act as network-attached power outlets. Malicious actors who controlled one could, with a simple keystroke, shut the power off for whatever equipment was plugged into the RPM – a server in a data center, a medical device or a critical piece of industrial equipment. The possibilities were endless.
The question remained: was this one case of an insecure RPM device that was a “target of opportunity” for hackers, or was something bigger and more nefarious going on: a compromise somewhere in the (sketchy) supply chain that delivered these low-cost devices to companies in the U.S., Canada, Australia and elsewhere?
To answer that question, I turned to my friend Stephen Ridley, whose firm Senrio (fka Xipiter) is one of the top embedded device security consulting firms around. My question was simple enough: tell me if these RPM devices are just insecure (poorly designed, poorly deployed and vulnerable) or whether they’re malicious (compromised “out of the box” and used for nefarious purposes).
Those are seemingly simply questions that are actually hard to answer. There’s no shortage of tools that can analyze the behavior of traditional technology assets: the desktops, laptops, servers, switches and routers that make up most enterprise networks. But if you want to understand how the growing population of network-connected and embedded systems behave – what’s “normal” and what’s “weird” – you’re out of luck.
And these are hardly edge cases. Medical devices, smart meters and the kinds of industrial controllers that manage assembly line equipment, elevators and HVAC systems are increasingly “talking IP” and deployed on standard networks alongside more traditional IT assets. But companies have hardly any visibility into risk posture and the behavior of these devices and, as such, are vulnerable to attack by malicious actors who are savvy enough to go after them.
The solution, for large companies, is to hire their own embedded systems engineers to study these devices, or third-party penetration testing and analysis firms to do that research for you. But throwing bodies at the problem isn’t a solution that “scales,” as tech industry folk like to say.
Back when I was working on my story, Stephen and Senrio were getting ready to launch a new product that did exactly that: using machine learning to gain operational visibility into the existence and behavior of embedded devices.
They agreed to use it on the RPM devices I was writing about…but they weren’t yet ready to talk about what their product. Just this week (Thursday, to be exact), Senrio finally unveiled their eponymous Sensor technology to the world.
According to Stephen, the goal is to break out of the torpor of embedded system and IoT “show hacking” that has dominated the information security conversation for the last decade.
Stellar researchers like the late Barnaby Jack, Chris Valasek and Charlie Miller have done the yeoman’s work of exposing embedded device insecurity. But what changes have resulted from those demonstrations? Some emergency patches, sure. But if you step back and look at the embedded device space as a whole, its hard to find any evidence of durable progress.
