In-brief: A BBC article profiles an information security expert who finds herself the bearer of an implanted pacemaker, raising issues about the risks and benefits of new, connected health devices.
Just as the U.S. Food and Drug Administration (FDA) announces plans for a workshop to discuss collaborative approaches to medical device security (more on that as it approaches), the BBC is running an interesting piece on medical device hacking. There’s been a lot written on the topic – including in these pages – but the BBC article is useful for focusing on the feelings of an end-user. In this case, that end-user is Marie Moe, an information security expert who had previously worked with the Norwegian CERT.
No novice, Moe took a keen interest in the workings of the pacemaker implanted in her chest. From the article:
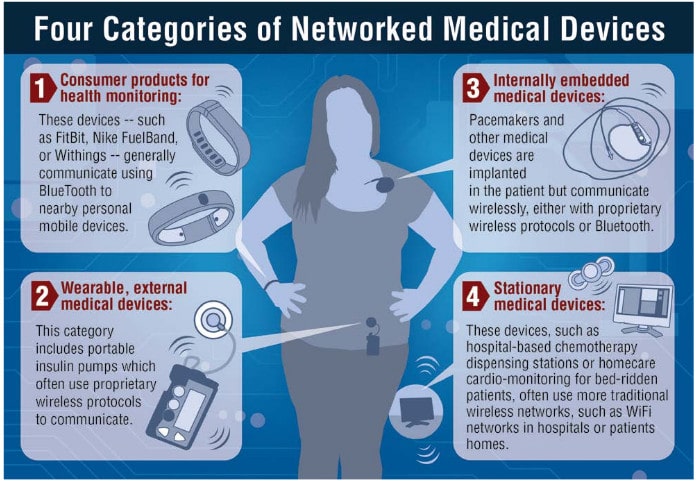
“When Marie first had her pacemaker fitted she downloaded the manuals. She discovered it had not one, but two wireless interfaces.
One enables doctors to adjust the pacemaker’s settings via a near-field link. Another, slightly longer-range, connection lets the device share data logs via the internet.
Hearts are now part of the Internet of Things, she realised.”
The article notes the work of Barnaby Jack and quotes Kevin Fu of the University of Michigan, a noted expert on the security of medical devices. It also does a good job of noting the conundrum medical professionals are in when it comes to connected medical devices, which promise to revolutionize treatment. From the article:
“(Cardiologist) Andrew Grace says the devices are ‘transformative’; if you need one, he and Marie agree, you shouldn’t be put off by colourful cyber-assassination tales in TV dramas. But that doesn’t mean security isn’t important.
…Andrew’s colleague, cardiologist Simon Hansom believes security has to be a priority. The wireless aspect – “being able to monitor people in their own homes, get up-to-the-minute checks on the devices” – is very useful, Mr Hansom says, but the security needs to be right first time.
Source: Could hackers break my heart via my pacemaker? – BBC News

Just waiting for the first reported case of cyber-murder. Not a matter of IF, but rather WHEN.
To put this all in context, this is simply a consequence of the IoT land-grab that is going on in the market right now. Folks are more worried about getting things working than that they should have security built in. A lot of that comes from the VC’s and the organizations themselves, who are firstly only interested in getting to revenue.
Every year Gartner does an update of their Hype Cycle — where new ideas start from a Technological Trigger, soar to the Peak of Inflated Expectations, plunge into the Trough of Disillusionment, until folks ditch the inappropriate uses & get the right uses and implementations to climb the Slope of Enlightenment to the Plateau of Productivity.
For the last two years, Gartner has pegged IoT to the Peak, and we’re looking down a steep slope of Disillusionment ahead of us. A lot of that disillusionment is headed our way precisely because we haven’t put the basic requirements in place for cyber-security: 1) Harden the Device, 2) Secure the Comms, and 3) Monitor and Manage the security constantly.
If you do nothing else make sure that your IoT device is hardened with Secure Boot, Immutable ID, Whitelisting, and signed SW/FW. That is if you don’t want to be the next Jeep or Barbie, or accessory to the first cyber-murder.