A mysterious piece of software, dubbed Wifatch, has been infecting tens of thousands of Linux-based home routers and, according to experts at Symantec, attempts to secure them from attack. But Wifatch’s benevolent intentions shouldn’t obscure its malicious actions, or the security problems that it takes advantage of.
The malicious software runs on vulnerable, Linux-based home routers. There, it removes other malware infections, disables vulnerable services like Telnet and even prompts users to update their administrator user name and password to prevent compromise, according to a post on Symantec’s blog. But the malware is still spreading between vulnerable systems without the owners consent and could easily be pressed into service distributing spam or malicious software, experts note.
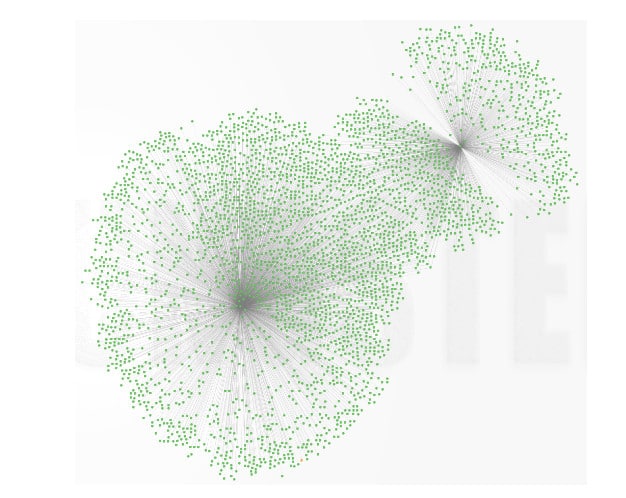
According to Symantec, Wifatch is likely spreading between infected devices by targeting exposed Telnet interfaces and using brute force password attacks to gain access to the devices. Tens of thousands of devices may have been infected globally.
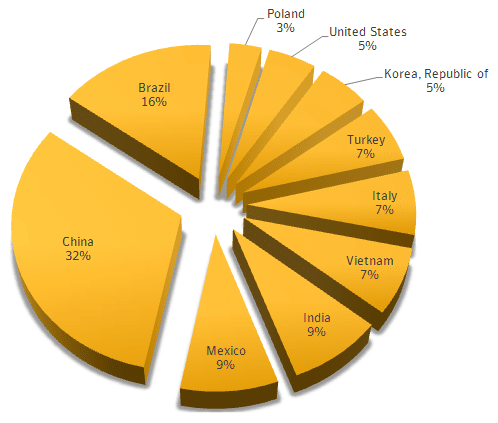
Symantec said that home and small office routers with ARM architectures make up the bulk of infected devices, but that devices running MIPS and SH4 were also identified, and PowerPC and X86 devices in much smaller numbers.
The bigger picture is that Wifatch is more evidence that unmanaged and Internet-connected embedded systems such as home broadband routers are an increasingly interesting target to malicious actors. Vigilantism like Wifatch, while more palatable than malicious attacks, simply underscores the challenges of securing a population of millions of embedded systems that power home networks and small offices.
According to the blog L00t Myself, the malware was first discovered lurking on home routers in November of 2014. Described as an “undetected, maybe unknown family of malware, quite complex and using advanced techniques to avoid disassembly and emulation,” Wifatch was written in PERL and designed to spread between vulnerable home routers and other embedded systems.
Like other botnets, Wifatch communicated via common sites like Pastebin, and allowed nodes within the botnet to communicate back to a command and control platform. It didn’t attract much attention until Symantec began studying it earlier this year as part of a renewed company focus on threats to embedded systems and “Internet of Things” platforms.
However, after closer study, Wifatch started to stick out, notably for efforts to secure the devices it was running on, rather than ravage them. Symantec noted that Wifatch’s code “does not ship any payloads used for malicious activities,” such as conducting spam campaigns or denial of service attacks. “In fact all the hardcoded routines seem to have been implemented in order to harden compromised devices,” Symantec notes in a blog post. After monitoring Wifatch over a period of months, Symantec said it had yet to observe “any malicious actions being carried out through it.” To the contrary: Wifatch took steps to improve the security of the devices it ran on – killing processes linked to known malware and disabling Telnet access to the devices (a common avenue of compromise). Administrators were prompted to change their passwords and update the firmware.
So – a good thing? Not really. In fact, software vigilantism raises the same practical and ethical dilemmas as real-world vigilantism. Namely: it doesn’t really solve the underlying problem (insecurity) and comes with a host of thorny problems about where to draw the line between benevolent and malicious actions.
This isn’t exactly a new problem. In 2004, for example, Lycos Europe was forced to withdraw an anti-spam screen saver application, “Make Love Not Spam,” which targeted known spammer websites with traffic requests in what many Internet Service Providers considered a denial of service attack.
In each case, the vigilantism is more symptom than cause: an aspirational attempt to “do something” about what everyone recognizes is a big and unsolved problem. In the case of Wifatch, of course, that problem is insecure embedded systems – not just home wifi routers, but embedded systems of all types.
Incidents like the disclosure of the Misfortune Cookie vulnerability have revealed the dismal state of embedded system security, in which outdated and insecure firmware can persist for years – if not decades. Security firms including Team Cymru and IOActive have also highlighted the problem of insecure SOHO wireless routers, which are increasingly the targets of malware and other attacks.
Still, there’s been little progress. And, with home Internet hubs set to become the gateway to more populated networks of appliances, smart home devices and traditional endpoints, the continued insecurity of the underlying hardware and software is a growing concern.
Rather than take their chances with the current generation of insecure infrastructure, vendors like Google are considering an end run around outdated devices. In August, for example, Google introduced OnHub, its own home router that is designed to make home routers more powerful and easier to manage – and therefore more secure.