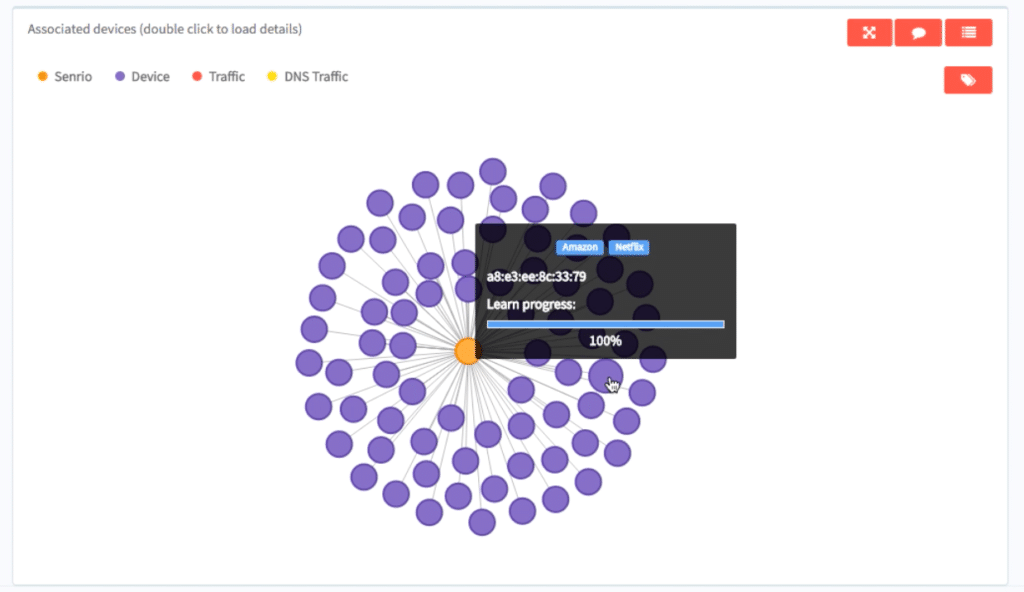
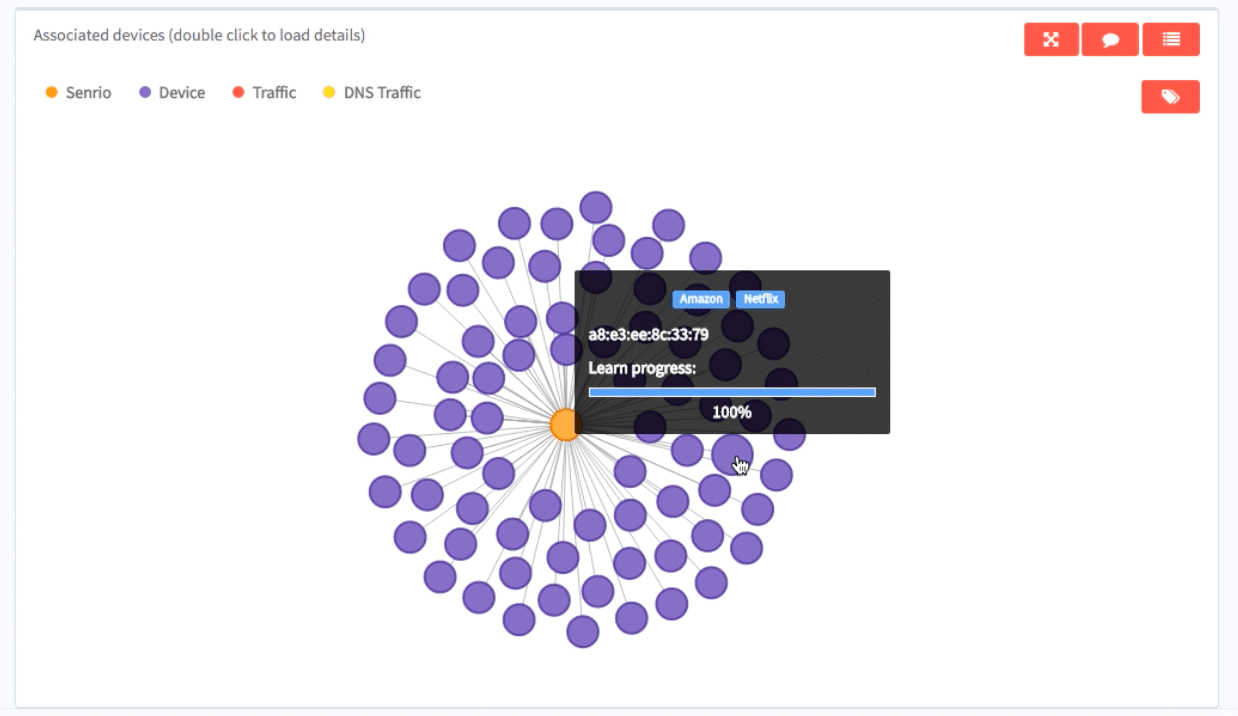
The Senrio technology operates from the premise that you have to be able to see and name the problem before you can go about addressing it. The company’s Sensors are deployed at network choke points and sniff out embedded systems, fingerprinting the device type, the operating system and so on to make it visible to IT security staff.
“We try to address all the ways a hacker would compromise a platform,” said Ridley. The data that Senrio Sensors collect is fed into a large machine learning system running on Amazon’s cloud that actually identifies what type of device it is. Senrio also does more in-depth analysis of the data, including traffic to and from the device, patterns of activity, destination and source IP addresses, and so on. The goal is to build a behavior pattern for the device so that deviations or anomalies in its behavior can be noted.
The RPM device that Ridley and his team analyzed, sold by a firm called SynAccess, was a great example of the kind of embedded device that bedevils corporate IT.
“It’s the kind of thing where maybe a couple of guys in the organization use it. It’s just some device way off in a data center that is doing something strange,” Ridley told Security Ledger. But those kinds of use cases are surprisingly common: healthcare networks, manufacturing and retail all have lots of endpoints that don’t look like “traditional” IT assets: they’re running proprietary software, one of the many real-time operating systems (RTOS) or an embedded form of Linux. They’re talking funny protocols and listening on funny ports.
Senrio’s sensors build what Ridley describes as a “very terse behavioral profile” of each device, and then waits and watches for it to deviate from it. Data can be sent up to Splunk or other security dashboards for follow-up, he said.
“The big thing that we provide isn’t just security but operations,” Ridley said. In fact, one beta site testing the technology was able to spot a subtle problem with earthquake sensors that were having trouble syncing up with a central control server.
And, while machine learning technology has its limits, especially monitoring general purpose systems, the technology works quite well for single-purpose endpoints, like embedded devices, where user interaction is rare and the scope of acceptable behaviors is much smaller, Ridley said.
Senrio is currently supporting several enterprise customers through evaluation and API integration. The company has closed its first round of financing led by Talis Capital, a London-based VC.
As we noted recently, security firms are gearing up to address security and privacy concerns engendered by the Internet of Things. That’s especially true in hot markets like automobiles and connected vehicles.

Pingback: Qadium Reaps $20M Venture Round For IoT Device Search Engine | The Security Ledger