In-brief: A new study by BitDefender suggests that security lapses dampen the appeal of smart home appliances and could (literally) open the door to burglars.
Smart technology is already available for homes in a wide array of forms. And analysts predict that the number of smart, connected devices will continue to grow at a fast rate in the coming years. For example, estimates from Gartner show that 2016 will see about 1.5 billion more smart things installed compared to 2015.
However, reports from researchers showcasing inherent security risks in such gadgets continue to pour in. Whether it’s a light bulb, an alarm system, a thermostat, a printer, a window shade, a doorbell or a door lock, judging from the recent news, it is likely that they can fall under the control of someone else than their owner.
In March, for example, we wrote about Matthew Garrett, a security researcher who managed to hack into the lighting system of a hotel that had replaced the classic light switches with digital controls. By the time he was done poking around, Garrett could turn on or off the lights in every room.
Garrett’s investigation was spur of the moment, and just for fun. But IoT devices can lead to greater risks than impossibility to control the lights. Online access to a poorly protected management panel for a home security system could translate into a home invasion incident; a hacked thermostat could deprive the house of heating in the cold days.
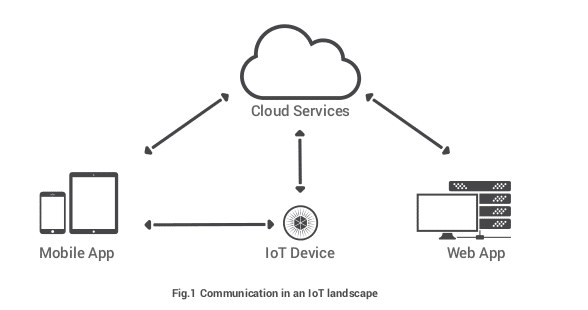
The security company Bitdefender has been delving into IoT and has published a new case study on four common IoT platforms. Among its conclusions: authentication features for such devices are inadequate. That means an intruder in close proximity of the wireless connection would not have to put in too much of an effort to compromise the home’s WiFi network. Once in, they could wreak havoc by taking control of the router and all devices behind it.
The list of tested gadgets included Belkin’s WeMo switch (disrupts/enables power to any device connected to it), a Lifx Bulb (smart LED with built-in WiFi), a GELink hub (allows lighting automation and operating bulbs individually or in groups), and Muzo Cobblestone WiFi audio receiver.
The researchers at Bitdefender needed about a month of testing to discover and exploit vulnerable protocols, design flaws, insecure data communication and unprotected hotspots, which ultimately gave them the keys to the WiFi kingdom, said a company representative via email. All of the smart devices studied are managed via a corresponding mobile application – a common characteristic of smart home devices.
Some of the problems identified were in areas that have been singled out before. Among them: insecure protocols. Bitdefender Labs researchers found that the UPnP compatible WeMo switch communicates with its smartphone application without authentication. When the hotspot is configured, everything is transmitted in plain text except for the password.
However, the passwords is weakly encrypted with a 128-bit AES algorithm, while the Wi-Fi password is encrypted with a key AES derived from the MAC address and the device ID. Since the device ID and MAC address are transmitted prior to the encrypted password, researchers had all the elements needed to decrypt the password.
“Sending data in clear text is a rookie mistake. However, while today’s encryption protocols are robust, they require high computing platforms, a resource that may not exist in all IoT-attached devices. But this is in no way an excuse to avoid encryption,” the report says.
Also: the WeMo switch and GELink hub initially connect to a hotspot that doesn’t require authentication. This allowed the security researchers to create a fake hotspot for the mobile app to connect to and intercept the communication.
From the four gadgets evaluated, the Lifx Bulb seems to be the toughest to crack because it relies on built-in WiFi capability for manipulation, and the vulnerable hotspot is available only in the initial configuration stage. Once the credentials for the WiFi network are received, Lifx bulb terminates the hotspot.
The researchers found a way into the wireless network, though. They found that by cutting the power to the device repeatedly at a frequency of one or two seconds, Lifx bulb’s configuration is reset and the user has to re-register the smart LED. Once again, experts reached their goal by impersonating the bulb’s hotspot.
Users streaming music with the help of Muzo Cobblestone audio receiver also run the risk of getting their home network compromised since setting up the device starts an unencrypted hotspot that remains active. It can be protected with a password, Bitdefender says, but this is not explicitly advertised to the user.
Additionally, the receiver includes a Telnet service for remote administration. “Our researchers tried basic password brute-forcing and observed that the initial credentials of the service were admin/ admin. Since the device is connected both to its hotspot and to the home Wi-Fi, it’s fairly easy to find and grab the files where Wi-Fi credentials are stored,” reads the paper.
Bitdefender notified the vendors of the products of the security faults they discovered and allowed patching time of at least 30 days before publicly disclosing the vulnerabilities.
According to the security company, out of the four devices, only in the case of Muzo Cobblestone some risks were mitigated (the hotspot no longer stays active, but the telnet service is still present for remote control), while the status of the others remained unchanged.
Despite consumers rapidly adopting IoT, the comfort they bring should not be placed above security features. Currently, it is the other way around.
Hopefully, pressure from the security community along with customers demanding safer devices will force manufacturers to implement safer ways to deliver IoT benefits in the near future.
